U2F Keys Have Prevented Phishing Attacks for Over 85,000 Employees at Google
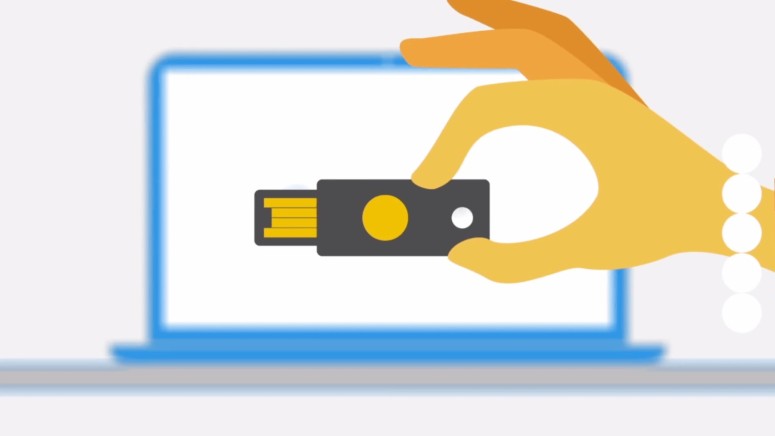
- Google uses a cheap and effective method of preventing phishing attacks by using physical security keys in place of OTP codes or passwords.
- Security keys are available for as little as $20 and serve as an alternative to two-factor authorization for many websites.
- The security keys were implemented in the company last year, with Google employees using one-time codes up until early-2017.
With security breaches becoming more common than ever and even government organizations not being left out, Google has managed to keep its security intact through a very simple solution. Over 85,000 employees at the tech giant make use of cheap USB security keys that use Universal 2nd Factor (U2F) authorization. When using such keys, users do not need to enter any passwords or one-time passwords. Simply inserting the USB device and pressing a button twice is enough for authorization, making logging in simpler than ever.
A Google spokesperson revealed how crucial security keys have become at the organization since their implementation. He stated “We have had no reported or confirmed account takeovers since implementing security keys at Google. Users might be asked to authenticate using their security key for many different apps/reasons. It all depends on the sensitivity of the app and the risk of the user at that point in time.”
Google revealed the organization chose to go ahead with implementing Universal 2nd Factor (U2F) authorization because even in cases of password theft, hackers would need access to the physical USB keys to supplement the one-time codes.
The keys work without requiring any kind of special software, which makes the technology even more reliable. Websites that support security keys do not require passwords after the initial key setup.
Many popular websites like Facebook, Github, Dropbox, KeePass, LastPass and others use the technology and Google expects others to pick up the “WebAuthn” standard soon. “WebAuthn” was introduced as a security standard by the World Wide Web Consortium and the FIDO Alliance. Phishing and man-in-the-middle attacks can be reduced to a minimum if the technology is widely adopted.
Do you use security keys to protect your data? Let us know in the comments below. Get instant updates on TechNadu’s Facebook page, or Twitter handle.