BeiTaAd Adware Found in 238 Google Play Apps with 440 Million Installations
- CooTek’s BeiTaAd adware plugin has found its way into the Play Store through 238 apps.
- Cumulatively, the apps have been downloaded by more than 440 million users.
- The adware pushes out-of-app ads, interrupts even phone calls, and auto-plays video and audio ads.
Lookout researchers have discovered a large-scale infection of a large number of apps that are available on the Google Play store, that contains the BeiTaAd adware plugin. This is an especially nasty piece of software that pushes ads on the device even when the user is on the lock screen, downloads and plays video and audio ads even when the phone is locked, and displays all kinds of pop-ups and out-of-app ads that make using the phone unbearable. Following Lookout’s report to Google, the latter removed the apps from its official store, but since there have been 440 million installations, many people out there are bound to still running one of them on their phone.
image source: blog.lookout.com
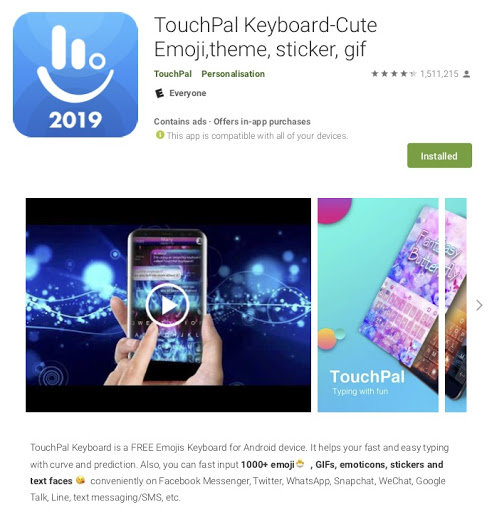
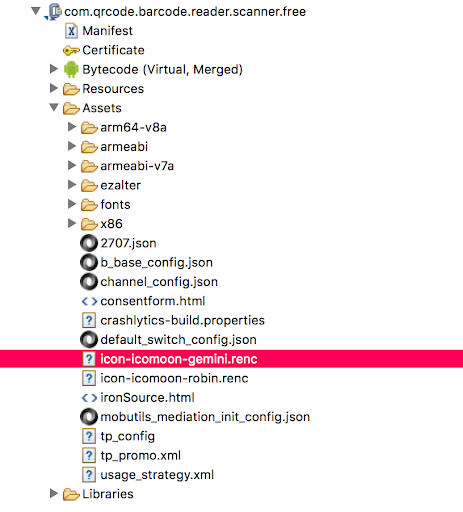
The particular plugin was developed by CooTek, a Chinese developer who is known for their popular keyboard app, TouchPal. TouchPal alone counts over 100 million installations, and in its review section, many users are reporting excessive and obtrusive ads even after paying for the premium upgrade. The BeiTaAd has been under continuous development and improvement since its initial release back in early 2018, adding AES encryption and renaming its components (to “icomoon gemini”) to discard any resemblance and create confusion to the users who are trying to find the root of the ad-serving nightmare on their phones.
image source: blog.lookout.com
The loaded plugin is not planted into the device through the usual installation method, so you won’t find it by browsing the list of your installed apps. Instead, head on to “/data/user/0/<package_name>/app_p_od” and locate the malicious JAR file. Where “package_name”, is the app that came with the adware bundled. As we have seen before, the problem with these plugins is not that the developers of hundreds of different apps are conspiring to push adware around, but rather get tricked into using infected SDKs in their apps. That is why many of the compromised apps have been already re-uploaded to the Google Play store and are clean of adware this time. For a full list of the BeiTaAd apps, check Lookout’s full list.
Care to share your thoughts on the above? Feel free to do so in the comments down below, or on our socials, on Facebook and Twitter.