‘Windeln’ Has Potentially Exposed the Details of 700,000 Customers Online
- A popular children’s clothing and toy e-commerce platform has exposed the sensitive PII of 700 thousand of its clients.
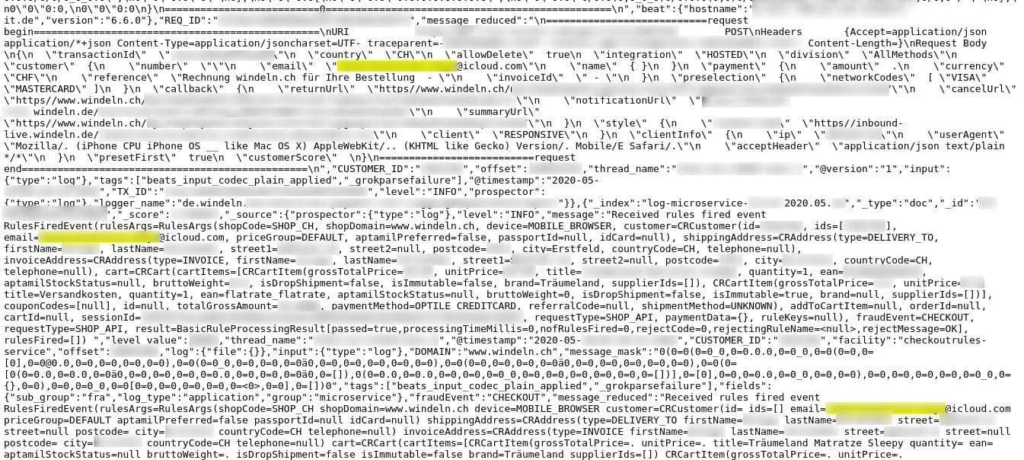
- The German shop named ‘Windeln’ was exposed to the ultimate level, as all internal network details and API login tokens were publicly available.
- The incident will invoke a GDPR investigation, and there is no way this will go by without a huge fine.
A German e-shop using the domains’ windeln.de’ and ‘windeln.ch’ has leaked a hefty 6.4 TB of data online, which corresponds to more than six billion records that affect about 700,000 customers. The shop is selling baby and toddler products and is also engaged in large-scale cross-border e-commerce business operations between Europe and China.
At the time of writing this, the “de” domain is offline, while the “ch” one is up, so this gives us an idea of where the jumble happened. Indeed, the researcher who discovered the dataset confirmed that the leaky server is located in France.
Source: Safety Detectives
This was a production server hosting an unprotected database that was storing data from May 24, 2020, including everything from API logs to customer details. More specifically, this is what was found by the researchers:
- Full names
- Email addresses
- Full postal addresses
- Telephone numbers
- IP addresses
- Windeln.de newsletter subscription mailing list
- Order and purchase details
- Payment methods (without payment information)
- Order invoices
- Information about users’ children, including their names, dates of birth, and gender information
- Amazon OAuth API login tokens
- Authentication tokens
- Partial listings of hashed passwords
- Internal logs including various employee details
- Records referring to sister site and brand Bebitus.com including website user account tokens
Source: Safety Detectives
This is pretty revealing both for the clients and the company itself, as there are way too much sensitive data in there. The only thing that’s (thankfully) missing are the payment details, but besides that, the exposure is quite extensive.
The question that arises now is, have any malicious actors access that data before the white-hat researchers did? This remains a question, but there are generally no signs that anyone else has exfiltrated the data.
Windeln is a relatively large firm that’s publicly listed on the Frankfurt stock exchange and had annual revenues of €82 million in 2019. Leaving their network exposed to hackers, infiltration, and takeover in such a way is embarrassing.
If you have bought anything on windeln.de between May 23 and June 23, 2020, be careful with how you handle incoming emails, phone calls, and SMS. Phishing, scamming, social engineering, and spamming are all included in the spectrum of dire possibilities.
Finally, you should contact the company and ask for further details on the incident, and then also report it to your local data protection office. Since Windeln is a Munich-based company storing EU-people data on French-based servers, the GDPR “Sword of Damocles” is now hanging above its head, and a substantial fine should be considered certain.
Read More:
- SoftServe IT Firm Hacked, Locked Down, and “Plundered”
- “Telmate” Prison Communications Exposes Personal Data of Millions
- The ‘Warner Music Group’ Announced a Credit Card Data Breach