A Crash Course in Encryption History
If you care about computer security at all then you’re at least aware of digital encryption’s importance. It’s the cornerstone of the internet and everything you use it for today. Without encryption, the only thing the web would be good for is cat video sites. Shopping, banking and gig economy apps like Uber need it. They are simply not possible without secure encryption.
The same goes for our personal electronics. Thanks to device encryption, you can now store your personal information on something like a thumb drive or smartphone. Without any reasonable prospect that anyone can get to it without your permission.
Encryption is integral to modern digital life. So much, that you’d be excused for thinking it was invented as part of the computer age. It turns out however that cryptography is far older than you may think.
The Need for Secrecy
We, humans, are pretty special in the animal kingdom. All animals communicate in one way or another. We are however the only animals to develop language. We can accurately convey our thoughts to someone else. Just by using a system of verbal symbols. As well as the rules that govern them.
When we invented writing, we amplified the power of language. Now it could exist over time and travel over massive distances. You could send someone a message on the other side of the world. Alternatively, someone could read it 100 years from now from you writing it down. Then we figured out how to mass produce copies of these messages. Then the whole world changed again. The printing press, radio, and TV were earth-shaking technologies.
The problem is that, as soon as your communication moves beyond face-to-face communication, there’s a real danger that someone will intercept it you don’t want to.
A general sends his troops an order via carrier pigeon. You don’t want someone shooting it down and figuring out his plan. That’s why encryption has been around since ancient times. Starting with the Old Kingdom of Egypt.
From the Age of Pyramids
Nearly four thousand years ago, someone carved a very important set of hieroglyphs into the wall of a tomb. A person fluent in reading standard hieroglyphs at the time would have been a little confused by these cryptic messages. Apparently, no experts think that this writing was meant to keep a secret. Instead, it was just meant to be arcane and indecipherable. It still counts as cryptography though. Since it was writing specifically designed not to be read by just anyone. This discovery lets us put a solid earliest date on the idea of cryptography. Of course, there are likely earlier examples. Ones lost to the ravages of time. Unfortunately, we’ll never know.
As records and civilizations progressed, the idea of keeping information secret in plain sight also becomes far more common. Around 700 BC, Spartan soldiers used a device known as the Scytale.
It’s actually pretty ingenious. First off, you create two wooden rods that are identical in size and shape. This has to be done very precisely. Otherwise, the system won’t work. One rod is then taken by each person who needs to communicate in secret.
A leather strip is wound tightly around the rod. Then the message is etched onto it. When you unwind the strip, the letters make no sense at all. However, when the other person wraps it around their rod, the message becomes clear. Obviously, this can be defeated. But one would have to experiment with rod dimensions. Hopefully, this would take long enough that Spartans could do something else instead.
The Middle Ages
Like Algebra and other branches of modern mathematics, one of the clearest lines between modern cryptography and the past can be drawn to the Arab nations. They carefully documented cryptographic methods. In addition, they documented code-breaking algorithms. The work that Arab scholars did around the year 800 AD laid the foundation for fundamental cryptography. Information still used to this day. It would only be in the early 20th century that such large steps would be taken again. It was a book published by one Al-Kindi that would prove fundamental. Pioneering the mathematical ways of breaking ciphers and also how to strengthen them against code-breaking attempts.
In the 1300s more Arabic cryptography work was published. This included various ciphers more advanced than simple substitution ciphers.
Meanwhile, in England, there was some use of substitution ciphers in use by priests. That makes sense. Given that very few people were literate and the clergy often acted as scribes. It doesn’t seem as if these ciphers were applied to any serious use. They were more for amusement and the creation of puzzles.
By the 1400s however, things had become more serious. The Duke of Mantua is known to have used quite a sophisticated cipher. One that has multiple substitutions and other safeguards against frequency analysis. The method most commonly used to break substitution ciphers.
Leon Battista Alberti is widely thought of as the patriarch of Western cryptography. It was in the latter half of the 1400s that he presented a sophisticated poly-alphabetic substitution cipher. It used two metal discs with letters. You could rotate the two discs to instantly create different ciphers.
Renaissance Cryptography
The period following the Middle Ages is known as the Renaissance. This is where significant cultural gains happened in the West. Kick-starting the process that would deliver modern Western values.
These relatively rapid and radical socio-political changes made cryptography important. Various states, provinces, and cities were clandestine conflicts. Working against each other in secret. Hiding the meaning of messages passed to spies and diplomats alike. There was some increase in cipher sophistication during this time. But they still sucked and were broken often. However, without cryptography, plenty of plots would probably have failed back then.
Industrial Age Secrets and WWI
When humanity started to master and embrace machines, things began to change quickly. Steam power was changing the way we did work. Advances in clockwork and other sophisticated mechanical devices were laying the groundwork for the computers of today.
At the same time, thinking about cryptography and the mathematical approaches to both making and breaking codes were getting a lot better. The Jefferson wheel, named for Thomas Jefferson who invented it, used 24 rotating cylinders with randomized letters. You could create messages. Then note a landmark string in that configuration. Using the wheel, you get the message back later by reproducing it. These wheels were used by the US army for quite a while in the early 20th Century.
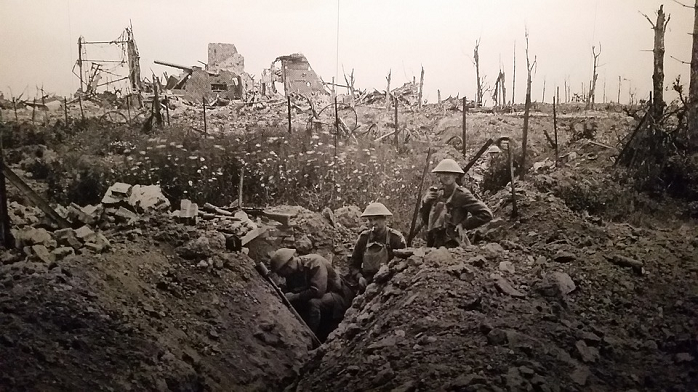
By the time the first World War rolled in, cryptography was pretty mature. This would prove pivotal to the war. Both the Germans and their adversaries used ciphers to prevent intelligence from getting into the wrong hands.
Radio changed the way that wars were thought. Many new ciphers and cryptography devices were invented during this time. However, one of the most interesting footnotes is the use of Native American code talkers. This is where Native American troops were included in military units. They would talk to each other over the radio in a language that the Germans almost certainly had no way of understanding. It’s not strictly cryptography, but a very cool fact!
World War II
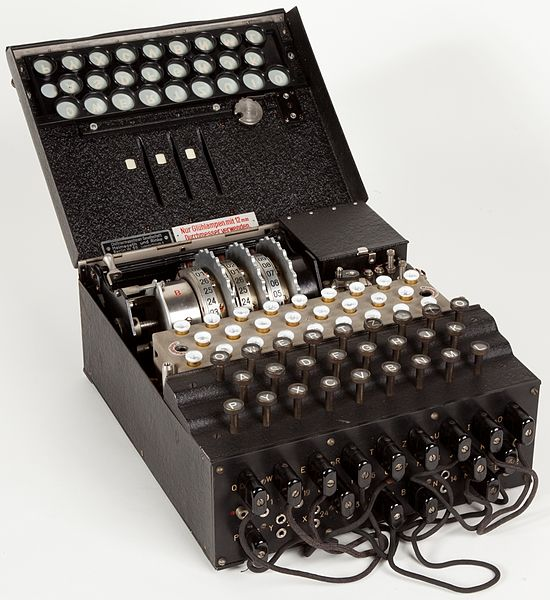
Enigma Machine Image By Alessandro Nassiri [CC BY-SA 4.0 (http://creativecommons.org/licenses/by-sa/4.0)], via Wikimedia Commons
The Germans elevated the art of using encryption in war higher than anyone thought possible. They had invented the machine called the Enigma. This device constantly changed ciphers on a daily basis. It seemed like an impossible problem at first. Thankfully, geniuses like Alan Turing created machines that could crack the Enigma codes. Quickly enough to catch the Germans off guard. In a very real sense, the cracking of Enigma helped win the war for the Allied forces.
Cryptography Today
From the end of the Second World War onwards, digital computers began coming into their own. At first, developed to combat enemy encryption. To perform other war-related calculations. These computers quickly started finding a home in almost every sort of business. Eventually, we started networking computer systems together. Which is what lead to the internet itself.
The internet as we know it today started out as a military project in the form of ARPANET. Despite this, it doesn’t seem like that much attention was given to securing the information that would pass through it. The early internet only connected trusted actors like universities and government installations.
The Second World War had driven the development of computers. Which started out as a way to break the ultra-tough (for the time) German code machines. So it’s sort of ironic that cryptography played a major role for the initial investment in digital computing. Which in turn drove the greatest enhancements in cryptography.
When the internet and the Web became something that normal, everyday people would use, things had to change. The Web offered an incredible opportunity to provide new services and business models. None of which would work if anyone could just intercept the information. The invention of DES digital encryption standard probably kicked off the overall race. Heading towards effective digital cryptography. By 1997 AES was developed to replace DES and we still use it to this day!
A Radical, Encrypted Future
While the development of cryptography over history has been relatively slow, the last century or so has seen an explosion in the technology. Most of this is thanks to the development of computers. Especially following the Second World War.
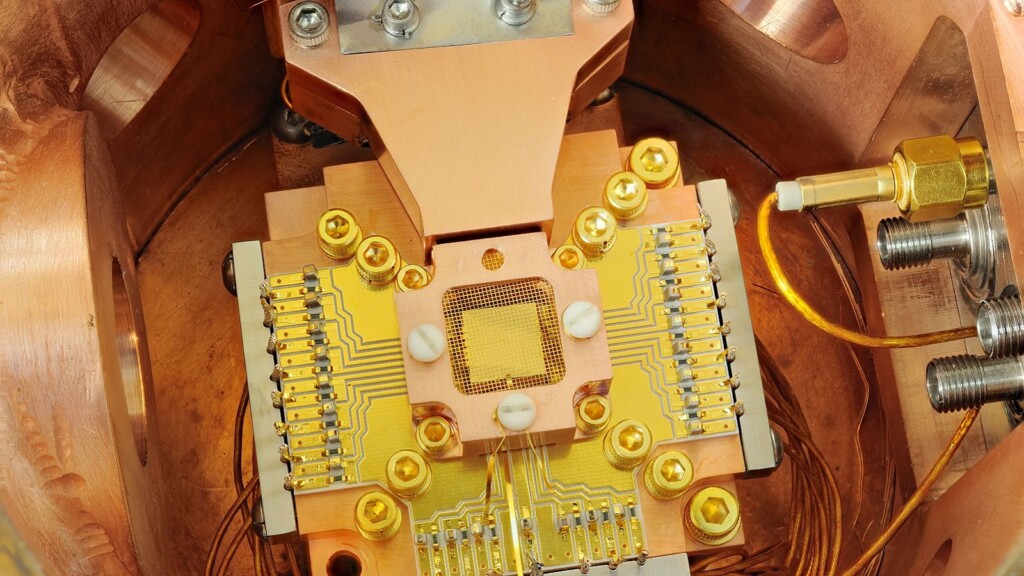
Since then things have not only been progressing more quickly but it seems the speed of development is picking up. Several radical new computing technologies promise to push cryptography into a new realm.
The most promising branch of technology is quantum computing and the related field of quantum cryptography. A quantum computer uses the spooky nature of the universe at the very smallest scale to perform a computation. Unlike digital computers, which have bits stored as either 1s or 0s, quantum bits can be both at once. Which means that the more qubits you have the more exponentially powerful its computations become.
The Encrypted Life
Today, encryption is more integral to our daily lives than ever before. Plenty of things around you are using sophisticated encryption technology right now in order to keep you safe. All without you knowing it. It’s important to appreciate how much encryption has done for us today and the long road we took to get here. The big journey is actually ahead of us.
As we become an ever more digital world and begin to integrate machines into our bodies and let automation take over, data integrity will become a literal case of life or death. Hopefully, encryption will keep pace in this changing world. Allowing us to thrive rather than suffer a major disaster.
What do you think about Encryption History? Let us know in the comments below. To get instant tech updates, follow TechNadu’s Facebook page, and Twitter handle.