Zero Day WhatsApp Exploits Payout Now Doubled to $1 Million
- Zerodium doubles the payouts for mobile vulnerabilities reported by bounty hunters.
- Security researchers have an increasingly harder time to hack OSes and apps, but higher payouts keep the reporting rates high for now.
- A combination of reasons has formed the basis for the payout rise, reaching millions in some cases.
Zerodium, a company that acquires functional exploits and pays rewards to the tipsters has doubled the price of the bounty payouts. According to their new price catalog, security researchers that share details about high-risk vulnerabilities will now get compensated in the millions. Zerodium then passes this information to interested parties such as the affected software developers, governments, or national cyber-security agencies, and so everyone except cyber-criminals is happy.
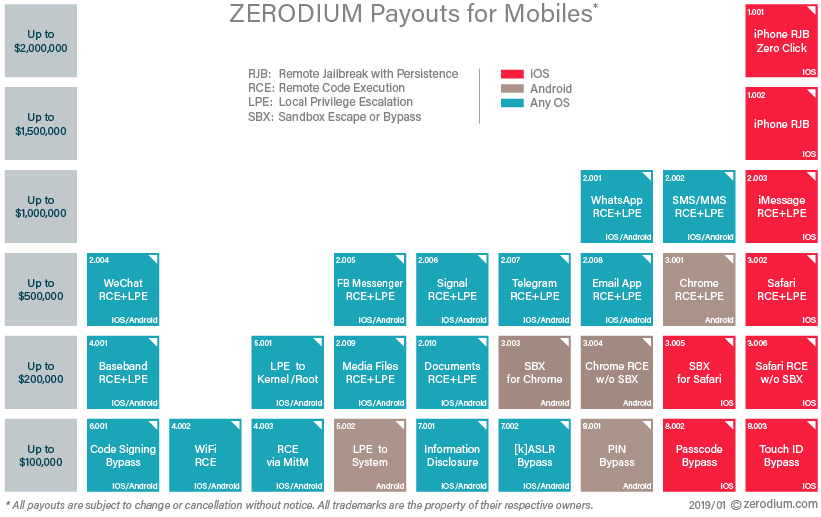
Indicatively, Zerodium is paying up to $2 million for high-risk vulnerabilities concerning iOS remote jail-breaking, $1 million for WhatsApp, iMessage or SMS remote code execution, $200k for Chrome or Safari sandbox escape, and up to $100k for local pin/passcode or Touch ID bypassing occurring either on Android or iOS. The bounty payouts for mobiles have reached the level of those that concern server and desktop systems, and in some cases have even surpassed them by far.
Up to date Zerodium Payout table
This price increase for exploits is not reflected only on a single bounty hunting company, as others such as Crowdfense and Azimuth have gradually increased the amount of money they pay to security researchers as well. The reasons behind all this are multiple, but the most important ones can be summed up to the following three:
- Mobile platforms are getting increasingly more secure and thus harder to crack. This makes the amount of the reported vulnerabilities less, so bounty hunting companies have fewer risks to report and sell to the concerned organizations and agencies. According to the “offer and demand” rules of the market, the prices for tips should naturally go up.
- Mobile users are getting more, as the smartphone market is finding new areas to expand to. This means that every vulnerability has the potential to affect a much larger number of people, and so a tip is valued higher.
- Security monitoring agencies and customer protection committees have gotten much stricter lately, hitting non-compliant software developers and social media platform owners with hefty fines. This increases the value of security tips, as timely fixes can prevent security-related damage outbursts.
Not all of these tips are used for protection though, as many government agencies need them for the opposite, which is to spy and intercept messages through chat platforms for example. As these tools get more secure without openly providing any type of backdoor for governments, the cost of acquiring a tip that will allow them to continue their operations increases.
Where do you stand on the above? Let us know in the comments section below, and feel free to share this story through our socials on Facebook and Twitter.