Toyota India (Kirloskar Motor) May Be Hit by Black Nevas Ransomware Attack
- Toyota data breach: Threat actors allege the systems of Toyota India have been compromised, exposing employee and company data.
- The claim: Approximately 4TB of corporate information may have been stolen in the process.
- Other threats: Nevas Ransomware stated its operators gained a foothold on other networks of the corporation as well.
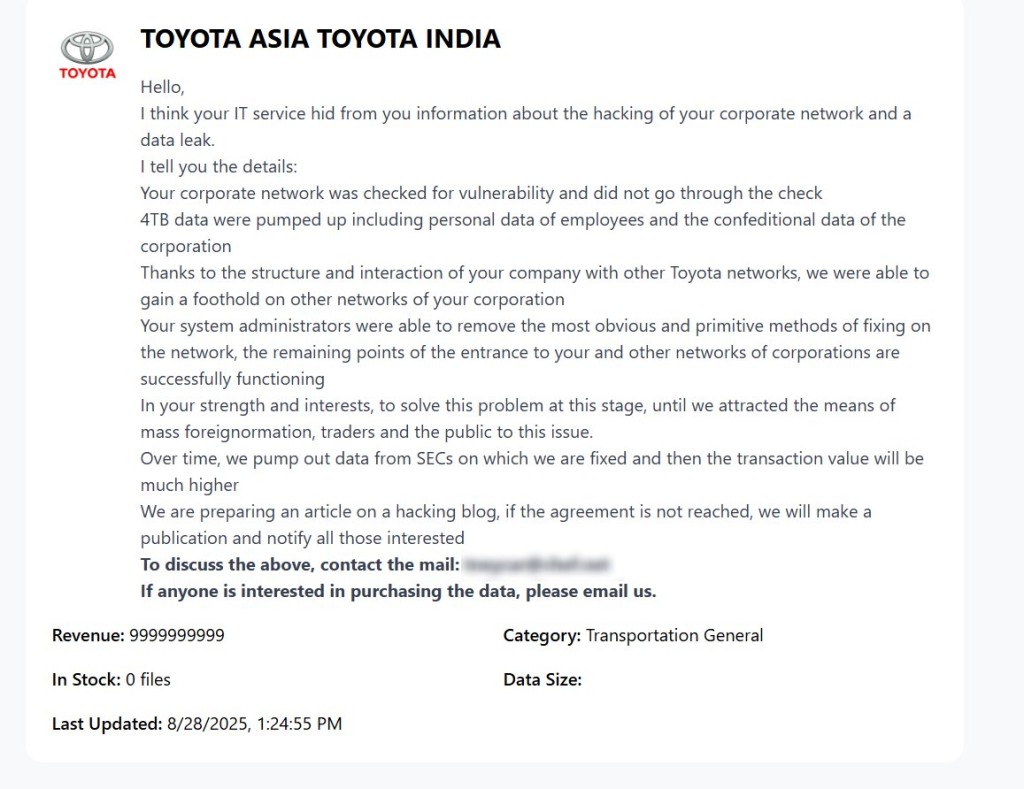
The Black Nevas ransomware gang has claimed responsibility for a cyberattack on Toyota Kirloskar Motor, the Karnataka-based automotive manufacturer. The threat actors claim to have exfiltrated approximately 4TB of sensitive corporate data from the company's systems.
Breach and Data Compromise Claims
The alleged Toyota Kirloskar Motor data breach reportedly involved the exfiltration of data from the manufacturer's internal networks, which included employee personal data and corporate information, according to the ransomware group.
The attackers have reportedly uploaded sample files as proof of their successful infiltration, a common tactic employed by ransomware operators to demonstrate the legitimacy of their claims and pressure victims into compliance.
Black Nevas said it gained a foothold on other networks of the corporation of Toyota India with other Toyota networks. Their statement also claims that while system administrators removed some easier-to-detect compromises, other threat points of entry to this and other company networks remain functional.
Toyota Kirloskar Motor's digital infrastructure may offer access to multiple data categories, including proprietary manufacturing processes, supplier information, employee records, and potentially customer data, though specific content categories have not been named.
Implications for Automotive Cybersecurity
Toyota Kirloskar Motor, established as a joint venture between Toyota Motor Corporation and the Kirloskar Group, represents a significant presence in India's automotive market.
The Black Nevas group's targeting of automotive infrastructure reflects broader industry vulnerabilities that require immediate attention from security professionals and organizational leadership.
Strategic Response Requirements
Organizations within the automotive manufacturing sector must implement comprehensive cybersecurity frameworks that address both operational technology (OT) and information technology (IT) environments.
The Toyota data breach underscores the necessity for robust backup systems, network segmentation, and incident response protocols specifically tailored to manufacturing environments.
The automotive sector's complex supply chain networks and proprietary intellectual property make these companies particularly attractive targets for sophisticated threat actors.
In August, the Qilin Ransomware leak site claimed that a branch of the Nissan design network had been breached, and an unnamed carmaker’s web portal exposed a remote car unlocking vulnerability. Also, flaws in Volkswagen’s Connected Car app allowed brute force attacks and exposed owner details in May.