GotaTun Security Audit Finds No Major Issues, Minor Fixes Made
- GotaTun security audit findings: Independent review found no major vulnerabilities in GotaTun v0.2.0 during January–February 2026 security assessment.
- Low-severity issues identified: Audit highlighted predictable session identifiers and incorrect packet padding; both fixed to align with WireGuard specification.
- Future rollout plans: Updated GotaTun v0.4.0 includes fixes, with wider deployment across remaining platforms planned throughout 2026.
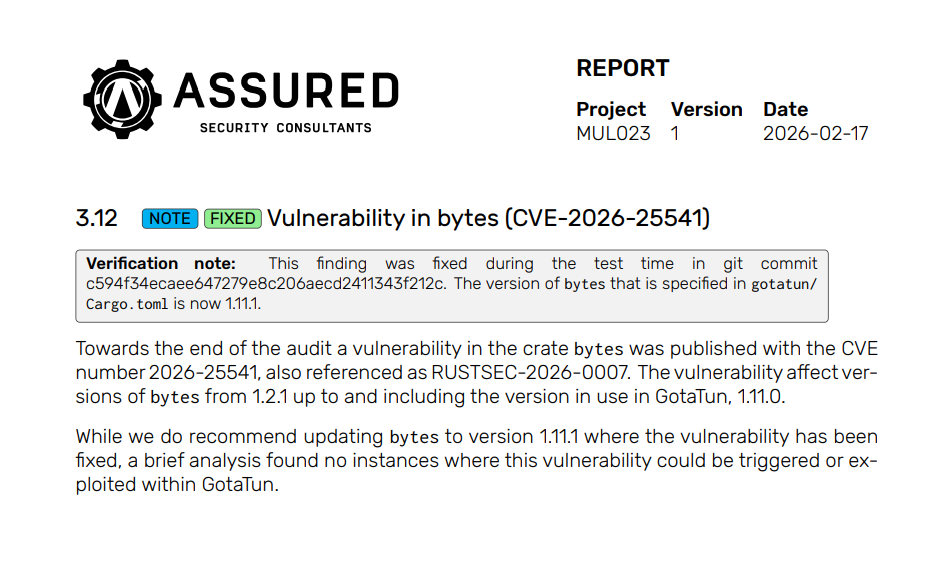
A new independent security audit has reviewed GotaTun, the WireGuard implementation currently used in Mullvad’s Android app, and found no major vulnerabilities. The review was conducted by Assured Security Consultants and covered version 0.2.0 of the software.
The audit took place between January 19 and February 15, 2026. It evaluated the core components of GotaTun but did not include DAITA, the GotaTun CLI, or any external dependencies. While the assessment confirmed the absence of critical security flaws, auditors did identify two low-severity issues and several additional notes related to the implementation.
Most of the recommended improvements have already been addressed before the audit report was published.
Independent Audit Finds No Major Security Flaws
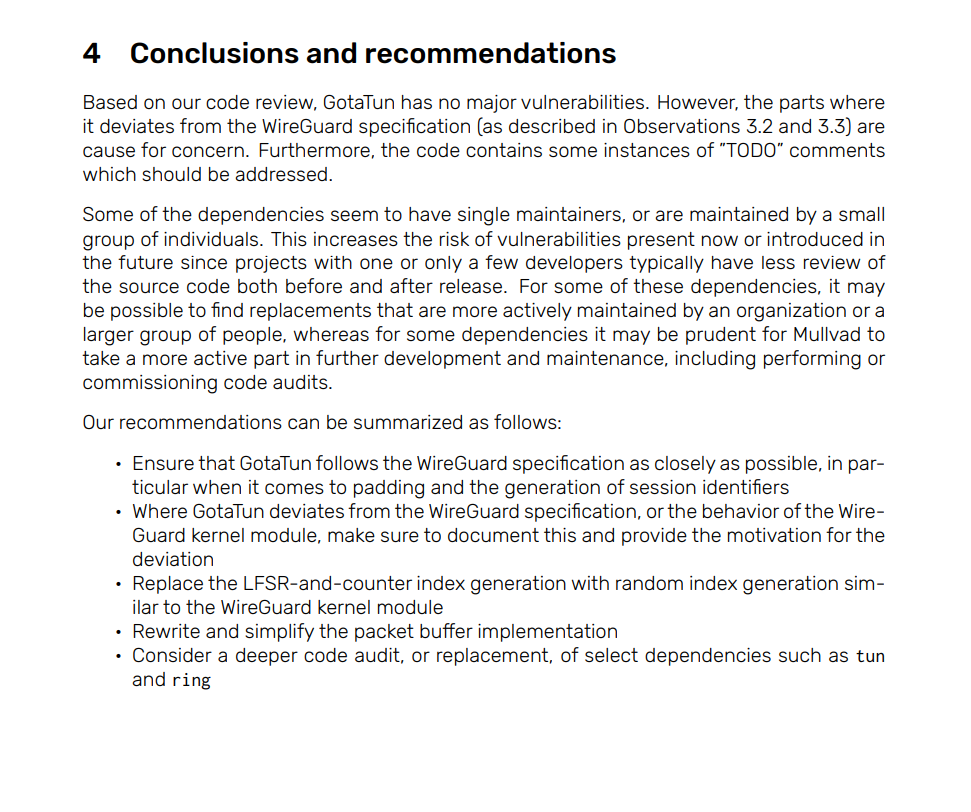
According to the findings from Assured Security Consultants, the overall codebase of GotaTun did not show any major vulnerabilities. However, the auditors highlighted areas where the implementation differed from the official WireGuard specification.
The report also pointed out the presence of several “TODO” comments in the code, suggesting that some areas still required attention or further development. While these comments did not indicate immediate security risks, the auditors recommended addressing them in future updates.
Mullvad confirmed that several of the issues raised in the report were fixed before the audit results were made public. These include patches for both low-severity findings and some informational notes. The remaining observations were reviewed but considered non-urgent.
Low-Severity Issues Related to Session Identifiers and Packet Padding
One of the low-severity issues involved how GotaTun generated peer session identifiers. In version 0.2.0, 24 bits of the identifier remained static for a specific peer, while the remaining 8 bits functioned as a predictable counter that increased with each new session, typically every two minutes.
This behavior differed from the WireGuard specification, which recommends generating a fully random 32-bit integer for each session. The design originally came from BoringTun, another WireGuard implementation. Auditors noted that this setup would likely reveal very little to passive observers, potentially only indicating the number of connection handshakes or active peers.
Even though the risk was limited, the developers updated the code to follow the WireGuard specification and ensure session identifiers are generated randomly.
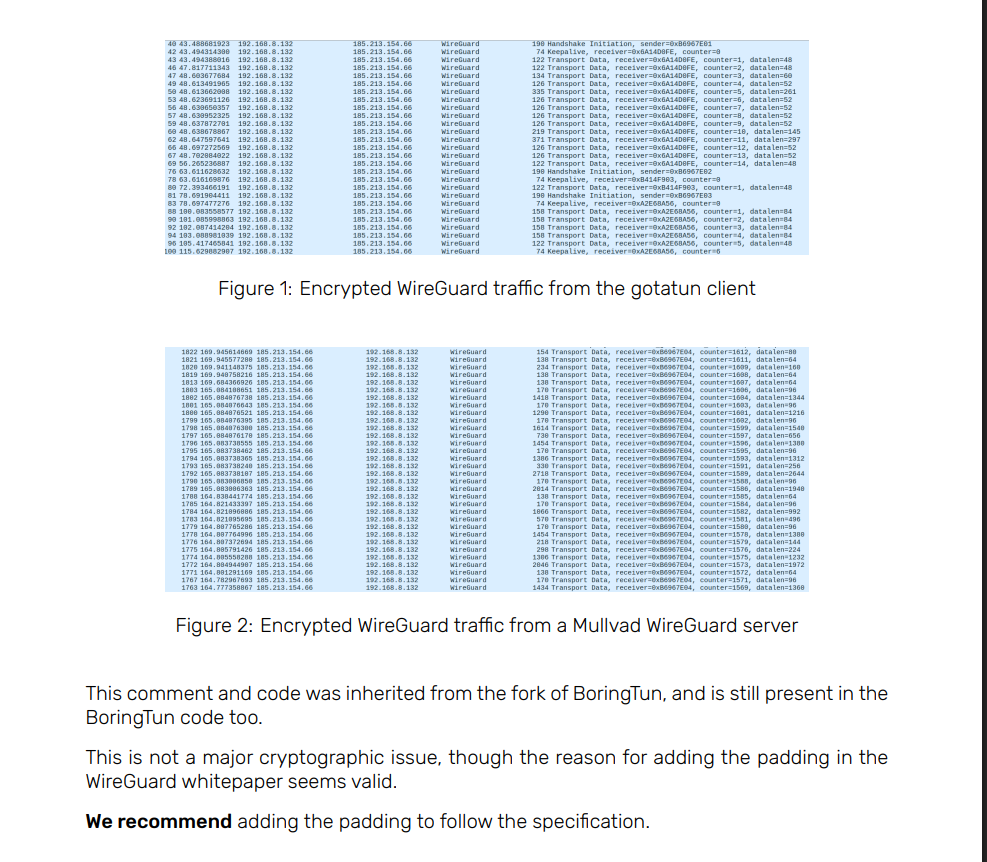
Another issue involved packet padding. WireGuard specifies that packets should be padded before encryption so their length is divisible by 16. GotaTun’s code included a comment indicating this step had not yet been implemented. The developers have since updated the software so that payloads are always padded before encryption. This change also slightly improves resistance to traffic analysis.
Peer Roaming Behavior Noted in Audit
The audit also documented a functional issue related to peer roaming. If a peer’s IP address changed during a session, GotaTun did not always begin sending packets to the new address. As a result, the implementation did not correctly handle roaming peers.
According to Mullvad, this limitation did not affect its VPN service because its VPN servers do not change IP addresses during an active WireGuard session. However, the company still considered the issue important for broader use cases and fixed it to make GotaTun more suitable as a general-purpose WireGuard implementation.
Future Rollout Planned After Audit Completion
The fixes mentioned in the report are now available starting with GotaTun version 0.4.0. Upcoming releases of the company’s apps will automatically begin using the updated implementation.
GotaTun was first introduced in Mullvad’s Android app last year, where it delivered promising results. With the security audit completed, the company says it now has greater confidence in the implementation and plans to expand GotaTun to its remaining platforms during 2026.