The Babuk Ransomware Gang Isn’t Quitting, They’re Just Changing Focus
- Babuk isn’t going to quit the ransomware space; they’re just stopping the encryption games.
- The actors will focus on stealthy network infiltration and data-stealing extortion from now on.
- This is probably the next step in the ransomware space in general, as it comes with a set of key benefits.
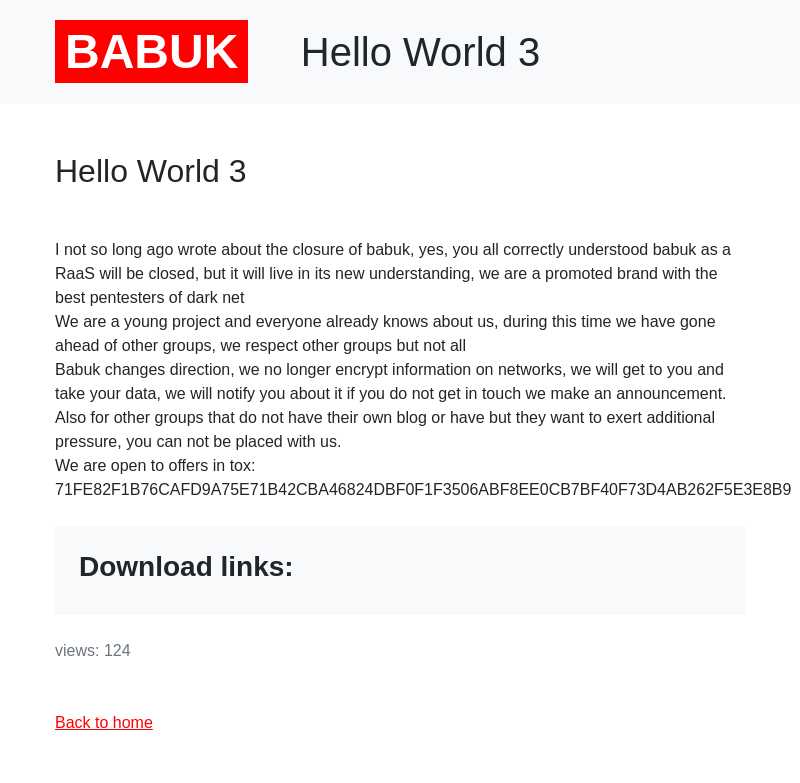
The Babuk ransomware gang has made some back-to-back announcements on its dark web portal following the attack on Washington D.C. Police network, and naturally, the media got confused. First, they declared that this was their last ransomware attack during an interview and informed that they're planning to share the source of their buggy strain openly.
Then they decided to launch something like an open-source RaaS (ransomware as a service), remaining in control of the project. And most recently, they posted a third announcement saying that they will just close the RaaS program, stop encryption operations and focus on data-stealing extortion.
While Babuk’s claims and announcements come and go, and they frankly don’t have much value, it is important to understand that what these crooks are saying is symbolic of a new age in ransomware operations. We are seeing an increasing rate of ransomware incidents not affecting operations or taking down websites, as the actors are focusing solely on stealing sensitive data.
The encryption aspect of ransomware attacks has gradually taken the back seat, playing a secondary, less important role, and has now reached a point that it’s totally optional, if not entirely obsolete already.
After all, companies that have proper backup programs in place can recover from encryption incidents, even if it isn’t always simple or free of time-consuming complications. The encryption of files is simply not damaging enough anymore, so Babuk figured they might as well skip it entirely and focus on what really matters, the data exfiltration.
The advantage of this is that the attackers will have fewer chances to raise alarms on the victim side, so they will have higher success rates. Also, they won’t have to waste time fixing and/or strengthening their encryption schemes, so they’ll instead focus on honing their network infiltration skills.
So, shall we expect more ransomware gangs to follow suit? That’s very likely, if not certain, but we’ll have to wait and see what direction other big groups will choose to take in the following months. In many cases, we see ransomware groups having ethical boundaries, not attacking certain categories of organizations or companies that offer crucial services, like healthcare centers and hospitals, for example. This is to avoid causing a disruption in their operations, which would essentially risk human lives. If the encryption aspect is taken away, these entities could become eligible for targeting and extortion again.