The ‘TA800’ Group Is Using a New Initial Access Tool Called ‘NimzaLoader’
- The 'T800' hackers are using a new initial access tool written in Nim, called 'NimzaLoader.'
- This is an entirely different family of a payload fetcher than what was being used thus far.
- The most commonly fetched second-stage payload appears to be Cobalt Strike.
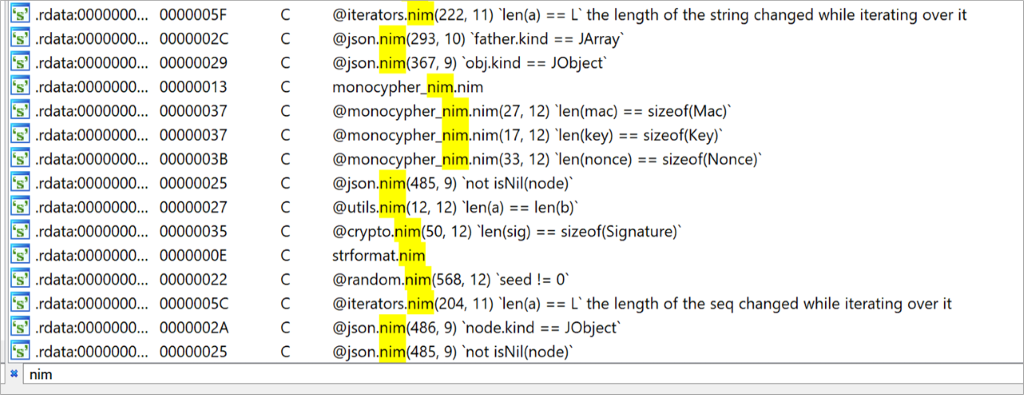
The threat group tracked as "TA800" has apparently shifted from using BazaLoader to a new malware called "NimzaLoader." The naming suggests that this initial access tool was written in Nim, a general-purpose programming language that is rarely used by malware authors.
According to the detailed report compiled by researchers at Proofpoint, who were the first to sample the new tool, the unusual choice of Nim could be an attempt to help TA800 fly under the radar and raise the effectiveness of its latest campaign.
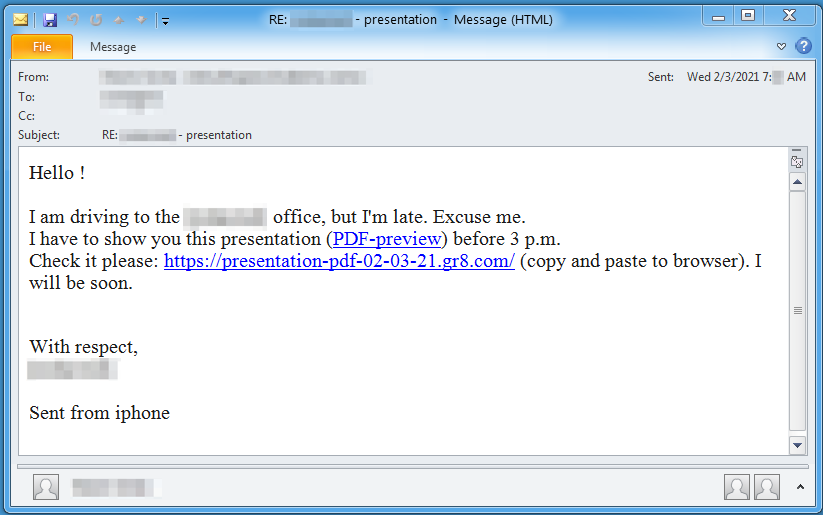
NimzaLoader has been used in a new campaign that appears to have started on February 3, 2021, and is ongoing. The actors are attempting to trick their victims by sending them emails containing personalized details like real employee and colleague names that one can easily find on LinkedIn.
These emails supposedly carry a PDF preview link - which, if clicked, takes the victim to a NimzaLoader download page. The actors are using an Adobe icon for the downloaded executable so as not to raise any suspicions.
Apart from the fact that NimzaLoader is written in Nim, the researchers have noticed the following differences compared to BazaLoader:
- Doesn’t use the same code flattening obfuscator
- Doesn’t use the same style of string decryption
- Doesn’t use the same XOR/rotate based Windows API hashing algorithm
- Doesn’t use the same RC4 using dates as the key command and control (C&C) response decryption
- Doesn’t use a domain generation algorithm (DGA)
- Makes use of JSON in C&C communications
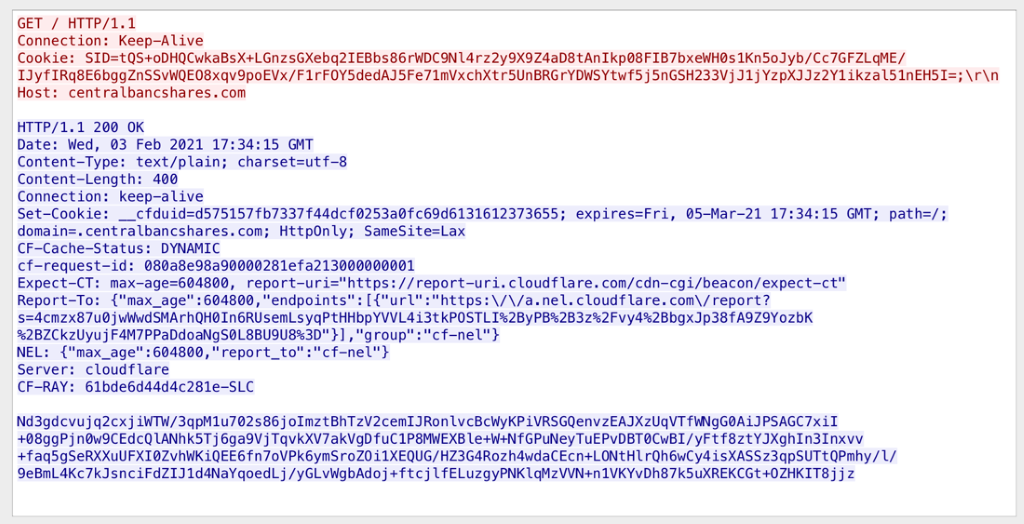
The researchers were able to analyze a sample through reverse-engineering, but by the time they got to that point, the C&C server was down, so not much about the infrastructure could be determined this time. They were still able to discern a handshake system based on the exchange of an X2551 key between the server and the malware, so all back and forth communications are encrypted.
As for the commands supported by NimzaLoader, these are the following:
- cmd – execute cmd.exe command
- powershell – execute powershell.exe command
- handshake – redo handshake
- shellcode – inject shellcode into a process as a thread
- command arguments are a JSON object containing:
- sc – hex-encoded and compressed shellcode
- prog – program to inject shellcode into
- heartbeat – used to update expiration date of the malware in memory
- command arguments are a JSON object containing:
- heartbeat – new expiration time
- sig – used in a signature check with an encrypted string
Finally, as for which tool is the secondary payload fetched by NimzaLoader, Cobalt Strike had the lion’s share in that regard. Still, Proofpoint doesn’t have an extensive dataset with which to determine the entire possible spectrum for the second stage just yet.