Trickbot Now Capable of Stealing Sensitive Windows Active Directory Data
- Trickbot has proven to be a sneaky breed of malware, gaining new functionality and avoiding detection at a rapid pace.
- It now includes a module affecting Windows’ Active Directory, stealing sensitive information and credentials.
- Considering that Trickbot is designed to actively spread, this can have very serious consequences in the long term.
It’s not unusual for malware breeds to evolve at a rapid pace. A few days ago, we wrote about sLoad 2.0 (Starsload) malware, which jumped a few steps in its evolution in under a month. However, examples like that one are quite often identified by cybersecurity experts. One such malware breed is called Trickbot, and we’ve been following its rapid development during the last few months.
Back in December 2019, there were reports of scammers using Trickbot (among other malware breeds) to infect more than 3,000 systems, 1,800 unique domains, and 400 top-level domains. Then, there were reports indicating that Trickbot can pass through email spam filters, which resulted in malicious actors using this malware in combination with legitimate cloud services. And now, the latest report indicates that Trickbot can target the Active Directory database stored on a compromised Windows domain controller.
The latest evolved functionality of Trickbot affects a file called 'ntds.dll'. This file is automatically created once a server is promoted as a domain controller, which means that the Active Directory database is created during this process as well. By default, the 'ntds.dll' file is saved to C:\Windows\NTDS. The file in question is actually a database that contains plenty of sensitive information related to Active Directory services, including usernames, passwords, groups, computers, and more. Due to its nature, this file is encrypted via a BootKey by default and can be opened only by the domain controller.
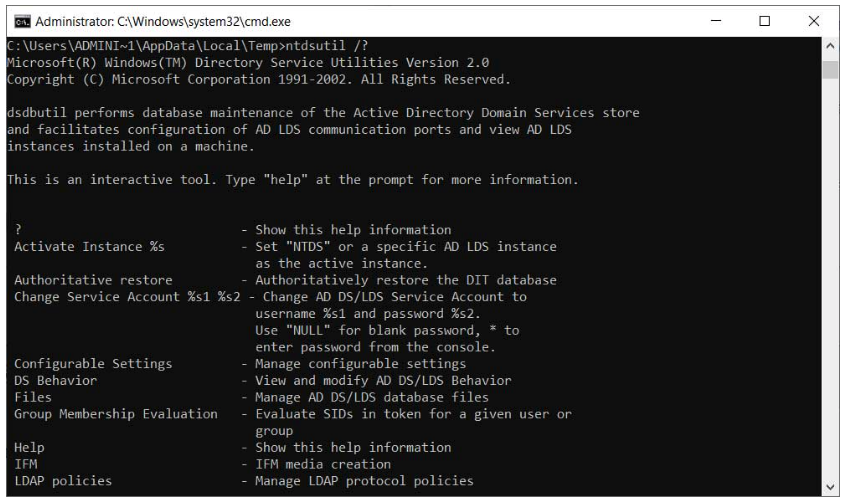
The 'ntdsutil' Command - Image Courtesy of BleepingComputer.
To open and edit the 'ntds.dll' file, the domain controller uses a tool called 'ntdsutil'. One of the possible commands that admins can perform is the ‘ifm’ command, which creates a dump of the Active Directory, which can later be used to automate the process of creating installation media. And this is precisely where Trickbot’s new module comes into play.
As per the information provided by Sandor Nemes, who was first to discover this feature, the Trickbot’s ADll module is capable of creating a temporary copy of the Active Directory database, compress it, and then exfiltrate the files back to the attacker’s servers. By having access to these files, the attacker can decrypt the Active Directory and steal any type of sensitive information stored there.
It’s clear that this Active Directory exploit can have grave consequences, as plenty of sensitive information can be exfiltrated that way. This is still a recently discovered exploit, which might take some time to be fully studied and prevented. In the meantime, one of the recommended resources if Huy Kha’s ‘Attacking Active Directory for Fun and Profit’, which gives a glimpse into various methods of exfiltrating the Active Directory data.