Zero-Day Vulnerability Found In WordPress GDPR Compliance Plugin
- Hackers are actively exploiting a zero-day vulnerability in the WP GDPR compliance plugin and creating backdoors to take over websites.
- The plugin is responsible for helping users make their websites GDPR compliant with ease and has over 100,000 users.
- The WordPress team has already patched the exploit, but users who have not updated the plugin are still at risk.
WordPress has become a major target for cyber attacks, and the platform is now facing its second major security incident less than two months apart. In September, a large number of websites on the platform were exploited using JavaScript code. Just two months later, roughly 100,000 website owners on the platform were at risk of being affected by a zero-day vulnerability.
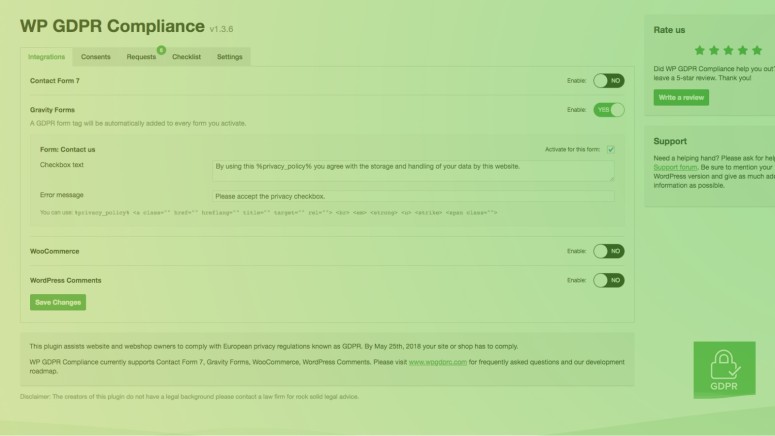
The WordPress vulnerability was found in the GDPR Compliance plugin which is a popular tool to help website owners follow data regulations set by the European Union earlier this year. The attacks happened three weeks ago after cybercriminals identified a vulnerability in the plugin and took advantage of it to gain access to WordPress sites and install backdoor scripts.
After a number of reports about websites being hacked landed on the WP GDPR Compliance forums, it was revealed that the exploit allowed attackers to install second-stage payloads on some websites and gain complete access. The plugin was removed by WordPress, and the security issues were eventually patched.
If you use the plugin and are on version 1.4.2 or earlier, you should update the plugin immediately. The latest version of the app contains patches for all the related issues, but many users are still running older versions and are at the risk of having their websites exploited.
Analysts from WP GDPR Compliance are still monitoring activity to detect any attacks. It is likely that opportunistic attackers are still on the lookout for finding websites that are using an older version of the affected plugin to take advantage of the security flaw.
What do you think about the recent exploit discovered in the WordPress plugin? Let us know in the comments below. Get instant updates on TechNadu’s Facebook page, or Twitter handle.