Chrome 77 Released with a New Guest Mode, and Google Unveils DoH Plans for 78
- Chrome 77 arrived with a new guest mode that empowers administrators to set the usage context.
- Google has dropped the bomb by introducing DoH as an experiment in the first snapshots of version 78.
- Users are happy with where things are going, but ISPs and security experts warn about the repercussions.
The latest major version release for the world’s most popular internet browser has landed. Chrome 77 has arrived with a new “guest mode”, that enables system administrators to set up specific configurations for Chrome browsers used in a network. These admin configurations cannot be bypassed by users, as they are mere “guests”, using the browser in incognito mode. Other than that, the EV (extended validation) certifications indicator has been removed from the address bar, 52 security-related flaws have been fixed, and several under-the-hood improvements promise a better performance now.
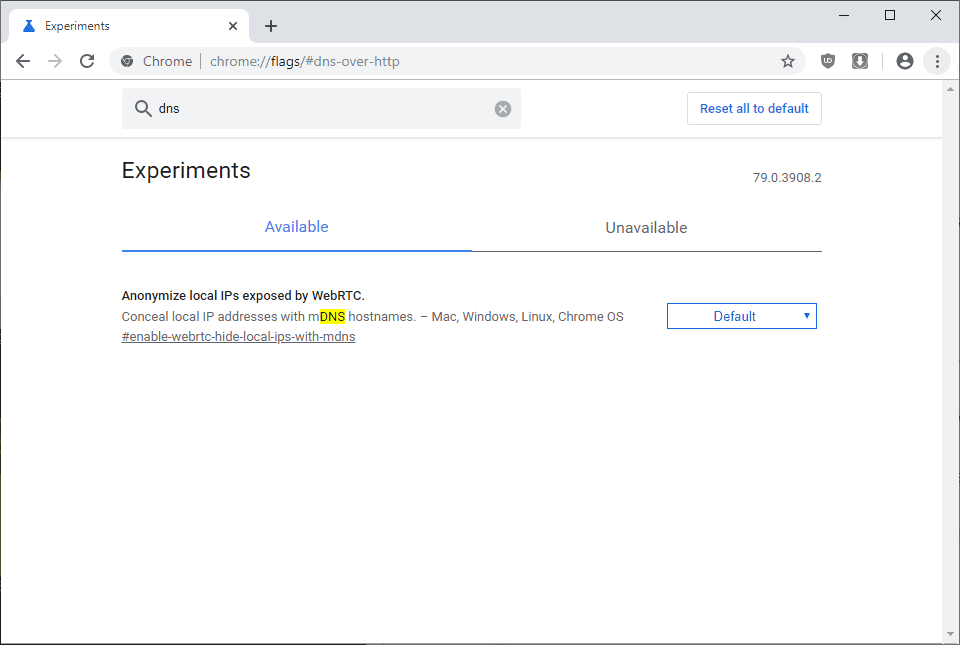
While version 77 is a welcome upgrade, it is the announcement of the experimentation with DNS-over-HTTPS that is planned for 78 that steals the show right now. For this reason, Google has already added a new UI element in 77 that allows users to opt-in and out of experimental features like the upcoming DoH. Although this new feature will be introduced in a purely experimental context in version 78, Google could decide to make it the default mode at any point in the future. That is especially if they notice that a large number of users will opt-in to use it.
Source: ghacks.net
As we discussed only a few days ago, Mozilla has the same aspirations for Firefox, planning to launch DNS-over-HTTPS in the next major version as an experimental, optional feature. Mozilla has already tested the new private browsing mode in the U.S. and found it reliable and stable enough. DoH prevents user tracking and domain blocking, as all DNS traffic becomes invisible to ISPs, sniffers, firewalls, and filters. With Firefox moving on with such a privacy-boosting feature, Chrome has no other option than to do the same, otherwise, they run the risk of losing large numbers of users to the competition.
Google will start the experimentation by collaborating with Cleanbrowsing, Cloudflare, DNS.SB, OpenDNS, and Quad9. The experiment will run on all platforms and will involve only a small fraction of Chrome users. In the case of any errors or resolving problems, Chrome will revert to the regular DNS service.
ISPs have already expressed their concerns with these plans, criticizing Mozilla and Google, and warning about the security risks that come with DoH browsing. Firefox has already responded to the concerns by claiming that they will respect ISP blocks and try to make malware filters work safely with DoH. Google has not announced anything about how they plan to deal with the security risks that arise from the use of DoH, but we’re sure that they will do it very soon.
Will you be using DoH, or do you prefer to stay with OS DNS settings? Let us know where you stand in the comments down below, or on our socials, on Facebook and Twitter.