Fortnite Cheat Pack Contains the Syrk Ransomware Encryptor
- Fortnite cheat pack is basically Syrk ransomware which encrypts user media files and documents.
- Victims can find the decrypting key right on their system, so there’s no reason to pay the ransom.
- People are advised not to download and execute software from untrusted sources, and always back up their important files.
Fortnite is a hugely popular “battle royale” video game available for all OSes and console platforms. As discovered by Cyren researchers recently, cybercriminals are promoting a cheat pack that contains the Syrk ransomware, trying to infect targets from the game’s vast, 250-million player-base. The particular cheat pack contains an aimbot and a “wallhack”. The former aids the players to perform quick and precise targeting on the enemy’s head and thus getting an easy kill, while the latter helps them discover the locations of others no matter where they are hidden.
Unfortunately for those who are looking to cheat on Fortnite by using it, the package only contains the Syrk open-source ransomware, so merely executing it will create a series of problems on the host system. First, the Windows Defender is disabled, and so is the UAC (User Account Control). Moreover, applets that are able to monitor the running processes such as the Task Manager and Process Monitor are also locked down by Syrk. Next, the malware adds itself on the startup auto-loading list, so there’s some persistence over rebooting actions. The target files for Syrk include media files, text documents, presentations, spreadsheets, archived files, Visual Studio files, Photoshop files, etc.
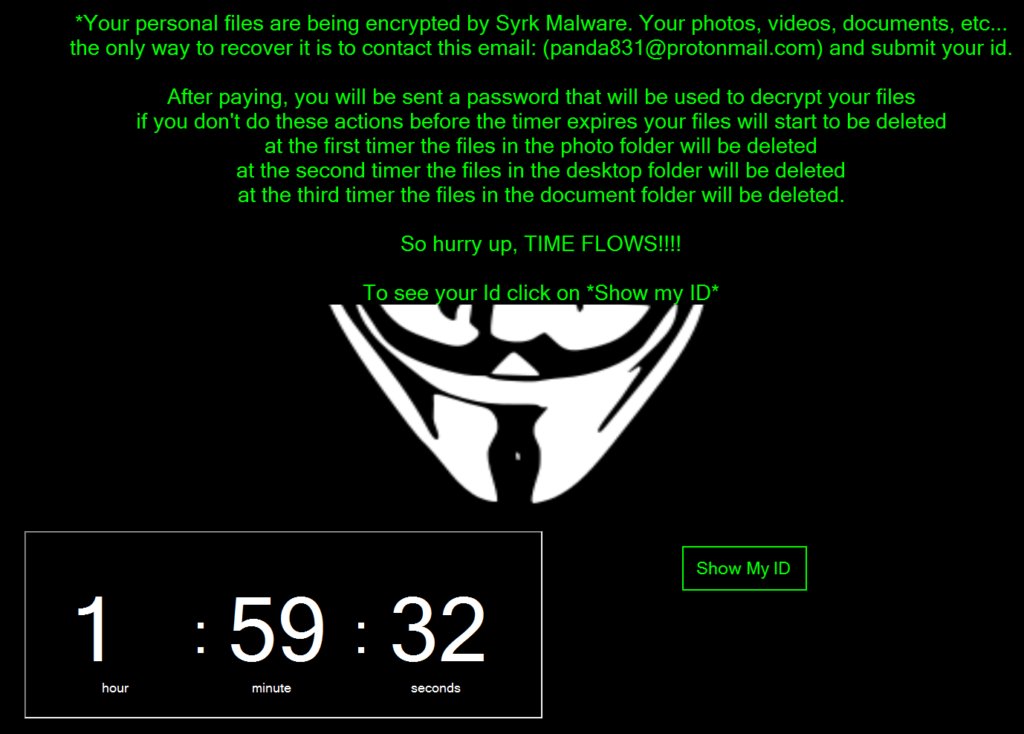
image source: https://www.cyren.com
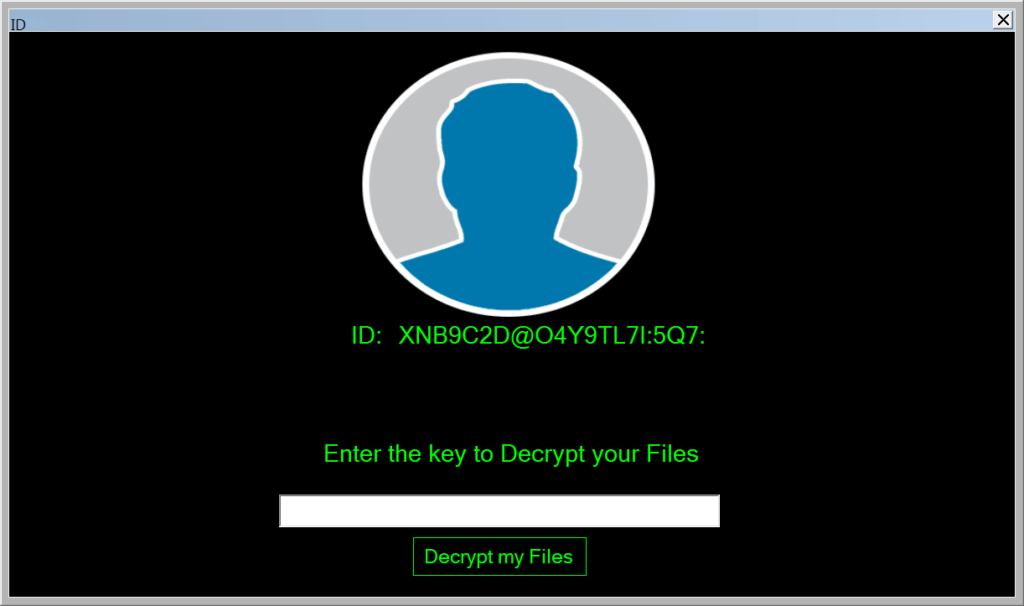
The message that the victim will get in this case urges them to contact a given ProtonMail address and submit their unique ID so as they are provided with the payment details. However, and as reported by the researchers, there are decrypters for Syrk, so you don’t have to pay anything to the ransomware actors. You can even use Syrk’s own decrypter by using the password that is stored locally on “C:\Users\Default\AppData\Local\Microsoft\-pw+.txt”. Why the software stores the key locally is inexplicable, but victims who aren’t facing the situation with composure would still pay the ransom.
image source: https://www.cyren.com
Syrk is making this case somewhat “light”, but there is nothing stopping malicious actors from using more powerful ransomware software on the next fake cheat pack. If you want to stay safe from such threats, you may refrain from downloading and executing cheats and just enjoy Fortnite as it is. Remember, none of these aimbots and wallhacks are released by Epic Games officially, none is endorsed, and none is reliable. Even if your computer isn’t infected by malware at this point, you are very likely to get banned from the game for cheating.
Are you using a cheat for Fortnite, or do you find that they destroy the joy of winning fairly? Let us know in the comments down below, or on our socials, on Facebook and Twitter.