Yet Another Massive Data Leak From a Marketing Company Exposes 126 Million U.S. Citizens
- A young American marketing company has exposed hundreds of millions of PII records online.
- The details include email addresses, home addresses, phone numbers, and full names.
- The source of the data is a mystery, but the firm won’t be able to get around the consequences.
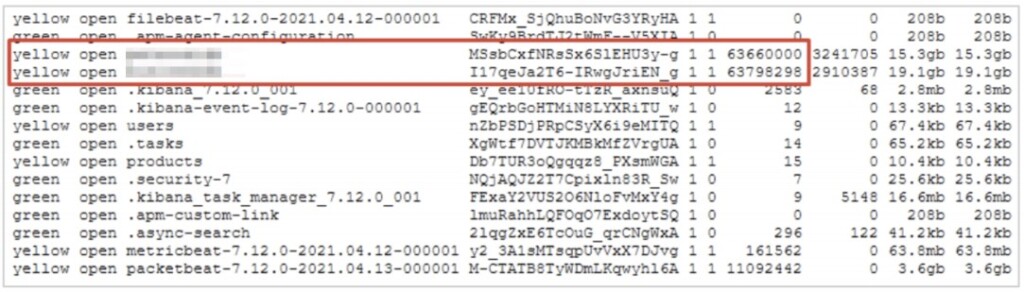
‘OneMoreLead,’ a B2B sales and marketing SaaS company, has exposed an ElasticSearch instance online without securing it properly, essentially leaking away 34 GB of data containing 126 million records. If no duplicates are to be found in the data set, the total number of people who may have been exposed due to this incident is 126 million citizens, mostly from the United States. The leaked data was discovered by the vpnMentor team, led by R. Locar and N. Rotem, who have shared their report with TechNadu prior to publication.
The data was found online on April 16, 2021, and four days after that, the owner, as well as AWS, were both contacted. The database was taken down the next day, on April 21, 2021. Although the company responded quickly, the impact remains severe as five days of exposure are more than enough for scrapping to have taken place. Also, the initial time of exposure remains unknown, so the estimation for the five days is really the best-case scenario in this case.
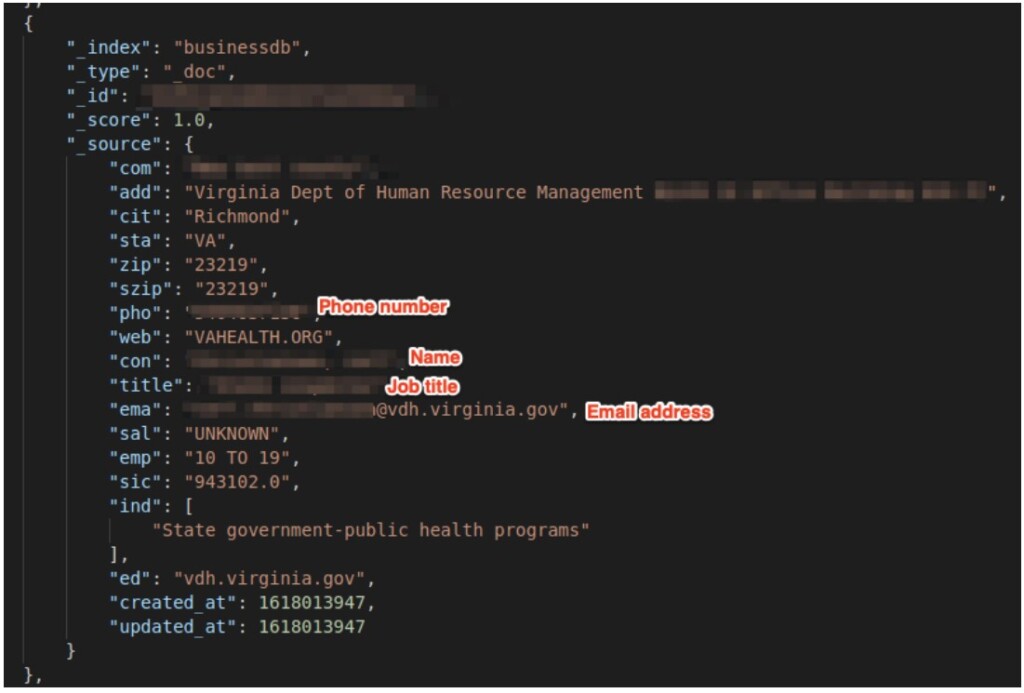
The data contained the following details:
- Full name
- Job title
- Personal email address
- Work email address
- Home device IP address
- Home address
- Work address
- Personal phone number
- Work phone number
- Employer
Some of the above may no longer apply as people change jobs, but the most crucial stuff found in the data set cannot be reset or changed. This incident raises the risk of having to deal with phishing, scamming, spamming, and social engineering attacks for the exposed individuals, so beware.
Locar and Rotem tell us:
The tricky part here is that OneMoreLead may have collected your data without you knowing about it. The company is new and small, having started only in April 2020, so it is unlikely that they scrapped all these records by themselves. Even their website appears partially incomplete at this point. Most likely, they bought the sets from elsewhere or even sourced them from dubious locations.
As the researchers point out, the data set appears to be very similar to a 2020 leak from a German B2B marketing firm named ‘Leadhunter.’ That company denied having any connection to the leak incident, so they were never proved to be the party responsible, and as such, they never faced any consequences. The case of OneMoreLead, though, will be different, as there’s no doubt about their involvement in this.