Researchers Find 19 Petabytes of Data Exposed Online and Accessible by Anyone
- There is enough exposed data out there to fill tens of thousands of high-capacity hard drives.
- It appears that Chinese admins using Hadoop is the worst combination in data security.
- There is an alarming number of databases that seem to have been totally abandoned.
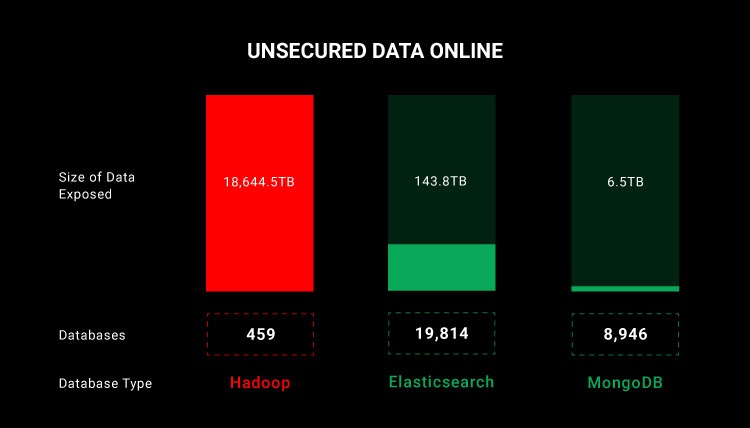
Researchers of the CyberNews team led by E. Mikalauskas have carried out a large-scale scan on the web to find out how much data lies unprotected and publicly accessible out there. According to their findings, there are over 29,000 databases exposed online and improperly secured, holding 19,000 terabytes of data. That’s 19 petabytes, which is a mind-boggling figure no matter how you see it.
The researchers used specialized search engines to find MongoDB, Elasticsearch, and Hadoop databases. While these three are very popular, this means there are more exposed databases of other types not covered in this report. Among the three, the least problematic is MongoDB. Elasticsearch has the largest number of exposed incidents, and Hadoop has the largest volumes of exposed data.
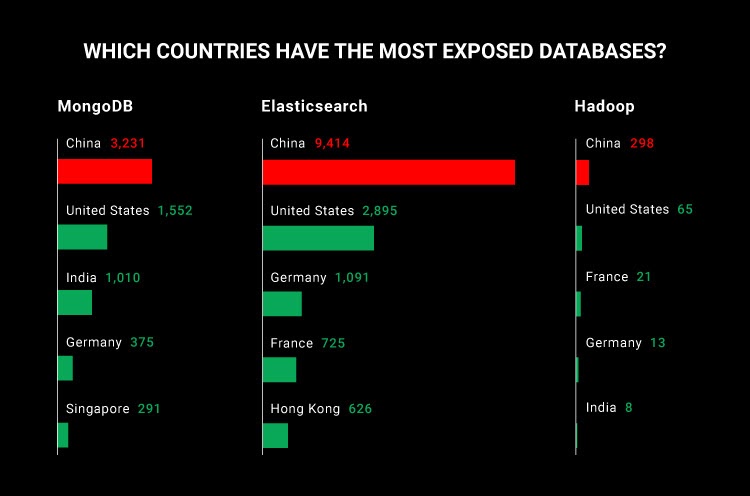
As for the countries where the most unprotected databases are hosted, it looks that Chinese admins are the most negligent, probably because they rarely have to face repercussions in the case of data leaks. In fact, data security and privacy in China are at a very different level compared to the rest of the world, and simply put, people there don’t care much about data safety.
The countries that follow China - probably due to the number of firms operating there, which inevitably holds a portion of misconfigurations - are the United States, India, Germany, and France.
The researchers also explored the effects of “Meow” in the landscape, which is a database wiping bot that has been mysteriously doing its thing for over a year now. The team found 59 databases hit by Meow attacks a year ago and still are online, exposed, and holding 12.5 GB of data. These appear to be totally abandoned databases whose admins have left them prey online for whatever reason.
Securing a database should start by adding an authentication step for accessing it, and while this sounds elementary, it remains the primary source of trouble. Apart from that, admins should enable encryption and use a VPN when they access the database so that even if the data is leaked or intercepted, the actor won’t get anything useful.
And finally, updating the database software and applying the latest security updates should be a standard security practice for all admins.