US Contractor Trenchant Reportedly Linked to Global iPhone Hacking Toolkit Coruna
- Allegations: An exploit reportedly originated from Trenchant, the offensive cyber operations division of U.S. defense contractor L3Harris, developed specifically for Western intelligence collection.
- Hackers’ Hands: The iPhone exploitation framework designated Coruna was deployed extensively by Russian and Chinese threat actors.
- Executive Arrested: A former Trenchant executive was sentenced to several years in prison for selling trade secrets to a Russian zero-day exploit broker.
The Coruna iPhone exploitation framework was allegedly developed by U.S. defense contractor Trenchant, the offensive cyber operations division of U.S. defense contractor L3Harris, according to reports. Originally engineered by Trenchant, the software was developed exclusively for authorized Western intelligence agencies.
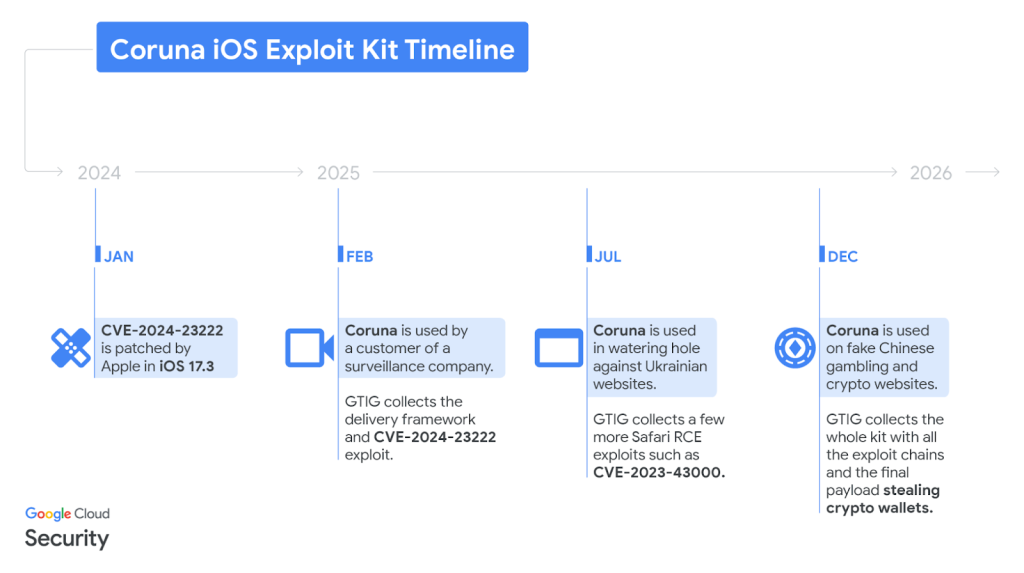
However, the advanced Coruna exploit chain subsequently leaked to unauthorized intermediaries, reaching Russian state-sponsored threat actors Chinese cybercriminal groups.
Russian Intelligence, Cybercriminal Exploitation
Two former L3Harris employees with knowledge of the company’s iPhone hacking tools told TechCrunch that Coruna was, at least in part, developed by Trenchant, adding that “Coruna was definitely an internal name of a component.”
Comprehensive analysis conducted by Google Threat Analysis Group (GTIG) and independent security researchers from iVerify confirmed that the 23-component toolkit was operationally deployed in targeted cyberattacks globally. One of the former employees mentioned that “many” of the technical details GTIG published were “familiar.”
Russian state-sponsored threat actors tracked as UNC6353 acquired the software and deployed it through compromised Ukrainian web infrastructure to target a limited number of nationals from a specific geolocation. Subsequently, financially motivated China-linked UNC6691 repurposed the exploits for global large-scale operations of cryptocurrency theft and financial fraud.
Escalating Cybersecurity Vulnerabilities
GTIG estimated that Coruna is currently used by multiple, unrelated threat actors. Officials said these powerful digital weapons could have provided adversarial actors with immediate exploitation capabilities against “millions” of consumer devices.
Peter Williams, a former senior employee at Trenchant, pleaded guilty to two counts of theft of trade secrets following accusations that over a 3-year period, he stole and sold at least 8 sensitive cyber-exploit components to a Russian zero-day exploit broker. He was recently sentenced to over 7 years in prison.
An ex-Trenchant employee said Williams fired them on allegedly false suspicions of stealing Chrome zero-days, which could mean this could be one of the several exploits sold, but this information is yet to be confirmed.
A New York fiber laser expert was convicted in November 2025 of stealing trade secrets for China, and CrowdStrike confirmed an insider threat incident linked to Scattered Lapsus$ Hunters.