Cisco Fixes High Severity RCE Flaw on Two Small Business VPN Routers
- Cisco pushes firmware update to fix a highly critical RCE flaw affecting two small business VPN routers.
- The models are RV132W and RV134W, two widely used routers that support large volumes of remote work right now.
- The identified flaw is most likely not being actively exploited in the wild by malicious actors.
Cisco has fixed a high-severity (CVSS-7.2) flaw (CVE-2021-1287) on two small business ADSL2 and wireless VPN routers, namely the RV132W and RV134W. The problem lies in the web-based management interface, which could allow an authenticated remote attacker to execute arbitrary code on the target device. The result would be a restart action, so exploiting it systematically could put the device to a DoS (denial of service) condition.
The stack-based buffer overflow was discovered and reported to Cisco by researcher Shizhi He, of the Wuhan University. While the DoS condition appears to be the main case, a complete compromise of the vulnerable system could happen too.
The two models are being widely deployed right now as many small businesses were called to pass to remote working models due to the pandemic, and those VPN routers provide an excellent platform through which to connect to remote networks securely.
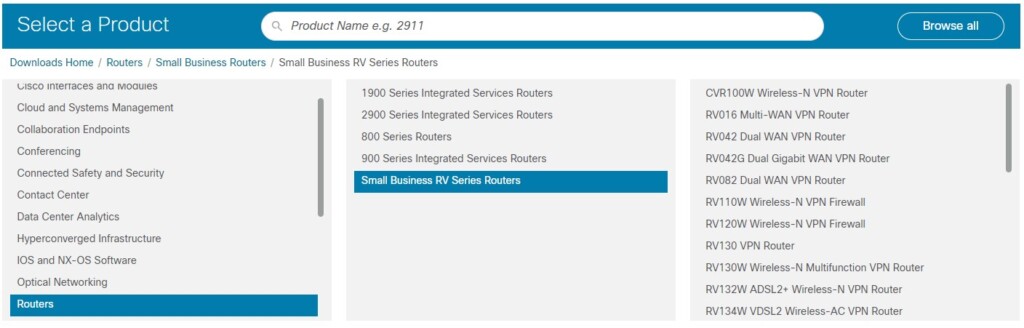
This vulnerability affects the following Cisco devices:
- RV132W ADSL2+ Wireless-N VPN Routers if they are running a firmware release earlier than Release 1.0.1.15
- RV134W VDSL2 Wireless-AC VPN Routers if they are running a firmware release earlier than Release 1.0.1.21
There are no workarounds for the problem, so the only solution right now is to apply the patch. The Cisco Product Security Incident Response Team (PSIRT) hasn’t seen any exploitation of the identified and fixed flaw in the wild. However, this doesn’t mean that you should postpone the application of the update. To get the latest firmware update, go to Cisco’s Software Center, select your router model, and download the file.
Remember, firmware upgrades may restore all your settings to default values, so after upgrading, you should check all settings, especially those related to security and remote access. Also, during the firmware upgrade, it is of utmost importance not to fiddle with the power input or press the reset button. Otherwise, you may end up with a bricked device.