What is Quantum Cryptography Anyway?
With a few special exceptions, modern encryption is essentially unbreakable. There is not enough time or energy in the universe to break the type of encryption that’s considered standard these days. Does this mean that the problem of encryption is solved and everyone can relax?
The answer is of course that things are far from over. For one thing, although brute force cracking of encryption is impractical, some researchers may still find weaknesses in the encryption algorithms themselves. This has happened several times in the past. However, it’s usually just a case of developing or scaling up a different algorithm that has not yet been compromised.
The second event that might break the entire existing system of digital encryption down is the advent of entirely new computing technologies.
The Age of Radical Computing
Scientists and engineers are tirelessly working on potential approaches to computing which promise to blow away the current performance ceiling with a vengeance. We're talking about building computers that use photons, DNA and the spooky effects of the quantum realm. Problem-solving machines that take a completely different approach to solving problems. Not just problems that are hard for the conventional computer, but also ones which are literally impossible.
The most promising of the various potential computing approaches is quantum computing. Which is what I’m doing to try and get a grip on in this article. To understand what makes quantum computing special, however, we need a quick recap on how conventional computing works.
How Conventional Computers Work
The device you are using to read this article right now (assuming you didn’t print it out or something) is an example of a conventional computer. It uses a microprocessor containing billions of microscopic devices known as transistors.
A transistor is the most fundamental semiconductor device in computing. This little marvel replaced the vacuum tube in early computers and other electronics. Because transistors can act as a switch, being either on or off, you can use them to build logic gates.
Logic gates can be used to build logical operations. Thanks to a number system known as binary, you only need the numbers 1 and 0 to represent any quantifiable value. Binary also has the significant advantage that it combines arithmetic and logic into one symbolic system.
Throw all of these elements together, and you have everything you need to make the incredibly sophisticated microprocessors today. The critical thing to remember here is that all of the sophisticated capabilities of the computer you are using right now only boils down to the numbers 1 and 0. The fundamental element of binary computing known as the bit.
It's also worth noting that any calculation a conventional computer can do, can also be done by a human being on paper. Their immense speed and efficiency mean they can do in seconds what would take error-prone humans years, but fundamentally computers and humans do the same math.
Conventional Computers and Encryption
So since conventional computers can basically only do the same math as humans (although much faster), it means the approach to breaking through modern encryption is pretty much how we would do it.
Encryption algorithms are designed in such a way that you indeed can't reverse engineering them and unscramble the information you want. Unless that is, there's a flaw in how the algorithm works. This severely reduces the level of randomness in the scrambling process.
Given that we don't know of any such flaws in an encryption method, the only way to crack the code is through brute force. The computer tries every possible key combination for the encryption. It's basically guessing systematically, but at incredible speeds.
The fight against increasing computer power has been to increase the randomness of the keys (their entropy) and the number of possible key combinations. Since the number of combinations scales exponentially with key length, even the fastest computers in the world can't possibly crack the keys in any sort of useful time frame. This fundamental fact is what keeps information secure and the web operational. However, what if there was another way which could cut out the millions of years it would take conventional computers to crack the most robust encryption? That's where quantum computing comes in.
How Quantum Computers Work
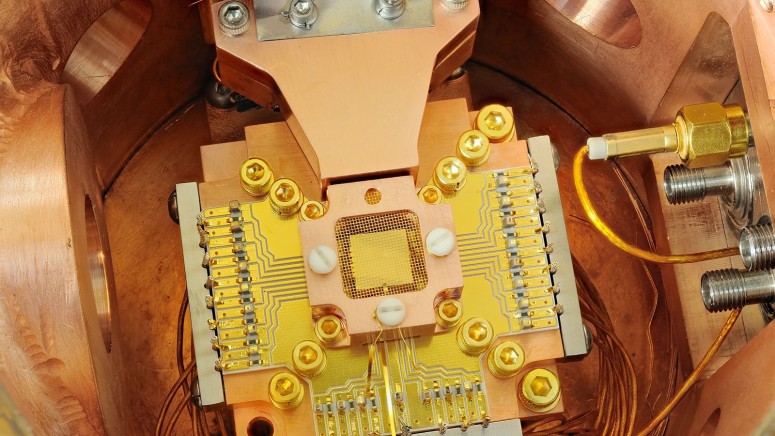
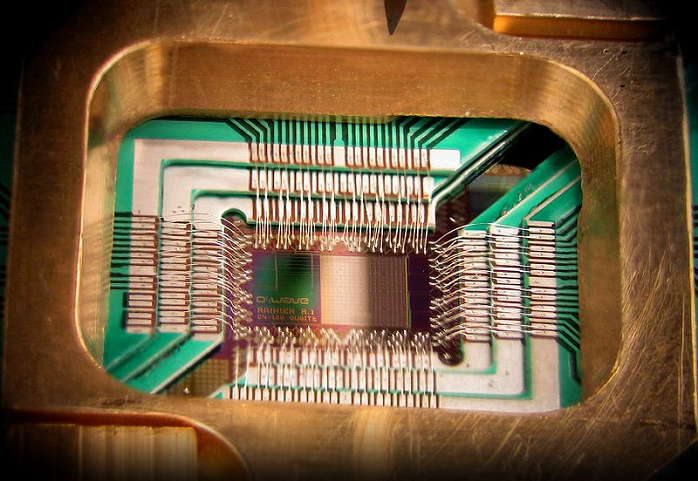
By D-Wave Systems, Inc. (D-Wave Systems, Inc.) [CC BY 3.0 (https://creativecommons.org/licenses/by/3.0)], via Wikimedia Commons
As you observe the universe at smaller and smaller scales, they rules we observe seem to change. So when you observe the motion of physical bodies in everyday life, Newton's classical physical laws apply perfectly. If we observe extremes of gravity and speed, however, they start to break down. That's when Einstein's theory of relativity helps us understand and predict the world. On the subatomic level, quantum theory is where it's at. It's a freaky realm where things pop in and out of existence. They appear in two places at once or everywhere at once. Those are just a few examples and, no, I don't really understand it either.
I don't think we should feel too bad. Celebrated physicist Richard Feynman supposedly quipped "If you think you understand quantum mechanics, you don't understand quantum mechanics." Einstein thought it was "spooky" and physicists are still trying to get their heads around it.
The Core of the Matter
The point is that the fundamental particles that make up our universe don't act like small versions of things like planets or baseballs. They act according to their own weird rules. However, these rules are highly predictable. It basically surprises everyone that despite how counter-intuitive the rules of the quantum realm are, experiences are highly precise and predictable.
So what does this have to do with computing? Well, it turns out that you can make something called a qubit with this knowledge. This quantum-bit is to the quantum computer as the binary bit is to the classical computer. However, where the conventional bit can only be a 1 or 0, a qubit can be both at the same time. This is a phenomenon known as superposition and is a fundamental feature of quantum mechanics. Also, qubits are subject to quantum entanglement, which means that the relationship between qubits is also computationally useful. As you add more qubits, the complexity of the system scales exponentially, not in a linear way.
Single atoms are used to represent a qubit. Since qubits can store all states at the same time, it means bit-for-bit quantum computers have a massive speed advantage over conventional computers. Moreover, the energy levels involved are theoretically orders of magnitude less than that needed in traditional computing.
While this means that we might have computers a million times faster than what's possible today, quantum computing has some profound implications for current encryption technology.
Quantum Computers and Encryption
As I said earlier in this article, the main reasons current encryption is unbreakable comes down to time and energy costs. So if computers became several orders of magnitude faster and started using a tiny fraction of the energy to compute compared to current standards, encryption could be in real trouble.
Quantum computers, such as the D-Wave, already exist. However, they don't possess enough qubits to crack modern encryption yet.
The most advanced quantum computer at the moment has 2000 qubits. In 2011 that number was 128. According to Google what the quantum computer they tested did in one second would take a desktop PC 10,000 years. However, current quantum computers are not general-purpose machines. They are built to solve particular problems. However, how much faster they can complete the tasks they are made for is mind-blowing.
At some point in the future, a quantum computer may be developed that will crack encryption keys in the blink of an eye. No one knows when that will be. According to one Forbes article, it might be as early as the 2030s. However, a breakthrough can happen at any time. It could be a real crisis for data security.
Quantum-resistant and Quantum-safe Encryption
Although the problem is still only theoretical, plenty of people are working hard to invent new forms of encryption that will stand up to the might of future quantum computers.
Quantum-resistant encryption doesn't use any of the core mathematical problems current encryption does. While those are very hard for conventional computers to work through, they are trivial to a sufficiently powerful quantum machine.
This generally only applies to public key encryption. Existing symmetric encryption methods are still hard for future quantum code-breakers to crack. Key lengths can also be increased to compensate for advances in quantum power.
Quantum Cryptography
So that's the issue of breaking current encryption with quantum cryptography in a nutshell, but that's far from the end of quantum computing and cryptography.
You see, quantum computers may also allow us to create quantum encryption. The various strange, wonderful and spooky aspects of quantum computing provide scientists, engineers, physicists and other related eggheads lots of new toys. Some of them can be applied to cryptographic tasks, and that's where things get exciting.
Quantum Key Distribution
As you may already know, one of the most significant problems we face in modern encryption is sharing encryption keys. Both ends of the communication channel require a key to decrypt what's being sent to them.
For example, when you set up a WiFi passphrase, you can install it directly on each machine on the network. It doesn't have to pass through unsecured channels. If you want to send an encrypted email to someone, however, you need to figure out a way to give them the decryption key without it getting snagged on the way there.
The best solution we have today is public key encryption. Where there are two keys, and you keep one secret. The public key can be used to encode messages, but you need the private key to decode them.
Quantum Key Distribution uses the unique nature of quantum mechanics to establish a shared key between two communicators. If a third-party try to eavesdrop, the process fails, and everyone is alerted. Once the keys are established, they can go on using conventional strong symmetric encryption. Even better, this method of key distribution can't be compromised using quantum technology. QKD may one day replace public key encryption, which also happens to be most vulnerable to quantum cracking. So it could kill two birds with one stone.
Quantum key distribution is the most mainstream and developed application of quantum cryptography. It's fair to say that this key distribution method is essentially quantum cryptography's killer application. It works perfectly alongside conventional symmetric key encryption methods.
Other forms of Quantum Cryptography
While quantum key distribution gets all the attention and is the most obviously useful application of the science, there are many different ways that we might use quantum computers to encrypt information.
For example, quantum coin flipping is a theoretical method of securing a communication channel between two communicators that don't trust each other. Useful, if they ever get it to work.
Position-based quantum cryptography is an application of the technology where only those at specific geographic locations can communicate. So you know that you are talking to someone at a verified position.
Apart from QKD, just about all quantum cryptography protocols and applications are theoretical. Either the hardware to make it work doesn't exist yet, or no one knows how to do it even if it did. Never say never, though! Living in a Post Quantum World.
Living in a Post-quantum World
It's hard to articulate all the different ways since the advent of practical quantum computing will change things. If we look at the radical way that modern conventional computers have changed our lives since the Second World War, it may provide an inkling. However, as incredible as that leap to develop was over just a few years, you haven't seen anything yet.
There are plenty of severe problems that would take too long to complete using conventional computers. Some problems are just impossible in principle. A high-performance future quantum computer would merely solve these problems instantly.
Diseases that require the simulation of complicated processes might now be cured. Complex engineering problems, energy issues, and other tough design questions could be optimized instantly. Nothing in our world would escape the power of quantum computing. Machine learning, in particular, will experience an extreme revolution.
The post-quantum computing world is one of the apparent miracles, and the 2030s are just around the corner. We have to be careful that a new and incredibly powerful technology doesn't end up damaging our privacy and security.