UK Tax Service Exposed Thousands Through Careless Bulk SMS Operation
- Mass texting from UK councils to taxpayers who owe them money has exposed their sensitive details.
- A contractor who was responsible for the communications sent out shortlinks that opened an unlocked database.
- The error has been fixed now, but the repercussions of the exposure remain unchanged.
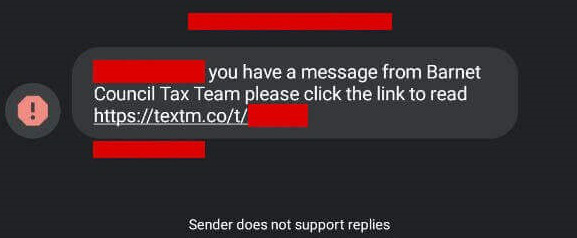
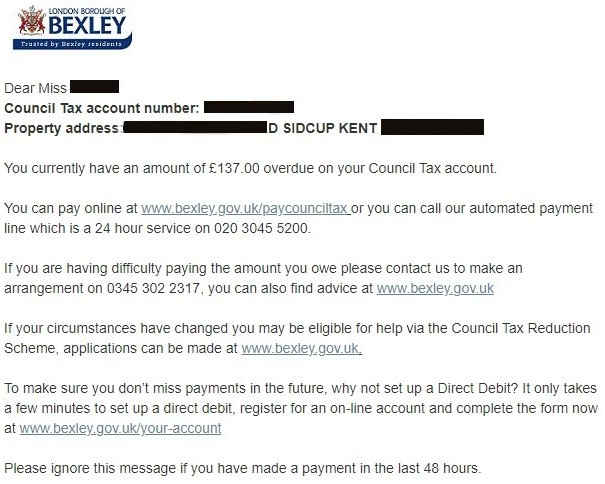
Various local councils in the UK have sent out SMS to thousands of taxpayers to urge them to cover outstanding sums. The messages contained links to online databases that hosted lists of other taxpayers whose data shouldn’t be accessible by anyone else, obviously. Unfortunately, there was no security or any form of authentication to prevent the leak from happening, so thousands of UK taxpayers have had their full names, home addresses, and outstanding debts exposed.
The blunder was the work of Telsolutions Ltd., a company that has provided the contact and communication services to the local councils, which was contracted to urge tax defaulters to pay up. This is a typical tactic that is followed by private and public entities around the globe. Besides the psychological repercussions for the recipients of these messages, we are now also seeing the existence of a risk of data exposure.
Besides SMS, the council tax services also use emails and even recorded voice messages. All of this creates the space for scammers to move in as well, as taxpayers having to deal with official communications with their state through third-parties is the ideal setting for trickery. The official guidelines on how to tell whether a text message or email claiming to come from a council is legitimate are practically pretty weak.
The news of this exposure reached The Register, who checked and confirmed that the data was indeed accessible via the sent shortlinks. From what we were able to confirm at the time of writing this, all of the shared URLs have been taken offline now as both Telsolutions and some of the authorities were informed about the mistake. However, as the UK press site confirms, internet crawlers have already caught some of these public entries, enabling people to search others and see their addresses, tax debts, etc.
In total, it appears that 14 councils have followed the same erroneous method after trusting the particular service provider. That includes Barnet, Bexley, Brighton, Cardiff, Coventry City, Greenwich, Lambeth, Redbridge, Southampton City, and Walsall.
If you are a citizen of one of these states, maybe you should pursue reimbursement for the exposure of your sensitive data and cover your tax debt with the received compensation. As funny as this may sound, state offices and their contractors should learn to be respectful of the personal details of citizens who are already in a vulnerable position.