Hamas Actors Hooked Israeli Soldiers on Dating Apps
- Hamas hackers lured hundreds of Israeli soldiers into downloading malware on their phones.
- The hackers used stolen images of attractive women and sent messages on Facebook and Instagram.
- The apps collected information by running secretly in the background and were able to download additional “.dex” files.
Hamas hackers have reportedly tricked several Israeli soldiers into installing malware on their devices by using fake dating app profiles - the Israel Defense Forces (IDF) tweeted about the danger to warn everyone else of the risk. At the same time, Israel Defense Forces are also boasting that they took down the enemy’s hacking system as soon as they discovered the problem. According to the latest reports, Hamas actors have created fake dating app profiles using stolen images of good-looking girls. They managed to lure in hundreds of Israeli soldiers and convince them to download the app executables.
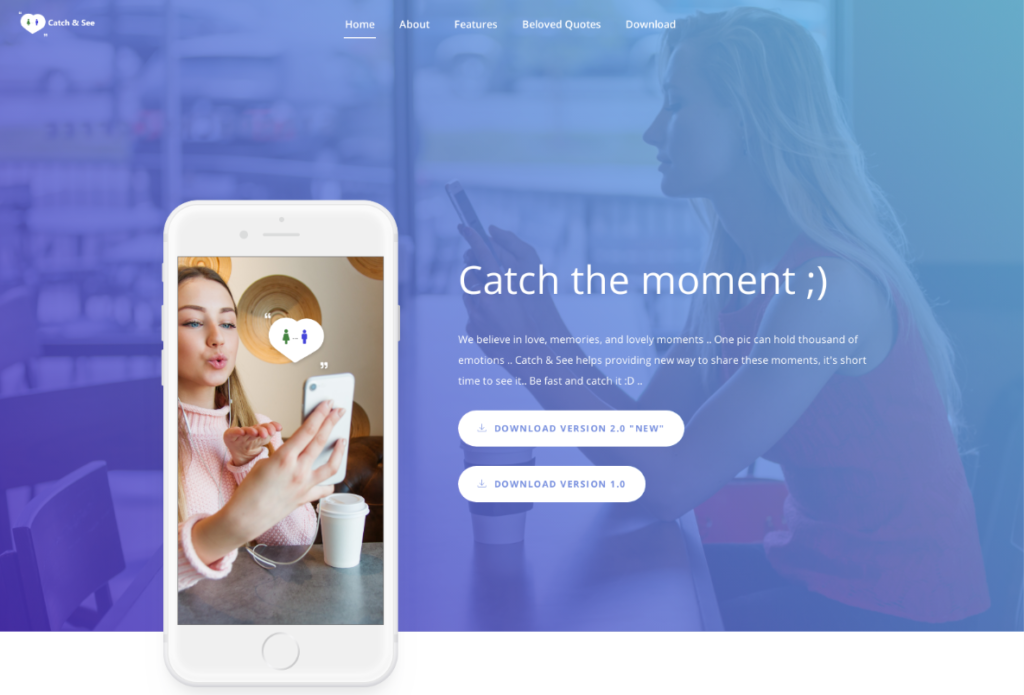
Hamas created fake social media profiles, using photos including this one, in an attempt to hack the phones of IDF soldiers.
What Hamas didn’t know was that Israeli intelligence caught onto their plot, tracked the malware & downed Hamas’ hacking system.#CatfishCaught
— Israel Defense Forces (@IDF) February 16, 2020
Hamas is a Palestinian Sunni-Islamic militant organization that is fighting against the Israeli occupation in the Gaza Strip. They have been engaging in military operations as well as cyber warfare against Israel, so this is just another page in the book of the ongoing conflict between the two. Back in May 2019, a Hamas hacking group tried to compromise Israeli targets, with the IDF responding by air-striking the building where the hackers resided. This disproportional response was an example of how serious these hacking attempts are for the Israeli forces, as Hamas has successfully hijacked military drones many times in the recent past.
This time, Israeli soldiers received messages on their personal Facebook, WhatsApp, Instagram, and even Telegram accounts, trying to lure them into downloading three dating apps where they would supposedly continue their communication with the girls that approached them. These chat apps, however, were nothing other than malware disguised as legitimate online dating platforms.
The actors have even set up websites to help convince the victims that these apps were real and trustworthy. The apps work in the background while collecting device information and sending it back to their makers. In some cases, the app icon is hidden right after the installation to trick the victim into thinking that nothing has happened.
Source: CheckPoint Research
Some of the app names that were used in this campaign are "GrixyApp," "ZatuApp," and "Catch&See". While the collected information wasn’t too sensitive, these apps had the ability to download additional files and to access the camera, GPS, SMS data, browser history, and calendar entries. By downloading additional ".dex" files, these apps could wreak havoc on the infected devices. But, according to the IDF, the actors didn’t get the chance to move to the next phase of the campaign as they were detected and stopped.