Japanese Power Tool Maker ‘Yamabiko’ Claimed as Victim by Babuk
- The Babuk ransomware gang has returned to ‘normal operations,’ claiming another victim.
- The compromised company is ‘Yamabiko,’ a Japanese toolmaker with a worldwide reach.
- The actors claim to have stolen 0.5 TB of sensitive data and are already leaking out some documents.
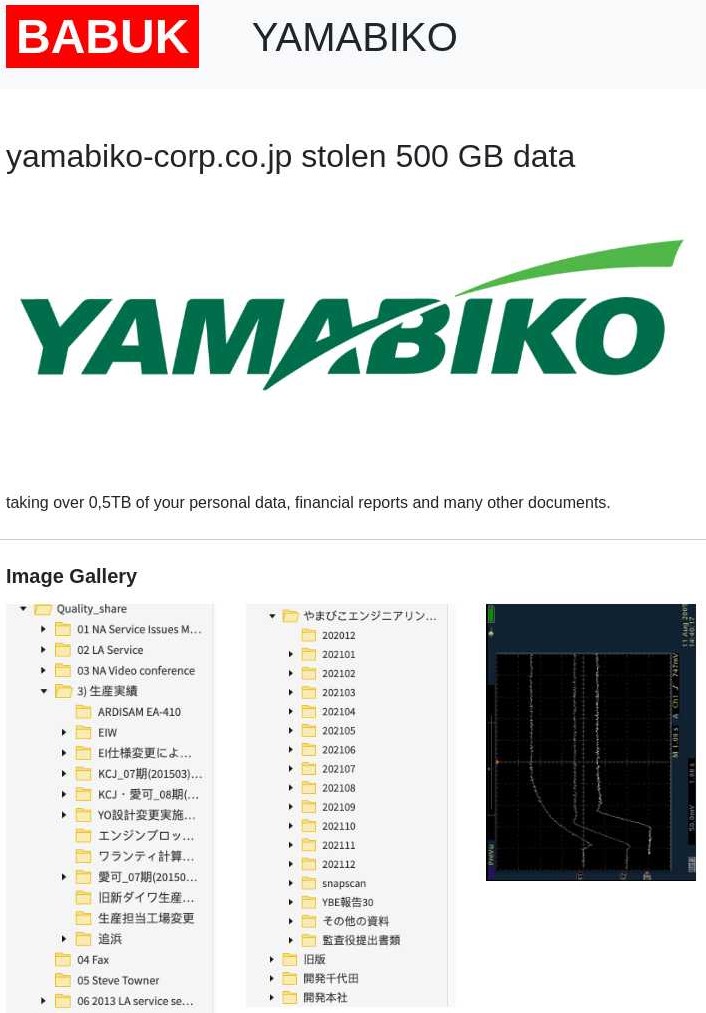
The Babuk ransomware gang has added ‘Yamabiko Corporation’ in its data leak portal, claiming to have stolen 0.5 TB of sensitive data from the Japanese power tool maker. The hackers are presenting screenshots of accessed filesystems, Solidworks files, personal employee data, financial reports, testing diagrams, circuit schematics, etc. The leaked files appear to be valid, and some of them feature the letterhead of Yamabiko or its brands, but so far, there has been no official admission of an incident.
Yamabiko is the result of a 2008 merger between Kioritz and Shindaiwa, with the two companies retaining their brands while also launching a fourth one, the Echo. It is headquartered in Tokyo and is selling power tools, agricultural machinery, and outdoor power equipment worldwide, using the aforementioned brands. The company has over three thousand employees, and its yearly revenue surpasses that of a billion USD. As such, if they have been hit by Babuk, the ransom could be a notable figure.
The website of Yamabiko remains up albeit characteristically slow, but this could be its standard performance anyway. After all, Babuk has previously stated that they will no longer focus on encrypting any files on the victimized networks. As such, Yamabiko shouldn’t have any front-facing trouble due to a ransomware attack by that group.
The problem remains solely the stolen data and the possibility to leak it publicly. We have contacted the company asking for a comment, and we will update this post once we hear back from them.
This is also the first time that the Babuk group moved against a company after their confusing and contradicting messages about ending its operation, and we see this as a confirmation that they’re not going anywhere for now. Also, in terms of their way into Yamabiko’s systems, if that has really happened, Babuk has stated in a recent interview that they are using a VPN zero-day. A recent report on a Japanese news site mentioned that VPN products are the most abused entrance points for ransomware actors against companies in the country.
And as for Babuk’s chances of getting any money from Yamabiko, we would say that Japanese companies are among the most difficult to negotiate this kind of stuff with. We saw this recently with Capcom, not accepting to discuss with the hackers of the “Ragnar Locker” group who demanded a payment of $11 million in Bitcoin.