Three Fake Android Apps on the Google Play Store Are Essentially Adware
- Three Android adware apps that feature advanced concealment have amassed 30000 downloads.
- The apps have been removed now, but it looks like they turned to adware recently via an update.
- The ad feeding occurs every 15 minutes, while the referral code is refreshed every day.
Researchers from the BitDefender team have discovered three Android apps that have just been removed from the Google Play Store but already managed to trick a total of 30000 people into downloading them. The difference of the three culprit apps from the usual adware that one comes across on the Play Store is that they are very well hidden inside the devices they infect, and this also explains why it took two months for the first user reports to start flowing. Moreover, instead of pushing ads all the time, these three apps were only displaying full-screen ads every 15 minutes and only after 24 hours following their installation have passed, so there was no apparent source of the problem.
image source: labs.bitdefender.com
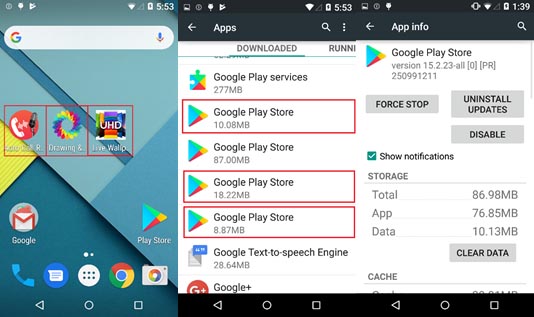
The apps are named “colors drawing coloring”, “hd4k wallpapers backgrounds”, and “launcher call recorder”. Upon their installation, however, these names are all replaced by “Google Play Store” on the “Apps” drawer, and their icons are also replaced by the associated icon. This way, users are further confused and the malicious apps are further protected from being located and eventually deleted. Another hiding method for the apps is to detect the status of the internet connection, and if there is one, to hide its icon.
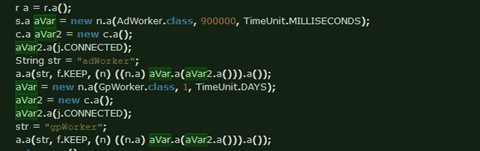
When the icons are there, the apps are working as intended/expected which is a sign that they were legitimate apps once, entering the Play Store as such. Three months ago, the apps turned rogue through an update, and they are now essentially adware, pushing overlay ads that promote other apps that look legit and not each other. It’s all done by setting GpWorker and AdWorker alarms, so the ad campaign referral code is re-fed to the device every 24 hours even if the user deletes it.
image source: labs.bitdefender.com
This story highlights the risk of apps that are already on your device, and may not have been posing any danger for a long time. Installing apps from untrustworthy developers always entail the risk of an app turning malware after a single update, so you should pay attention to what you’re doing and notice any strange differences in the behavior of your system after you have updated something. Finally, take a close look at the user reviews on the Play Store, and don’t hesitate to grab a good AV solution from a trusty vendor for the Android platform.
Do you have something to comment on the above? Feel free to do so in the dedicated section down below, or on our socials, on Facebook and Twitter.