Microsoft Says ‘NOBELIUM’ Hackers Are Still Actively Targeting American Firms
- Supply chain actors are still out there, targeting American IT firms and governmental entities.
- This is still going on despite the efforts that are being made at the highest political level.
- ‘NOBELIUM’ continues to evolve its techniques, rotate attack methods, and trying out all possible ways in.
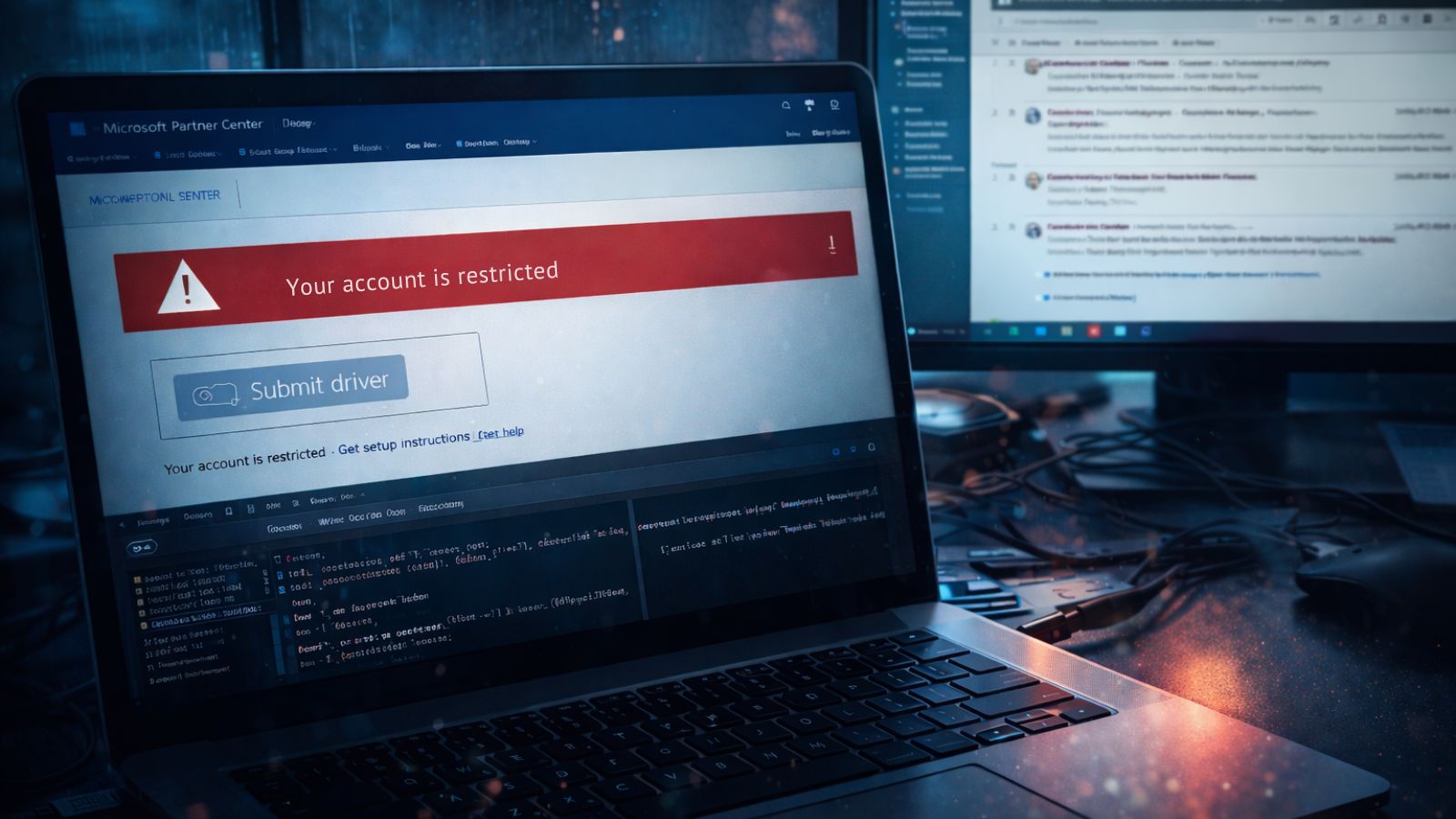
The Microsoft Threat Intelligence Center is reporting about new activity coming from ‘NOBELIUM,’ a group of hackers that has been linked with the catastrophic SolarWinds attacks discovered last December. This is quite notable because earlier in the month, U.S. President Joe Biden met with Russia’s President Vladimir Putin, and they appeared to have reached an agreement to de-escalate cyberattacks. ‘NOBELIUM’ has been confirmed (by American intelligence) as a state-supported actor, so seeing them continue their operations is going against whatever agreement the two forces reached recently.
Microsoft clarifies that the recent activity was mostly unsuccessful, as the nation-level notification system is now fully operational and produces very positive results. The majority of the targets (57%) are active in the IT sector, where the actors could be seeking a new opportunity to plant a backdoor and achieve a widespread supply chain infection. In 20% of the cases, the hackers targeted government entities directly, while the remaining percentage concerns financial institutes, non-governmental organizations, and think tanks.
One of the methods followed by ‘NOBELIUM’ involves deploying info-stealing malware, which attempts to gain access to a basic account like that of a Microsoft customer support agent. From there, the actors broaden the spectrum and increase the targeting sophistication by launching more tailored attacks. In most cases, Microsoft was able to detect this activity and alert the impacted customers, helping them keep their systems secure. As the software firm points out, enabling 2FA to protect these accounts remains key in defending against take-over attacks.
A month ago, we reported about ‘NOBELIUM’ operating large-scale phishing campaigns targeting American companies en masse, some of which managed to find their way into valuable corporate systems and networks. It is now clear that the Russian hackers aren’t going to stop, so every potential target must take all security precautions possible to prevent risky intrusions and generally follow a “Zero Trust” architecture.
This doesn’t apply only to American firms through, as ‘NOBELIUM’ has been confirmed to have targeted a total of 36 countries in the past few months. 45% of the attacks were focused on U.S.-based firms, but the UK, Germany, and Canada also had notable percentages.