Ex-NSA Hacker Reveals Another Zoom Flow – Affecting macOS Users’ Webcam and Microphone
- A researcher unveils two zero-day flaws that concern the macOS version of Zoom, the digital meetings app.
- The first bug makes privilege escalation possible, while the second can share the microphone and webcam access.
- Both exploits happen silently, without user prompts or interaction or any indication of what's going on.
It seems like there’s no end to the revelations that concern Zoom's security flaws, one of the currently most popular video-conferencing applications out there. The software unlawfully shared user data with Facebook and leaked people’s email addresses and photos to complete strangers. Moreover, Zoom can leak Windows login credentials to hackers, and it is making false claims about end-to-end encryption tricking high-profile individuals into trusting it. And now, on top of all that, a former NSA hacker named Patrick Wardle reveals a way to exploit Zoom to access the user’s microphone and camera and record things arbitrarily.
Source: objective-see.com
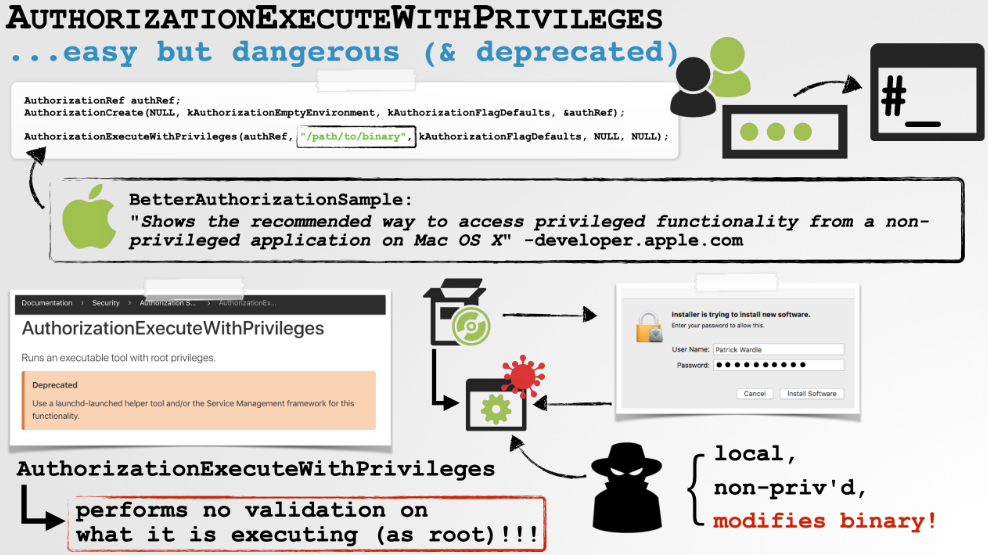
As Patrick Wardle explains, the attack is actually based on the exploitation of two specific bugs, and it must be launched locally. It means that the malicious person needs to have physical access to the target computer, which is quite hard in the days of self-isolation that we're currently going through. First, Zoom is using a set of installation scripts to unpack everything needed on macOS, without having to serve the users too many annoying dialog boxes. While this is convenient, it is also unsafe, as someone without root access to the system could potentially inject malicious code into the Zoom installer and automate a privilege escalation procedure.
Ever wondered how the @zoom_us macOS installer does it’s job without you ever clicking install? Turns out they (ab)use preinstallation scripts, manually unpack the app using a bundled 7zip and install it to /Applications if the current user is in the admin group (no root needed). pic.twitter.com/qgQ1XdU11M
— Felix (@c1truz_) March 30, 2020
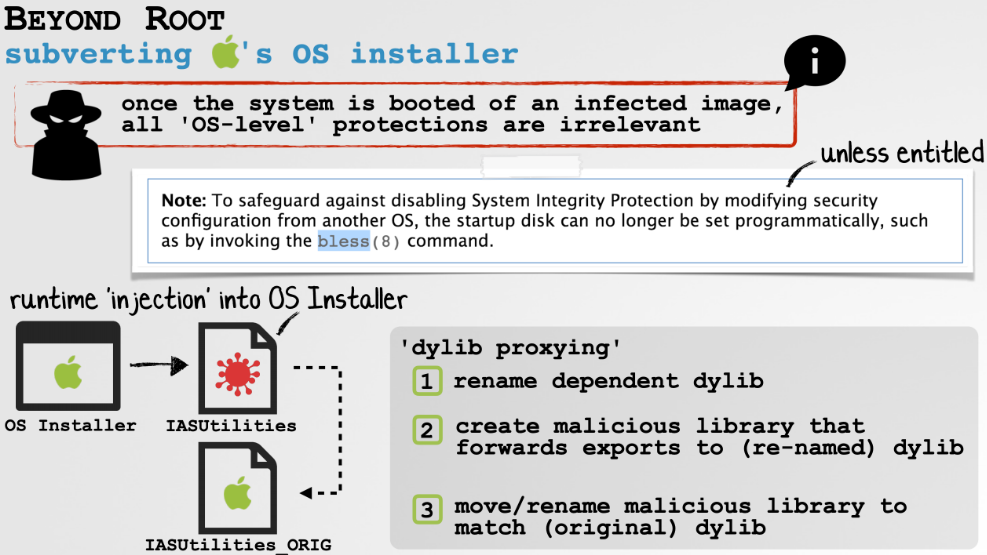
The second bug is based on the sharing of the Zoom access permissions with any other program, like malware or spyware that could be planted on the system by exploiting the first flaw. As Zoom has access to the user's webcam and microphone, someone could silently piggy-back this access without displaying a prompt to the user. The fault lies in the fact that Zoom allows malicious code to be injected into its process space, and the most worrying part of that is that the developers of the app have placed a specific exclusion to allow this.
Source: objective-see.com
Wardle concludes his write up by saying: “So, what to do? Honestly, if you care about your security and/or privacy, perhaps stop using Zoom.” While it's true that the scrutiny through which Zoom is going right now has yielded many things to worry about, it remains one of the best digital meeting tools in existence - it's free for up to one hundred participants, supports all platforms, is easy to set up and use, can maintain consistent HD video quality, and features a polished user interface. Just don't use it in critical situations, and make sure to employ any available updates immediately.