US Authorities Tracked Down North Korean WannaCry Hacker
- US authorities trace back to a North-Korean programmer, Park Jin Hyok, as a hacker behind the WannaCry Malware.
- Park was also involved with the Lazarus Group, which seems to be a Government-sponsored hacking team, backed by North Korea.
- Seemingly due to human error, Park had entangled his real-world persona with the Lazarus infrastructure which led the US authorities to him.
US Authorities strung together a list of malware samples, domain names, emails, and social media accounts to finally put a pin on one of the Lazarus Group hackers. According to the US Department of Justice, Park Jin Hyok, a 34-year-old North Korean programmer is among the many individuals involved in recent malware attacks including the WannaCry ransomware outbreak in 2017.
It turns out that Park was an active member of the Lazarus Group, which is a government-affiliated hacking team. However, officials are of the opinion that Park was an employee of Chosun Expo Joint Venture, a government-owned company. The company had offices in North Korea and China. Park worked in the Chinese office which was in Dalian.
There, Park worked under the title of “developer” and “online game developer.” He specialized in coding skills related to ava, JSP, PHP, Flash, and also Visual C++, which is the language used to create most of Lazarus Group malware.
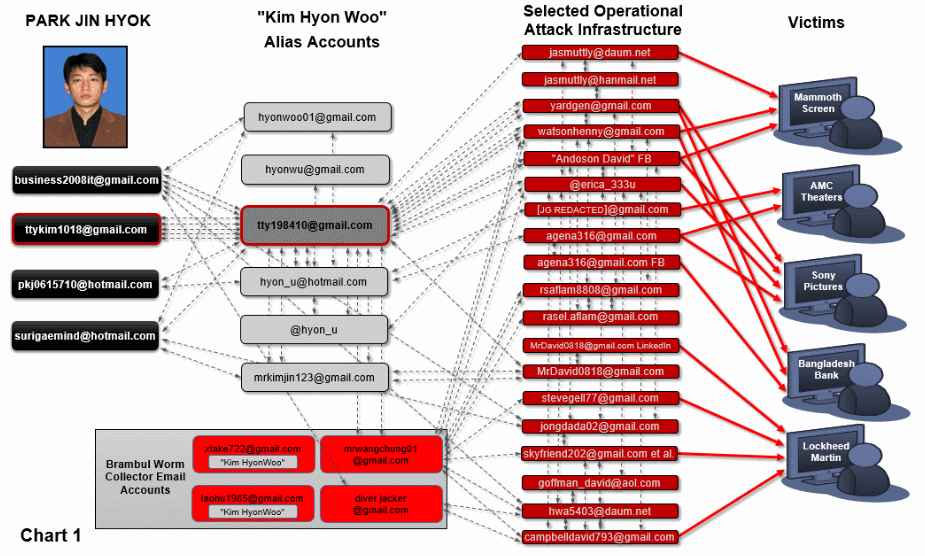
In the DOJ indictment, there is a list of a huge collection of email addresses which were used to register domain names and hosting services linked with all the hacks. There is also a list of IP addresses which were used to access malware commands and control servers, social media accounts. These IP addresses were also linked to the hacked servers and the hosted malware used in the attack.
It is from this list that US authorities have been able to identify Park’s email address and social media account. These were used as he worked at Chosun Expo., as well as during his hacking days at the Lazarus group.
According to the officials, Park had tried to separate his real-world persona with that of his malicious lifestyle. But his real email address, as well as IP address, somehow got linked with the Lazarus Group infrastructure which left a distinct trail for the US authorities to follow.
Park used the alias "Kim Hyon Woo" for all the cyber hacking purposes. Officials are currently of the opinion that it is also used by multiple other operators apart from Park.
Also, considering Park’s background in programming and coding, the officials are also considering the possibility this 34-year-old Korean might even be one of the founders of the Lazarus Group and the WannaCry Ransomware.
What do you think about this Wannacry hacker? Let us know in the comments below. Also, to get instant tech updates, follow TechNadu’s Facebook page, and Twitter handle.