REvil Ransomware Hits Spain’s State-Owned Railway Management Body
- ADIF in Spain has been hit by the REvil ransomware actors, apparently twice already.
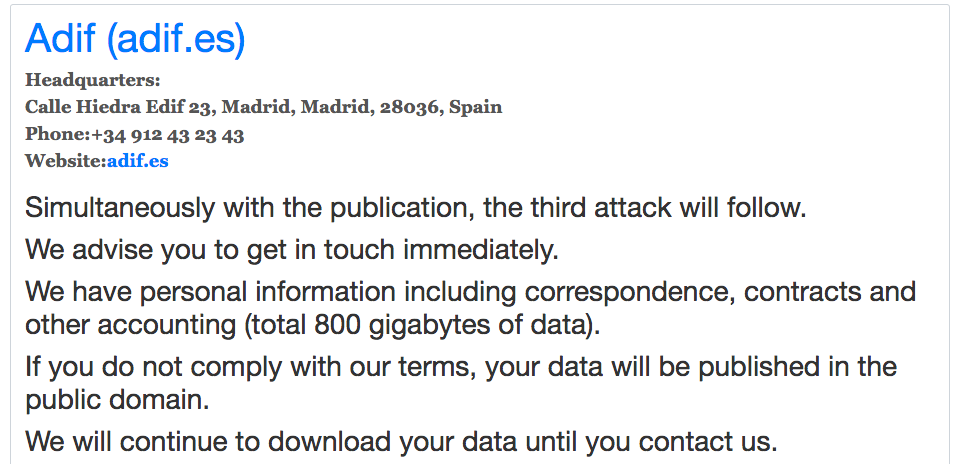
- The actors have published a final warning for the company to reach out, threatening to launch a new attack otherwise.
- The published data includes contracts, communications, documents, property records, and more.
The REvil ransomware gang has returned with yet another prestigious victimization, hitting Administrador de Infraestructuras Ferroviarias (ADIF). ADIF is Spain’s state-owned railway infrastructure management body, employing about 13,800 people and having yearly revenues of eight billion EUR.
They manage a large number of tracks, stations, freight terminals - and, most crucially, the rail traffic. They distribute capacity, collect fees for the use of the country’s railway infrastructure, and in general, play a pivotal role in the operation of the national transportation network, its development, and by extension, the socio-economical flourishing of entire areas. For REvil? They’re just the new cow to milk.
According to a Cyble report, the REvil group has stolen sensitive data from ADIF, and they have already published the first sample. This is part of the typical extortion process - the ransomware actors are gradually publishing more revealing data, forcing the victims to an increasingly worsening position until they accept to pay the ransom. In this case, the ransom amount hasn’t been disclosed, but we reckon it’s a dizzying figure.
REvil states this leak is also a warning, as they plan to launch a third attack to ADIF if the railway management firm fails to contact them immediately.
Source: Cyble blog
So, first of all, this means ADIF has already been breached twice. Secondly, the 800 GB of data that have already been exfiltrated should be enough for extortion purposes, so the third attack could have a higher-level goal, such as crippling ADIF’s operations. We sure wish this won’t affect the safety of train passengers in Spain, as ransomware actors have generally failed to show signs of having any ethical barriers whatsoever.
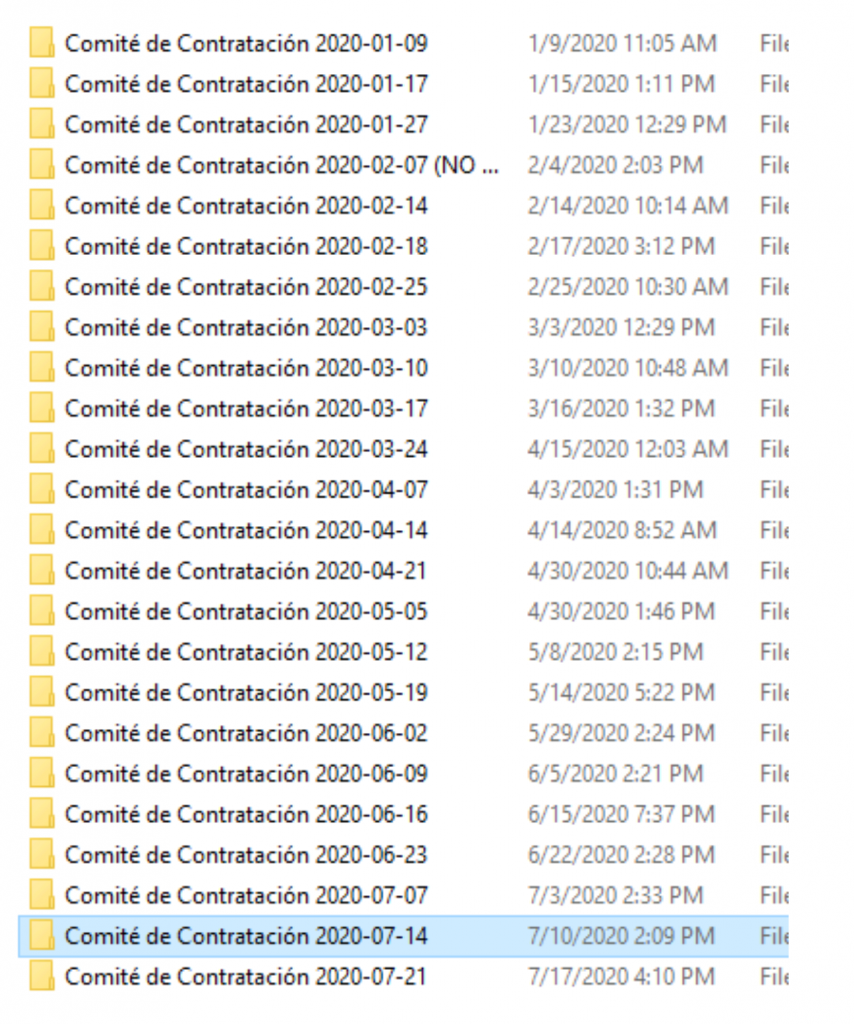
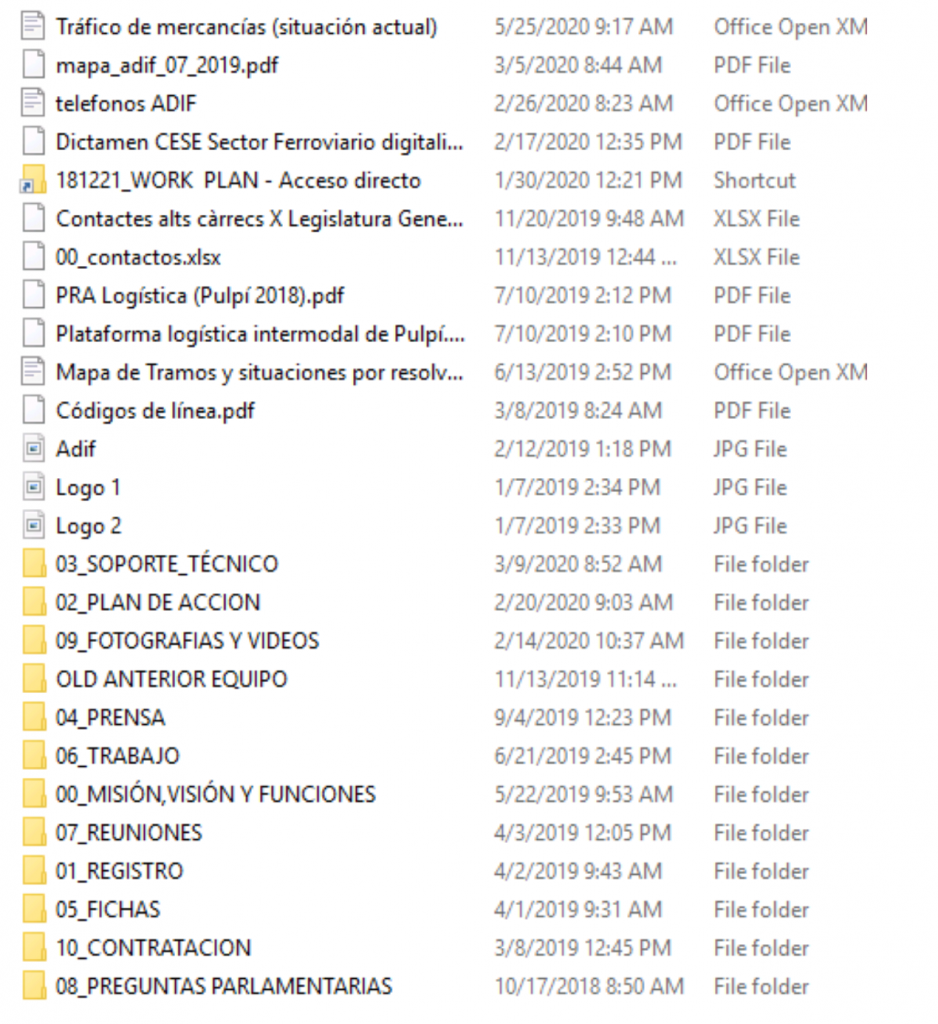
As for the already-stolen data, this includes high-speed hiring committee contracts, property records, field work reports, project action plans, documents about customers, contact information, correspondence records, and more.
Source: Cyble blog
Source: Cyble blog
Since the start of the year, REvil has compromised a Brazilian electric power company, the ‘Lion’ beer brewer in Australia, the ‘GSMLaw’ firm in New York, the ‘Travelex’ currency exchange platform, and almost certainly many more.
If you work for a large business, do not click on links that randomly arrive on your inbox, don’t open attachments, don’t use unfamiliar USBs, take regular data backups, and keep your security software up to date. If things go wrong, paying the ransom won’t change anything, as there are no guarantees that the extortion will stop there.
Read More:
- Brazilian Electric Power Company Extorted by REvil Ransomware Actors
- “Lion” Compromised by REvil Ransomware Actors Who Are Leaking Data
- REvil Ransomware Actors Threatening to Leak “GSMLaw” Documents
- Travelex Still Offline After a Sodinokibi Ransomware Attack