Phishing Actors Try to Lure Steam Users With a Free Game
- Phishing actors use Steam to steal accounts of credulous users, baiting them via private messages.
- The redirecting URL takes them to Twitter, and from there to the main phishing website.
- The phishing domains are appropriately crafted and look legit, with the signs of trickery being minimal.
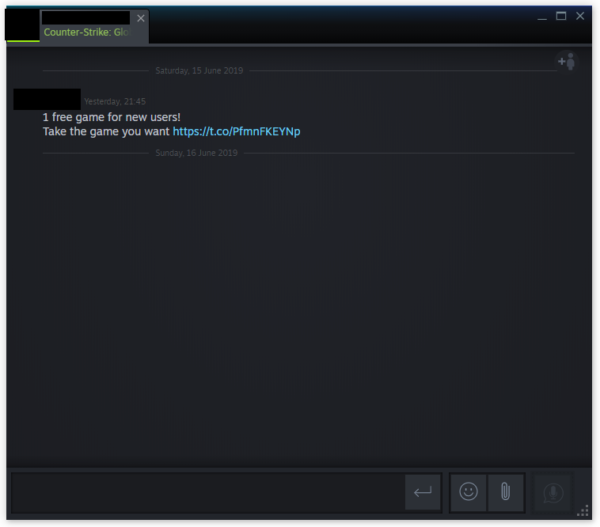
According to a report by Malwarebytes, there has been a phishing campaign that is taking place on Steam since March, but not a lot was known about it because it is staying somewhat underground. The phishing links that urge users to follow them are not published on forums and public discussions but sent to the players via private messages instead. These messages are disseminated by hacked accounts and reach those who are in the network of these accounts. That said if you get a message from one of your Steam friends claiming that you can get a free game, think twice before clicking on it.
image source: blog.malwarebytes.com
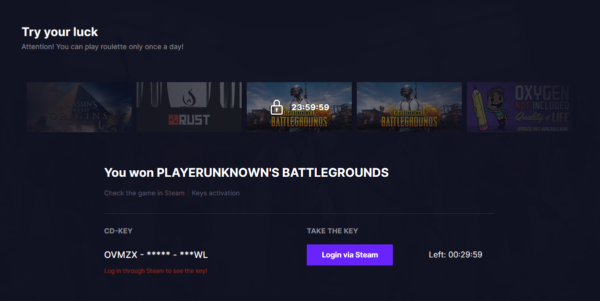
The URL redirects to a Twitter page, which then redirects through the chat to the real phishing page that pretends to be a “free game keys” platform. The exposed URLs are down now, but there are many more out there playing the same role for these actors. The Gift4Keys website, for example, is a properly made website that looks legit and urges visitors to “try their luck” on the game roulette. The victim is pressing on the “Play” button and the roulette starts spinning. Finally, the roulette stops on a game that the user supposedly just won.
image source: blog.malwarebytes.com
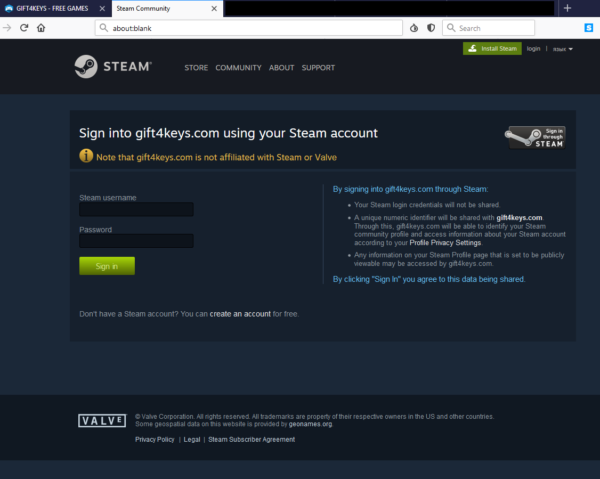
To claim the won game, the visitor has to login to their Steam account right from the website and is given 30 minutes to do so. The roulette is then locked for 24 hours, so the visitor will have to wait for another day before he wins another game (supposedly). Clicking on the “Login via Steam” button takes the victim to another phishing webpage which was made to look like the Steam login page. Malwarebytes testing revealed that this webpage could either come as a pop-up or a new tab, so this is a bit random at this point.
image source: blog.malwarebytes.com
Obviously, crooks are using the collected credentials to spread more of their phishing links to a wider Steam audience, getting even more credentials and so on. What these people do with the stolen accounts is to sell them on darknet marketplaces. The domains that have been confirmed by Malwarebytes to be phishing URLs are the following:
- easyk3y[dot]com
- ezzkeys[dot]com
- g4meroll[dot]com
- g4me5[dot]com
- gift4keys[dot]com
- gifts-key[dot]com
- ong4me[dot]com
- tf2details[dot]com
- yes-key[dot]com
As mentioned above, this doesn’t mean that the above are the only ones. Crooks are continually refreshing the domains they are using to trick Steam users into giving away their credentials, so beware.
Have you ever received a message from one of your Steam friends claiming that you’ve won a free game? Share the details with us in the comments down below, or on our socials, on Facebook and Twitter.