CafePress Data Breach Exposed 23.2 Million Customers
- CafePress exposed the sensitive information of millions of their customers, due to a February breach.
- The revelation came from “Have I Been Pwned” who actually sent notices to the exposed people.
- The company has not admitted the breach yet, but they have imposed a mandatory password reset.
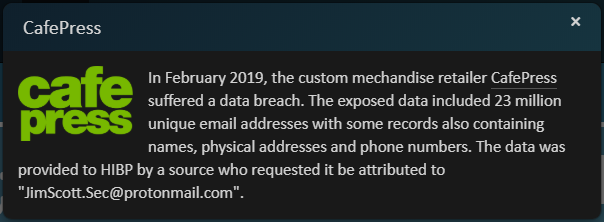
CafePress, the popular custom t-shirt online market has suffered a data breach which exposed the sensitive information of 23.2 million of their customers. The incident occurred back in February 2019 and was just discovered by security researcher Jim Scott who noticed the relevant bundle on the WeLeakInfo search engine. He actually searched for it following a tip from Troy Hunt, the owner of the “Have I Been Pwned” service, who had heard that it was circulating. As confirmed by the researcher, a pack containing nearly half a million of these accounts is already on sale on darknet forums.
image source: haveibeenpwned.com
The exposed information includes the full names of the customers, their email addresses, the passwords, physical addresses, and phone numbers. About half of the passwords are encoded with the now-obsolete base64 SHA1, so they are pretty weakly protected and bound to get decoded for exploitation. Those who accessed CafePress through Facebook and Amazon used third-party tokens for their login, so their passwords haven’t been compromised.
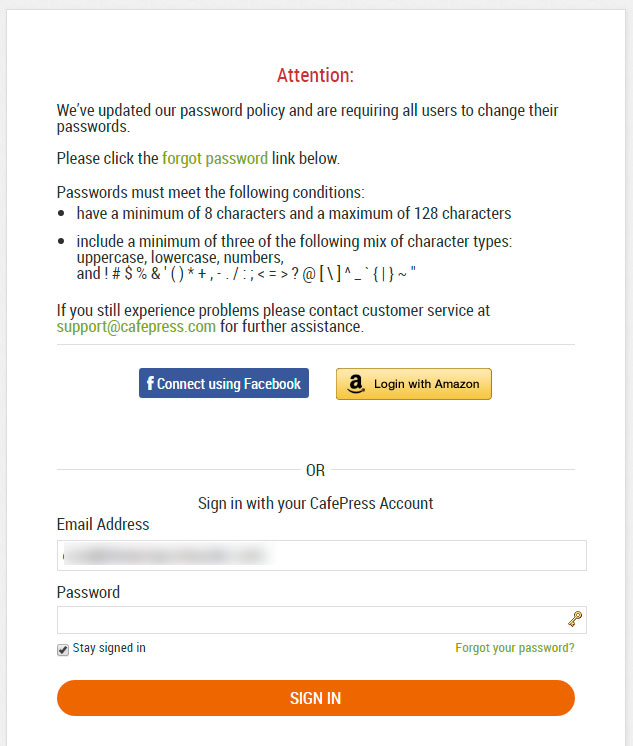
CafePress has not issued an official announcement on the revelations made by Troy Hunt and Jim Scott, so the breach hasn’t been confirmed by the e-commerce platform yet. However, they did force a password reset to their customers who tried to log in to the website, albeit there was no mention of any breach has happened. They simply stated that the password reset is occurring in the context of an update in the company’s password policy.
image source: bleepingcomputer.com
We trust the way that Troy Hunt is confirming the validity of the breaches, so we take for granted that the user data was indeed compromised. That said, CafePress should have circulated notices of the breach to the 23.2 million users who were affected by the incident, and they should have done so since February. Already, many thousands of them have had their information sold to crooks and may have possibly fallen victims to credential stuffing attacks on other platforms.
As always, using a unique and strong password for each platform you log in to is a solid way to limit the damage when data breaches like this one occur. Remember, if you have used your CafePress password across multiple websites you should change it globally now. Using a password manager to generate a set of fresh and powerful passwords would be a good idea now.
Have something to comment on the above? Let us know of your view in the comments down below, or on our socials, on Facebook and Twitter.