Chinese Hacker Group ‘APT20’ Able to Bypass 2FA in Corporate VPNs
- APT20 is reportedly able to bypass 2FA to log in to corporate VPN products.
- The group begins the infiltration by exploiting unpatched vulnerabilities in JBoss.
- In most of these cases, the hackers roam in the corporate networks undetected.
Security researchers working for the Fox-IT report that they have witnessed the capacity of ‘APT20’ to bypass two-factor authentication and enter into corporate networks. The Dutch researchers have been following the Chinese hackers for a while, monitoring their online moves and taking note of the industries they prefer to target. As they report, the fields that suffer APT20 attacks are mainly government entities, aviation, finance, energy, healthcare, and insurance firms. More specifically, the hackers are reportedly targeting the JBoss Enterprise Application Server which is extensively used by large organizations.
According to the findings presented in the relevant report, APT20 spent the last two years in compromising unpatched JBoss via known vulnerabilities, accessed servers to install web shells, and indulging in lateral movement inside the networks. The hackers actively tried to dump admin user credentials in order to infiltrate deeper, with special attention paid towards the stealing of VPN passwords. Using corporate VPNs to establish backdoors is safer and more stealthy for the malicious actors, so this is what they are going for. Of all their attack methods and smart tricks though, the most impressive one was the bypassing of two-factor authentication layers that were set for added security.
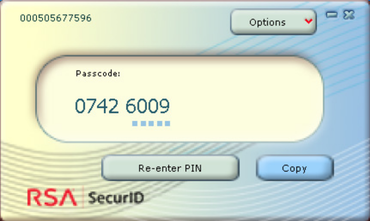
Fox-IT analysts can only speculate about the exact means by which the hackers managed to do this, with the most probable scenario being the stealing of an RSA SecurID software token from a system that they had compromised earlier. This would enable them to generate one-time codes, essentially providing a way around 2FA. This trick can work mainly due to the lack of system-specific value validation, alleviating the actors from having to physically access the compromised device and capture the token.
Source: ZDNet
The researchers named the particular operation “wocao” which is a curse word in Chinese Mandarin slang. The hackers wrote it in frustration when they lost access to one of the web shells they had planted in the systems of an organization which was the first to call Fox-IT for help. This incident highlights the importance of patching your systems, having threat and network infiltration detection tools in place, and following a network segmentation approach when setting it up. APT20's methods enable them to stay in the compromised networks undetected for long, making this campaign particularly dangerous for the organizations.
Have something to comment on the above? Let us know of your thoughts in the section down below, or join the discussion on our socials, on Facebook and Twitter.