Vishing Scams Are Surging as Companies Shift to Remote Work
- Working remotely goes hand in hand with tech support scammers and vishing actors.
- The number of crooks calling people who are working from home is exploding right now.
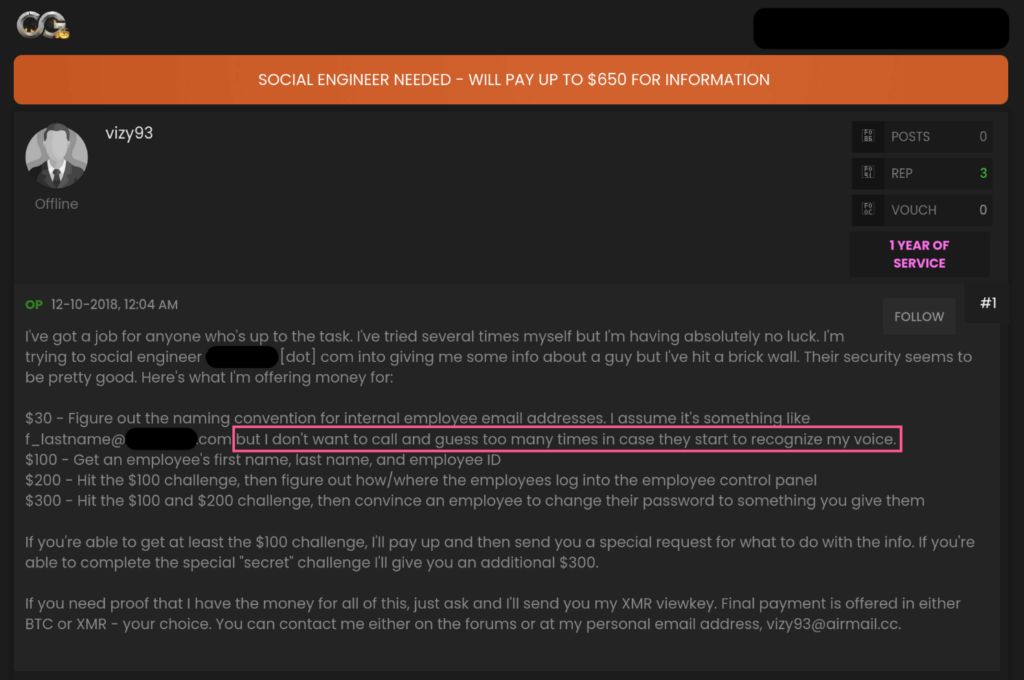
- In many cases, native English speakers are contracted to make fraudulent calls.
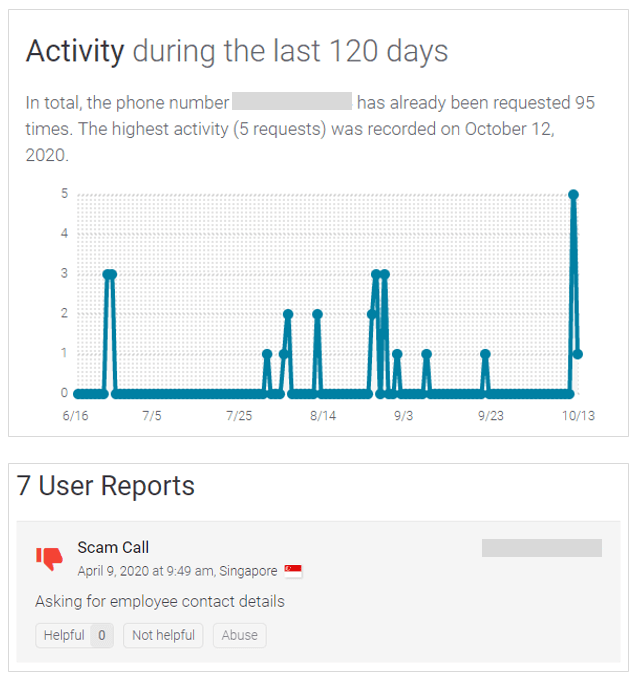
Voice phishing through phone calls is going rampant right now, and the FBI is warning companies and their employees to remain vigilant. Hackers are locating high-ranking individuals on LinkedIn and other social media platforms, and then proceed to trick them via calls.
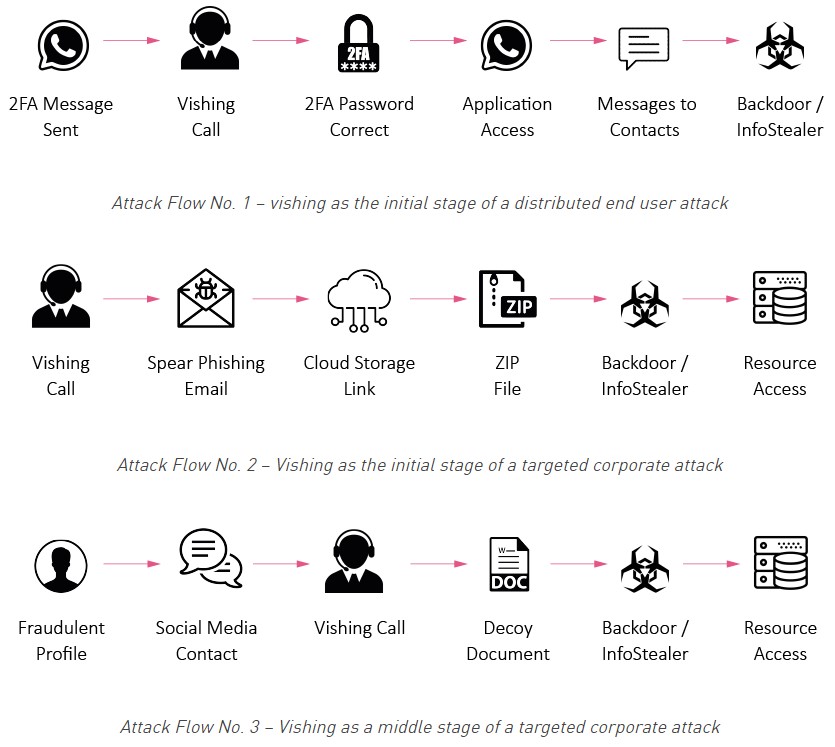
The actors' goal is to convince the targeted individuals to divulge their remote access credentials and then use these details to log in to the company’s network.
About four out of five enterprises have adopted mass remote working for their employees, and three out of four are planning to keep it that way indefinitely. Crooks are naturally turning their attention to this shift, deploying both new and old tricks to phish credentials from employees who are now isolated and more vulnerable.
As for the origin of the attacks, this is literally all over the place, ranging from small and inexperienced cyber-criminals to highly sophisticated state-supported APT groups.
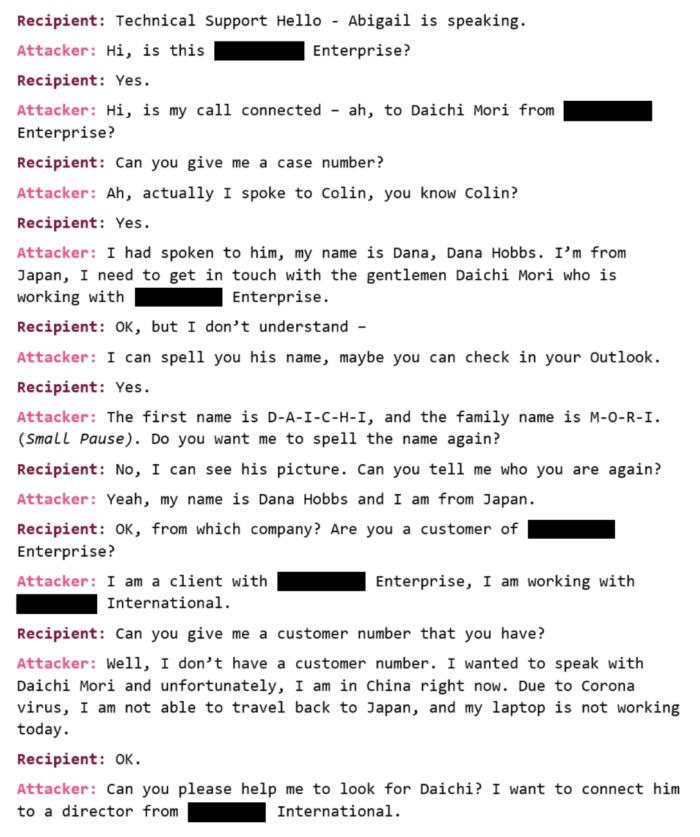
The theme used by the actors is most often “tech-support,” as this sets the stage to ask for credentials without making it look suspicious. In some cases, the victims see a pop-up alert on their computer and are convinced to install a RAT (remote access tool), making the hackers’ job even easier.
In other cases, the hackers call the victim and request the 2FA code that they just received, pretending to be a support representative in the process of fixing a problem for the customer. The crooks then use this code to access the victim’s email, IM, or banking account.
New hires sent to work from home are a category on their own, as they didn’t have enough time to get trained against vishing threats. Again, LinkedIn offers this valuable information to the attackers, who call the new employees pretending to be a colleague in need of assistance with VPN access. The hackers use real names of other employees of the company to convince the target, and oftentimes, they do.
The problem of presenting convincing oral communication in English is covered by hiring native speakers who are offering this kind of service. These people charge a couple of hundreds of dollars to perform the calls using a pre-written script, and some of them even undertake the reconnaissance part of the vishing operation.
When someone calls you and pretends to be from the company you’re working for, ask for their number to call them back and confirm it with the firm’s employee database. If they stutter or claim technical problems, just hang up. They will probably give up trying to phish you specifically, but reporting this incident to the company is key to protect colleagues as well.