Well-Intended Hackers Broke Into Fermilab’s Network and Accessed Sensitive Data
- Ethical hackers of the ‘Sakura Samurai’ group have broken into Fermilab’s network.
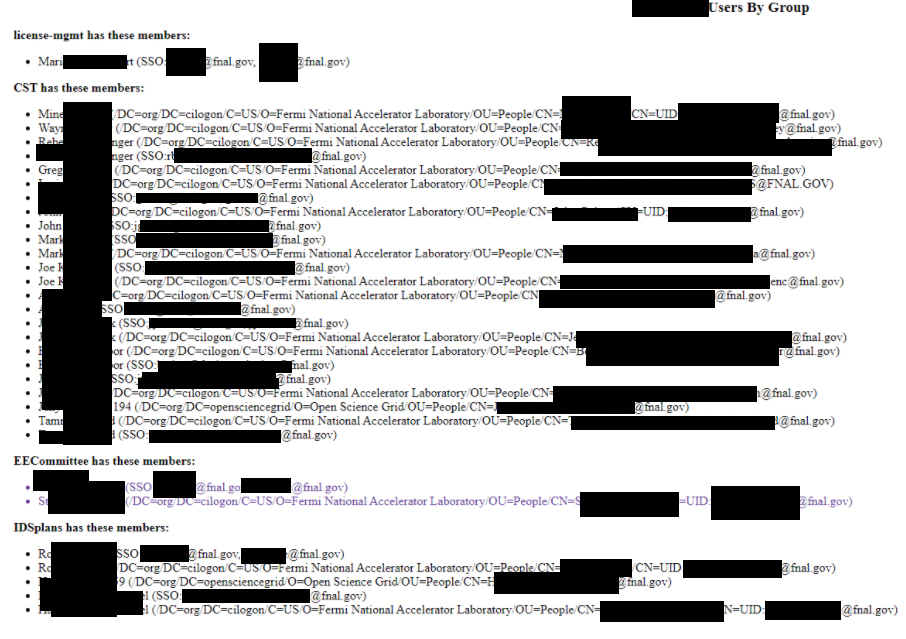
- The researchers found PII, network information, credentials, project data, and proprietary code.
- The potential consequences of this are dire, but all of the identified flaws have been reported and fixed now.
Members of the ‘Sakura Samurai’ security research hacking group have managed to break into Fermilab, accessing a trove of sensitive user information, ticketing systems, project servers, and also network information that would enable stealthy and unobstructed lateral movement.
The Fermi National Accelerator Laboratory, based in Illinois, is one of the most neuralgic points of research for the American scientific community. It manages an annual budget that is measured in the hundreds of millions of USD to carry out particle acceleration experiments that have led to important discoveries on four distinct occasions since 1977.
Of course, science at this level is typically open to global scientific teams, but the consequences of malicious access on Fermilab’s networks could be dire nonetheless. Apart from stealing proprietary code or accessing PII, an attacker could interrupt operations, plant malicious code that would fiddle with experimental results, and generally create the conditions for mind-boggling time and money losses for the program. This is why Fermilab has a vulnerability program in place, and that was enough for R. Willis, J. Jackson, and J. Henry to start digging.
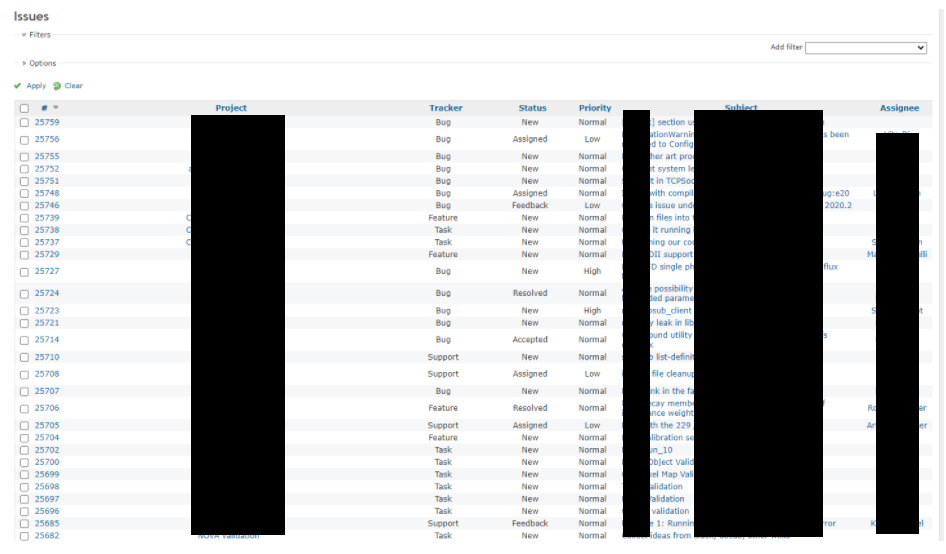
The ‘Sakura Samurai’ found a wide range of entry points, with the most promising one being an unrestricted subdomain that could be used to siphon tickets, project data, and account credentials. Many of the 4,500 tickets accessed had their own subset of valuable data, like project configuration and file attachments with sensitive info.
By using “basic” network scanning tools like nmap, amass, and dirsearch, the researchers explored more accessible servers, finding a web app that gave them access to all registered users and their details (full names, workgroups, emails, user IDs).
In similar ways, the team accessed an FTP server allowing anyone to log in without proper authentication, exposing data relevant to the “NOvA” experiment. This is an experiment exploring the possibility of the existence of evidence for an unknown symmetry of nature and the reason for the matter-antimatter asymmetry, which is a topic of debate for top-level physicists.
As worrying as the findings were for the team, Fermilab’s response was quick and to the point. All of the identified vulnerable endpoints were promptly fixed, so the problems have been addressed now. As for how long these security flaws may have been there and whether or not someone with malicious intentions accessed the Fermilab's network before the ‘Sakura Samurai’ team, we have no answer to that (yet).