What Is a Smurf Attack?
A "smurf" attack doesn't have anything to do with those adorable blue cartoon people. Instead, it's a particular form of DDoS or Distributed Denial of Service attack. Smurf attacks are devastating and employ a very clever exploit that sets them apart from vanilla DDoS attacks.
To understand what makes a smurf attack special, we first need to look at the more mainstream form of this attack.
First, What's a DDoS Attack?
The internet consists of servers that contain data we all want to access, client devices such as the one you're using right now, and network equipment that lets them talk to each other.
Servers don't have an infinite capacity to serve data to client devices. They have limited bandwidth, processing power, and IO speed. This means that if a server can only serve 100 users at a time, the 101st user is denied service.
Normally that's not a problem these days. Massive data centers now offer the majority of hosting services. Modern server technology allows the server capacity to be scaled up quickly. Servers are also more powerful than ever, making it very unlikely that you will be denied service.
A DDoS attack rope in a massive number of client devices and makes them all try to access the same service at the same time. This artificial demand is usually of the magnitude of what would be possible on the worst day.
You can, in principle, just get a bunch of computers together and launch a DDOS. However, in practice, you can only have an effective DDoS attack by infecting other people's computers. These so-called "botnets" all wait for the command to attack, and then you can take down a Goliath using millions of Davids.
How a Smurf Attack Works
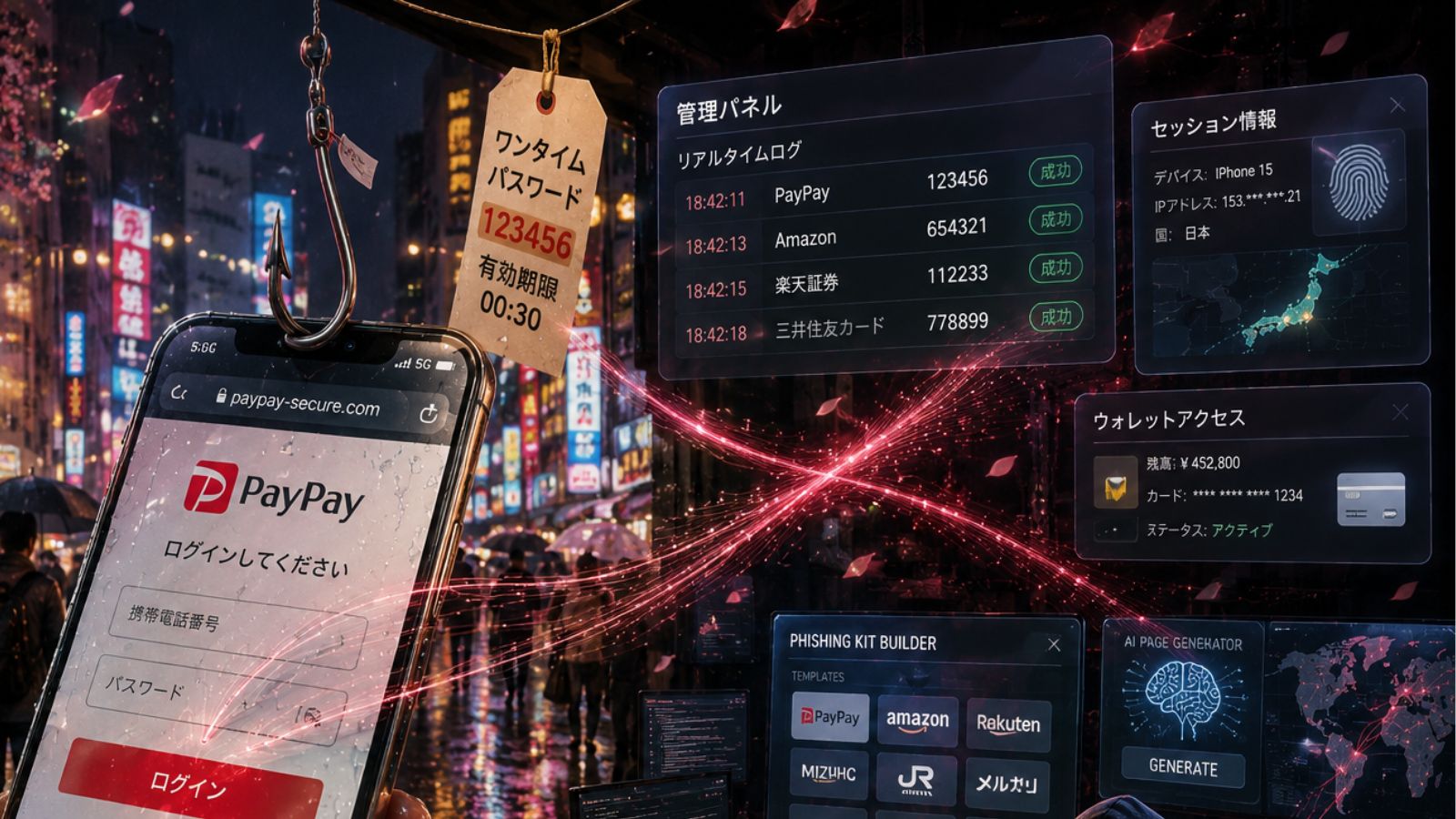
The end result of a smurf attack is the same as any DDoS attack. However, how it achieves and sustains the attack is the real genius part of the equation. It exploits a feature of networking technology called the ICMP - or Internal Control Message Protocol.
Smurf attack malware creates network packets with spoofed origin IP addresses. The packet has an ICMP message inside it, asking any device that receives it to send a ping back. When combined with a feature known as IP broadcasting, the pings begin to happen in an infinite loop, leading to what's effectively the network equivalent of a brain seizure.
This self-propagating storm of network packets grow exponentially and then clog up every piece of network hardware, not just servers that can't keep up. It's also an effective force multiplier since you don't need as many bots in your botnet to do it.
A Short History of the Smurf Attack
The earliest notable Smurf attack happened in 1998, targeting the University of Minnesota. It caused data loss and slow network speeds not just on the university campus network but across the entire state.
This attack caused an unprecedented 30% of packet loss, which means that nearly a third of packets sent out onto the network never made it to their destination. The first warning of such an attack being possible came in January of 1998 when the Computer Emergency Response Team issued an advisory about Smurf attacks.
Since this statewide internet disaster, there have been many new attacks and just as many new tactics and strategies to take the sting out of those pesky Smurfs.
Preventing Smurf Attacks
One of the biggest dangers of smurf attacks is that there is usually a long delay between the malware infection and the actual attack. That's because the attackers need to build up enough infected computers in their army to pull off an effective attack.
This is why many smurf attack trojans also have rootkits built into them. This lets the malware author open up a way for the system to send and receive commands. As you might imagine, it's therefore very important that computers have effective malware packages on them that prevent Smurf attack software from running in the first place.
In the end, however, it's up to the network engineers to build safeguards into the network itself. Modern firewalls and edge network devices can filter out malicious traffic. They can be set to ignore the types of compromised packets that would trigger a packet flood in the first place.
There also needs to be effective monitoring of network traffic to ensure that any weird behavior is detected and dealt with quickly. It can also help organizations buy scalable bandwidth and server capacity capable of dealing with short-term bursts in traffic caused by malicious attacks until they can be stopped.
Servers should also be spread out into different physical data centers and have redundancy so that if one does go down in a Smurf attack, there's no denial of service.
One Last Thing, Why Is It Called a "Smurf" Attack?
We almost forgot. Throughout this whole article, you've probably wondered why this type of attack has earned the nickname "Smurf" attack. At first, we thought it might be because the flood of internet packets might have been seen as an army of Smurfs, but the real story seems to be that the early exploit software used to perpetrate these attacks was simply called Smurf.
The package was apparently called this because the small packets caused big problems, just like the Smurfs in the cartoon. So maybe my first instinct wasn't that far off!
Smurf attacks aren't really something that end-users can do anything about or really need to understand on a precise technical level. We certainly don't! However, the next time you hear that service stopped working because of a flood, amplification, or "Smurf" attack, you'll know exactly what that means.