Newly Discovered Adware Was Present in 182 Android Apps Since 2018
- Researchers discovered an ongoing adware campaign that first launched back in 2018.
- The campaign was supported by 182 free apps, mostly camera apps, photo editors, and games.
- Google managed to remove all but eight until today, while the remaining are available on other stores.
Researchers from the Trend Micro team have unveiled a new adware campaign that took its place inside the Google Play Store through 111 free-to-download apps. The adware-ridden apps are games, camera apps, photo editors, and more, exposing and underlining once again the inability of Google to keep adware and even malware-infected apps out of the official Android store. To be precise, the campaign uses 182 apps, 111 of these were available in the Play Store, while the others were to be found in the 9Apps and the PP Assistant stores.
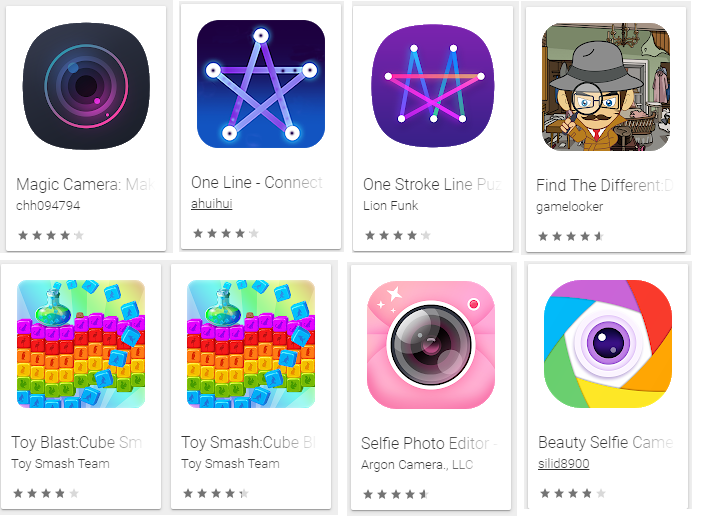
Out of the 111 adware apps, the 68 were duplicates and the remaining were unique. Based on the features, code characteristics, publishing times, packaging methods, and the labels, the researchers deduced that the campaign has been live since 2018, but only eight of them still remained on the Play Store until today. These are the following game and camera apps that are shown below, so if you have any of them installed on your device remove it immediately. In total, the 111 apps that were available on the Play Store counted more than 9.3 million downloads. That said, there are serious chances of old and removed apps from this campaign still operating on thousands of devices out there.
image source: blog.trendmicro.com
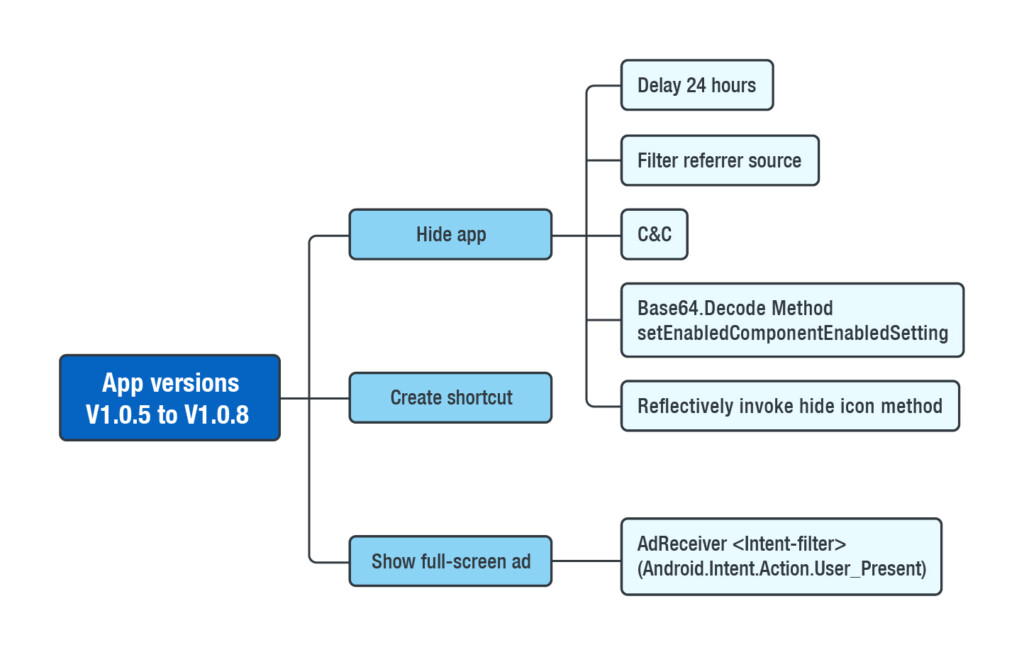
What all of these apps do is to pretend they're working normally for 30 minutes (or 24 hours in later versions), letting the user enjoy them as expected. When this period is over, the app hides its icon so that the user has difficulty in locating and uninstalling it, and pushes ads like crazy. The ads are full-screened and pop up continuously, even after unlocking the screen. It doesn't matter if the adware app is running or not, as the ads are pushed anyway. If the user tries to close the ad by clicking on the back button they are instead served with an “open with” prompt, and the close button only becomes available after a few seconds.
image source: blog.trendmicro.com
If you have one of these apps and want to remove it, you will still find it on the app drawer or the “apps” section in the settings menu. In the most recent versions of the adware, the crooks have added sandbox detection evasion techniques, smarter C&C server connection to hide from AV solutions, and base64 encrypted communication. If you want to stay protected from such dangers, only download high-quality apps that have high user scores on the Play Store and come from trustworthy developers who maintain a website as well. Finally, you should also use a mobile security and AV app from a reputable vendor.
Do you trust all apps on the Play Store? Have you ever had an adverse experience with adware? Let us know in the comments down below, or on our socials, on Facebook and Twitter.