University of Minnesota Banned from Linux Kernel Contributions Due to Annoying Experimentation
- Two students at the University of Minnesota decided to use Linux kernel hackers as lab rats, and it didn’t go well.
- The kernel development team has banned all contributions coming from the university, and the institute launched an investigation.
- This was an interesting yet naive and borderline unethical study that was guaranteed to fail from the start.
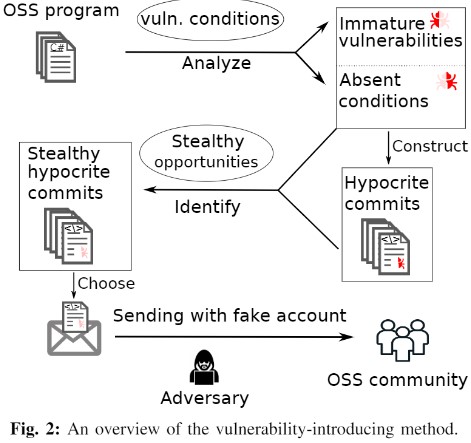
The Linux kernel development team has responded to a large number of bogus “security patches” submitted by two students at the University of Minnesota by barring the entire institute from making any contributions in the future. It seems that the students wanted to run an experiment on whether it would be feasible to stealthily introduce vulnerabilities in open-source software via what they call “hypocrite commits”. These commits weren’t very hypocritical as it seems, as the Linux kernel team found them quite obviously garbage, so the code never reached the main Linux kernel branch.
The source of annoyance, besides having to deal with attempts to introduce bugs onto the Linux kernel, is the way the researchers did this and how the experiment was actually very disruptive to the work of the Kernel hackers. As Greg Kroah-Hartman, who has been a major Linux kernel developer since 2013, explains in his reply to the students, the fact that they pretended to generate these commits with the aid of an automated tool is obviously false. All submissions followed fabricated patterns that were pretty obvious, and they still continued to arrive even after they were called out.
This came to the attention of the University of Minnesota Department of Computer Science & Engineering, who decided to suspend the research immediately and launch an investigation into its method and process. The university-wide ban was not a positive turn of events for anyone, and so the educational institute didn’t take it lightly.
To be fair with the students, their approach was interesting, on paper at least, and their intentions weren’t ill. Attempting to introduce immature vulnerabilities with no apparent activation conditions that deploy concurrency, error paths, aliases, and indirect calls to increase their stealthiness sounds like a plan, but those students obviously had a poor understanding of how things work in the Linux kernel development team. The people who work on the Linux kernel are particularly avid code munchers, and on top of them all sits Linus Torvalds, ready to unleash his wrath if anything weird reaches him.
In the end, the Linux kernel is the most foundational open-source software in the world, used in billions of Android devices, IoTs, personal computers, servers, and more. “Playing” or experimenting with it may be seen as anything between simply unnecessary to outright unethical and dangerous.