Mongol DDoS Attacks Still on the Rise and Getting Even Harder to Detect
- Mongol DDoS attacks are not likely to stop any time soon, as there’s still little we can do against them.
- This type of attacks have gotten more persistent, last longer, and have also grown in number.
- Researchers are still trying to develop smarter detection tools, as CSPs are increasingly falling victims of perpetrators.
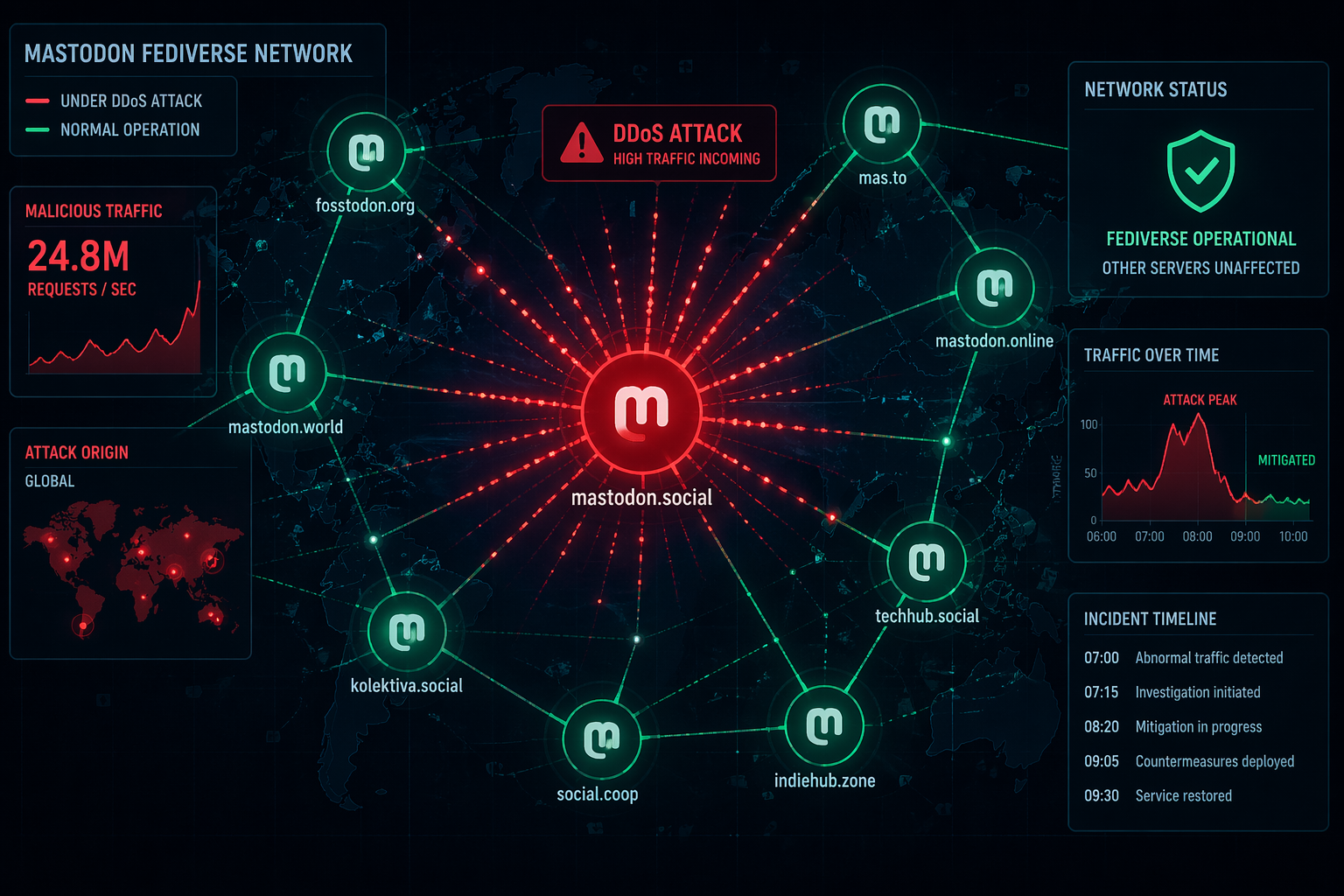
A recent research report by NexusGuard has confirmed something that multiple researchers are urgently warning about, and that is the alarming rise of “Mongol DDoS" attacks against CSP networks. In January, we tapped into the previous report from the same security research company, which indicated a worrying development in the world of DDoS attacks, involving sneaky small-sized swarm-like overloading action that ISPs find especially hard to deal with. The attackers are utilizing hundreds of individual IPs to inject junk data into the regular traffic, and then converge this junk at the destination, wreaking absolute havoc at the last minute.
Back in January, we saw that this trend was just starting to gain traction, but the latest evidence shows that it has been established for DDoS attackers, and it’s definitely here to stay. Compared to the previous three-month period, Mongol DDoS attacks show a rapid rise of 49.15% in the maximum attack size, 3.75% in the average attack size, and 36.08% in the total number of attacks. The amazing rise in the maximum attack size indicates that attackers are employing an unprecedentedly large-scale arsenal to bring down targets that were previously thought to be invulnerable.
The types of DDoS attacks that show the biggest rise compared to the previous quarter are the HTTPS Flooding (+194.17%), SSDP (+91.21%), and Amplification attacks (+78.80%). The researchers have concluded that the attacks became more persistent and more prolonged as well, going on for a minimum of half an hour and up to a full day. The average duration of the attacks is now at 450 minutes, 175% up compared to last year. Although some targets experienced even 13 attacks within a day, most of them were targeted during peak service hours to cause the greatest disruption.
As for the source of the Mongol DDoS attacks, China led the malicious efforts with 23%, while the United States came second, accounting for about 18% of the total number of attacks. Now, besides the efforts of agencies like the FBI and the Europol to seize the operation of the largest DDoS-for-hire service providers out there, there’s not much that ISPs can do. The network infrastructure remains somewhat naked against these sneaky Mongol DDoS attacks, with the only method of prevention is the clever attack pattern identification and an increase in the versatility of whatever anti-DDoS systems are in place.
Care to share your opinion on the above? Feel free to do so in the comments section below, or join the discussions on our socials, on Facebook and Twitter.