“Meow” Attacks Are Again Wiping all Indexed Unsecured Databases
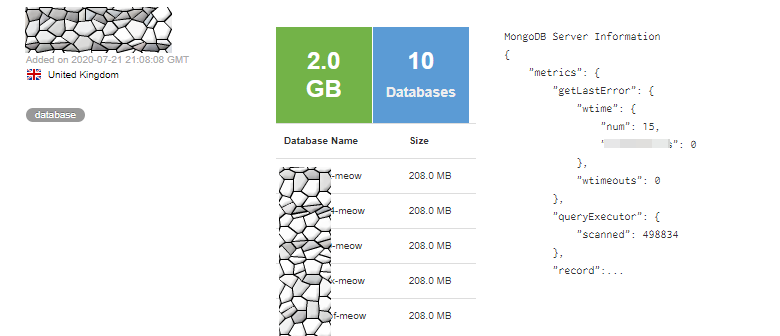
- Dozens of unsecured MongoDB instances are located by “Meow” bots and wiped or overwritten.
- The databases are essentially destroyed, but no specific reasons, goals, or explanations are provided.
- “Meow” could be the work of well-intended researchers, or actors trying to hide their tracks.
Someone is back to targeting unprotected databases indexed in Shodan and BinaryEdge, wiping their contents and giving no explanations whatsoever. This peculiar type of attack is named “Meow,” and researchers are baffled as to what the goal is. We see these wipes happen in waves every once in a while, and it looks like we’re going through yet another wave right now.
According to the Bleeping Computer, there are already dozens of indexed unprotected databases that have been wiped by “Meow,” with one notable example being the exposed database of the Hong Kong-based VPNs that we covered last week.
Meow involves running a scanning bot, which locates unprotected instances and then either deletes all data or overwrites it. There are no ransom notes, no threats delivered, and no explanations given. This leaves much margin for speculation, and there are quite a lot of possible scenarios that sound realistic or plausible.
Some suggest that this is the work of well-intended actors trying to teach admins a lesson in security. Others like to believe that an international agency is actively disrupting data sellers’ malicious operations and the associated dark web markets, effectively closing the tap.
Source: Bleeping Computer
Another idea lying on the opposite side is that “Meow” attacks are meant to obstruct researchers from discovering valuable information. Potentially, “Meow” actors may engage in exfiltrating the data and wiping the target database to hide their tracks and make it impossible for researchers to figure out what happened, who was affected, and who is responsible for the attack. This makes sense, but it’s all part of the speculation, so nothing can be told with certainty.
What is for sure is that the operation of the entities that have their databases wiped is disrupted, especially when those databases are live systems and not just misconfigured backups. Administrators should finally follow secure practices and pay attention to the ElasticSearch configuration details, and if the Meow attacks serve as a force pushing to that direction, so be it.
Automation is coming more and more into play this year, and all kinds of bots quickly locate databases that are publicly indexed. In the end, Meow is just a demonstration of what’s possible, and what’s possible is also probable. Many people are doing things just because they can, so there isn’t always a reasonable explanation behind everything.
Read More:
- How Long Does It Take for Actors to Find an Unsecured Database?
- Owners of Unprotected MongoDB Databases Now Facing Unusual Extortion