Hacker Breaches Data Leak Monitoring Service “DataViper”
- Someone has breached Vinny Troia’s “DataViper” data leak monitoring platform.
- The hacker has uploaded database indexes and is offering 50 of them for sale on the dark web.
- The researcher believes that it was an act of revenge and that the databases that are for sale are unrelated to the incident.
A peculiar case of a hacker attacking a data breach monitoring service has surfaced, and it looks like revenge was the motive of the attacker. The victim is the “DataViper” platform, which is the creation of Vinny Troia, a security researcher working for “Night Lion Security”. The alleged date of the breach is July 9, 2020. It is possible that the firm exposed the work of the hacker, so the person had a reason to fight them back. As per the claims made by the hacker, over 8,225 databases containing the information of billions of internet users are now in his/her hands.
These databases were collected by DataViper as part of the platform’s operation, which is to monitor and index what is leaked in the dark web. If the data has indeed fallen into the wrong hands, the hacker could make it look like the security firm is directly responsible for the people’s PII exposure. Normally, DataViper only allows the owners of this data to access it, in order to evaluate the damage they suffered. From a business perspective, there’s the obvious irony of having your security company breached by hackers which is another negative aspect of this attack.
Source: ZDNet
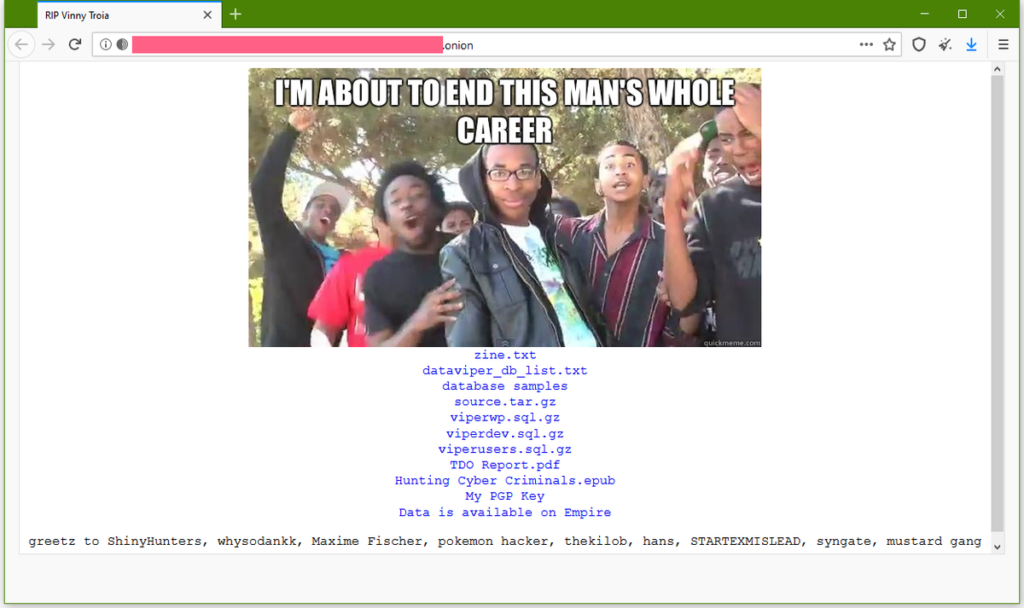
The hacker has used the name “NightLion”, to mock the security company, and then dissipated a link to an onion domain where he/she uploaded samples of the stolen data as well as information on how the hack was conducted. There, the attacker gives details on how the intrusion in DataViper’s backend infrastructure happened, a full index of the exfiltrated databases, 482 JSON files, and various other details. For starters, the hacker has put up 50 of the stolen databases for sale on a popular dark web marketplace, so the actor is already monetizing the data.
From his side, Vinny Troia confirmed the hack and stated that the hacker gained access to one of their testing instances. That said, the security researcher believes that what was put up for sale is the product of a different breach, potentially the work of groups like TheDarkOverlord, ShinyHunters, and GnosticPlayers, who are connected with the “NightLion” hacker. After all, all these groups have common reasons to target Troia and his company, since he is actively trying to reveal their real identities, and he is actually planning to publish some juicy details regarding that very matter this Wednesday.
Read More:
- A British Security Company Leaks Five Billion Records Online (Update)
- ‘Freddie Mac’ Mortgage Loan Company Announces Data Breach
- The Details of 384,319 BMW Owners Are for Sale on the Dark Web