When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works.
The Best Ways to Encrypt Internet Browsing
The illusion that you’re alone and away from prying eyes when you browse the web is a strong one. After all, one of the first things we were told when the internet first came to mainstream public attention is that it provide an anonymous platform. Your handle protected your identity.
Well, it is true that the internet has done more for free speech and anonymous whistleblowing than any other technology that I can think of. That doesn’t mean you are enjoying those benefits just by virtue of being online.
In fact, there has been a war on anonymity and personal information for years now. Social media is one of the biggest culprits. These are services that literally make their money by getting you to volunteer as much of your personal information a possible. This is then sold to advertisers and other organizations hungry to use big data for various purposes.
Clearly if you sign up for social media, you’re voluntarily giving up on anonymity, but what about your internet use in general? Every data packet you send and receive passes through thousands of other computer systems. Your ISP, for example, can see just about everything you do. Which means that anyone who gets access to their records can tie you to that internet activity. That is unless you encrypt your internet browsing!
Securing Your LAN
Believe it or not, one of the first places that someone might intercept your web browsing isn’t on the other side of the world, but just a few feet away. It could be someone in an adjacent apartment or hackers who practice something called Wardriving. If a person should find that your wireless LAN connection (WiFi) is not secured then they can get a lot of sensitive info about your browsing activity.
The good news is that your WiFi router should have come with WiFi encryption enabled out of the box. If you have to put in a password to access your WiFi then you have a secured connection. As long as it’s using WPA2 to handle the encryption. Consult your router’s manual to find out how to check this.
Even if your WiFi is secured, it won’t mean much if you’re using a weak password. These days most new routers will ship with a strong password already in place. It’s usually on a sticker underneath the unit. If you changed this password because you thought it would be too hard to remember, you should change it back. Weak WiFi passwords can be broken with relative ease. So put up with the minor inconvenience of having a strong password.
Using HTTPS
HTTPS is currently the de facto standard when it comes to securing the information that travels between your browser and the web server of the website that you are visiting. When you look at the space to the left of the URL in the browser’s address bar, there should be a little-closed padlock to show that the site is secure. The website itself should start with “https” as well.
When a site is secured with HTTPS there is almost no chance that anyone intercepting the data will be able to make sense of it. It’s thanks to this technology that it’s safe to shop online and use many modern services.
Not all sites have made the switch to this encrypted website format, however. So browsers like Google Chrome have started to take a zero-tolerance stance on this issue. If you try to visit a site that’s not secured in the latest version of Chrome, you’ll have to click through several large warnings. There’s a good reason for this too since unsecured sites are liable to leak your data to dodgy third-parties looking for holes in the web’s security.
So it’s a great idea to heed the advice of the likes of Google and avoid sites that haven’t secured themselves with HTTPS. However, if you really must visit a site that’s not secured, you can use a browser plugin known as HTTPS Everywhere. It’s made by the Electronic Frontier Foundation and comes in the form of a plugin for the most popular browsers.
Using this plugin you can get the benefit of HTTPS encryption on sites that don’t have it set up at the moment.
Using Tor
HTTPS is a reasonable defense for everyday encryption needs for your online browsing. However, sometime you may want to visit a site or send information to someone through a website while absolutely needing anonymity.
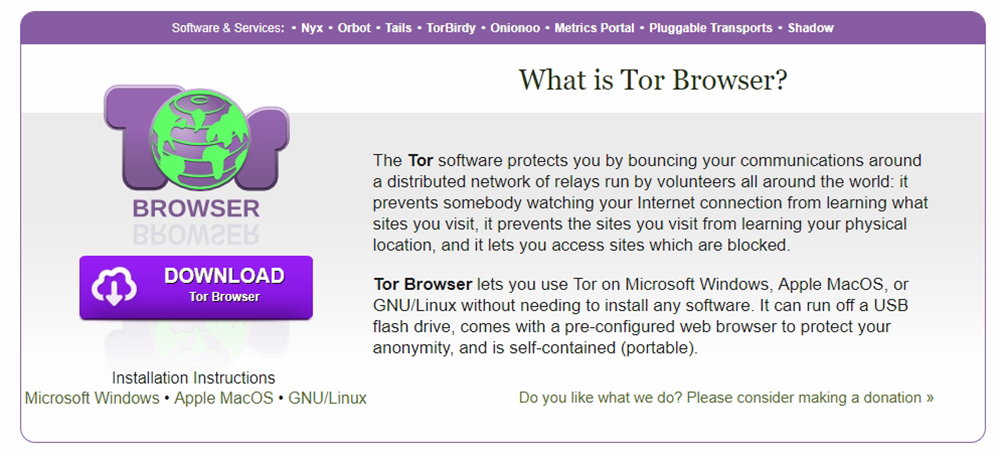
Using Tor (the onion router) is one of the most effective ways to use encryption and a sophisticated network of computers to completely hide your identity and location.
The Tor network is made up of thousands and thousands of computers. These are made available thanks to volunteers. When you access a website using Tor, the data does not go straight to your computer, but through a random zig-zag path through the network.
The data itself is encased in multiple layers of encryption, like an onion, and at each hop, through the network, another layer is stripped away. By the time it gets to the last computer in the chain, only the original data remains and that can then be sent on to the destination server.
You have two choices when it comes to using Tor. You can configure your existing browser to use the Tor network, or you can download a modified version of FireFox already set up for Tor.
Getting Tor
I strongly recommend that you use the pre-packaged Tor browser. Configuring Tor is not a simple process and if you get it wrong you are in real danger of exposing yourself. So getting the official Tor browser makes a lot of sense. In any case, it's much easier to keep track of things if you separate Tor browsing from other kinds of browsing that doesn't quite need this much security.
Tor is also quite unsuitable for things like streaming video and other bandwidth-heavy applications. Thanks to its nature, you'll experience slow speeds and lots of lag. Tor is really only a good idea when you absolutely must have anonymity.
The Windows installer works like just about any other application that you'd install. Just double click the executable and choose an install location. You should know that Tor is a portable app. This means that it's not dependent on a specific system to run. Instead, it can run from anywhere like a flash drive. That makes it very handy if you want to use something like an internet cafe, where your privacy could really be in doubt.
Using a VPN
The best way to secure your internet browsing against interference from third parties is a VPN. That’s short for Virtual Private Network and that’s pretty much what it is. You see. The internet is really just millions and millions of computers all connected to each other with network hardware. When you buy something from Amazon, there’s no direct dedicated line between your computer and theirs.
The data packets have to travel through numerous other devices in order to get where it's going. All of those computers that pass the data along can easily see where the packets come from and where they are going. These days, thanks to HTTPS, they can’t see the content of the data, but it’s still a problem.
For example, you might want to visit a banned site in your country without getting in trouble for it. Perhaps your ISP throttles certain kinds of traffic, such as torrents. These are just two good reasons to keep others on the internet in the dark when it comes to what you choose to do and where you go on the net.
VPN technology does all of this and more. It creates a virtual, dedicated line between you and the VPN provider. No one outside of this connection can know anything about what you are doing. Even better, the service that you connect to can’t know your true internet address or location. Using a VPN is super easy, they are affordable and are becoming virtually essential. They are especially important to have if you connect to public WiFi hotspots, where other people on the same network can intercept your information as it leaves your computer on the way to the internet.
Finding and Installing a VPN
The most common way to use a personal VPN these days is to download its client or mobile applications. Before you do either of those things, you should start your VPN subscription. This involves signing up on their website and then making the first payment. The more months you pay upfront for, the less you'll generally pay overall. However, try out your chosen VPN for a month before giving up your cash.
Once you've installed the client or app in question you can just run it. Log in with your credentials and choose where you'd like to connect to.
Once the app reports that you are securely connected, you can browse wherever you want. No one is going to be watching you. At least, if they try they won't get to see anything.
Choosing right can be tricky with VPNs. We specialize in reviewing VPN services for various use cases. Be sure to have a look at your VPN reviews to help you pick the best one. The best overall choice for most people is ExpressVPN in our opinion.
Out with the Bad, in With the Good
Getting into the habit of auditing your web browsing for potential privacy weak spots is a great habit to have. We spend so much time of our lives on the internet that we should really be doing it more safely. In this age, more than ever, you need to take your privacy seriously. Unless you want to be the next unlucky victim of harassment or identity theft.