‘UC Browser’ Found to Be Peeking Into Its Users’ Activities Even When in Incognito
- ‘UC Browser’ is sending user browsing details to Alibaba’s and UCWeb’s servers even when in incognito mode.
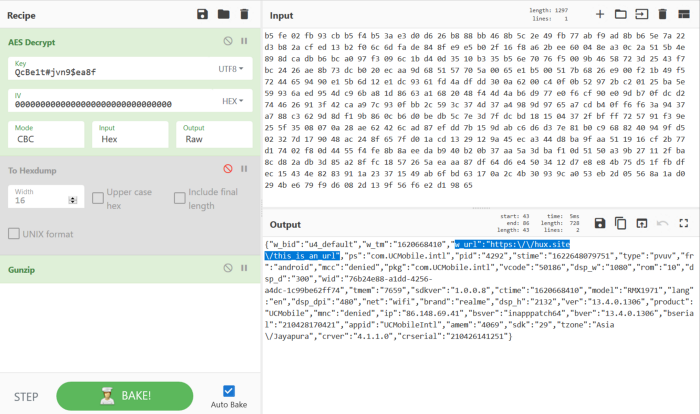
- The browser is doing so stealthily through encrypted requests and packs, but it happens on both Android and iOS.
- The browser app has disappeared suddenly from the App Store but is still available on the Play Store.
One thing that all web browsers have in common is the existence of an “incognito” browsing mode that promises not to keep any history or logs of what websites the user has visited through it. It doesn’t mean that your ISP won’t know about the sites you have visited, nor that certain websites won’t still try to track you around. Still, it at least comes with the assurance that the browser itself does not save browsing history, cookies, and information entered into forms. Not for UC Browser as it seems.
Alibaba’s web browser, which also happens to be pretty popular in China, is recording the users’ browsing history even when in incognito and sends the relevant reports to the project’s servers. To make this finding even worse, UCWeb, the developer of UC Browser, claims that this isn’t happening, so users are straight-out tricked into believing a false promise. And to complete this repugnant data handling approach, the same data also flies to Alibaba’s servers, so it ends up to two separate albeit connected entities.
So, could this be a mistake in the configuration or simply a non-intentionally introduced bug? As detailed by Gabi Cirlig, a researcher who reverse-engineered this data transaction system and figured out what is going on, this behavior is consistent in both Android and iOS, for which UC Browser is available, so it doesn’t look like an error in the development.
According to the researcher’s findings, the browser keeps on sending a data pack containing the visited URL, the IP address of the user, and a proprietary ID that is the persistent identifier to help with tracking even in the case of the user deploying a VPN tool.
The UC Browser app has suddenly disappeared from the App Store, and if it is to return there, it will need to declare what user data it plans to harvest during operation. Clearly, lying to users will not be acceptable to Apple. However, the app remains available in the Google Play Store - not sure for how long, though.
Back in March 2019, researchers of the Dr. Web Anti-Virus team discovered that UC Browser was fetching data through HTTP to update itself without prompting the user, risking MitM attacks and a host of other potential troubles. This didn’t stop the project from becoming the fourth most popular web browser in the world by 2021.