“ThunderSpy” Is Threatening to Steal Your Data Right From the Laptop Port
- A new Thunderbolt attack can exfiltrate data from laptops without going through authentication.
- The attack is based on seven vulnerabilities that Intel isn’t planning to fix, as they are addressed by existing risk mitigation technology.
- Not many devices support Kernel DMA Protection right now, so physical protection is the best approach.
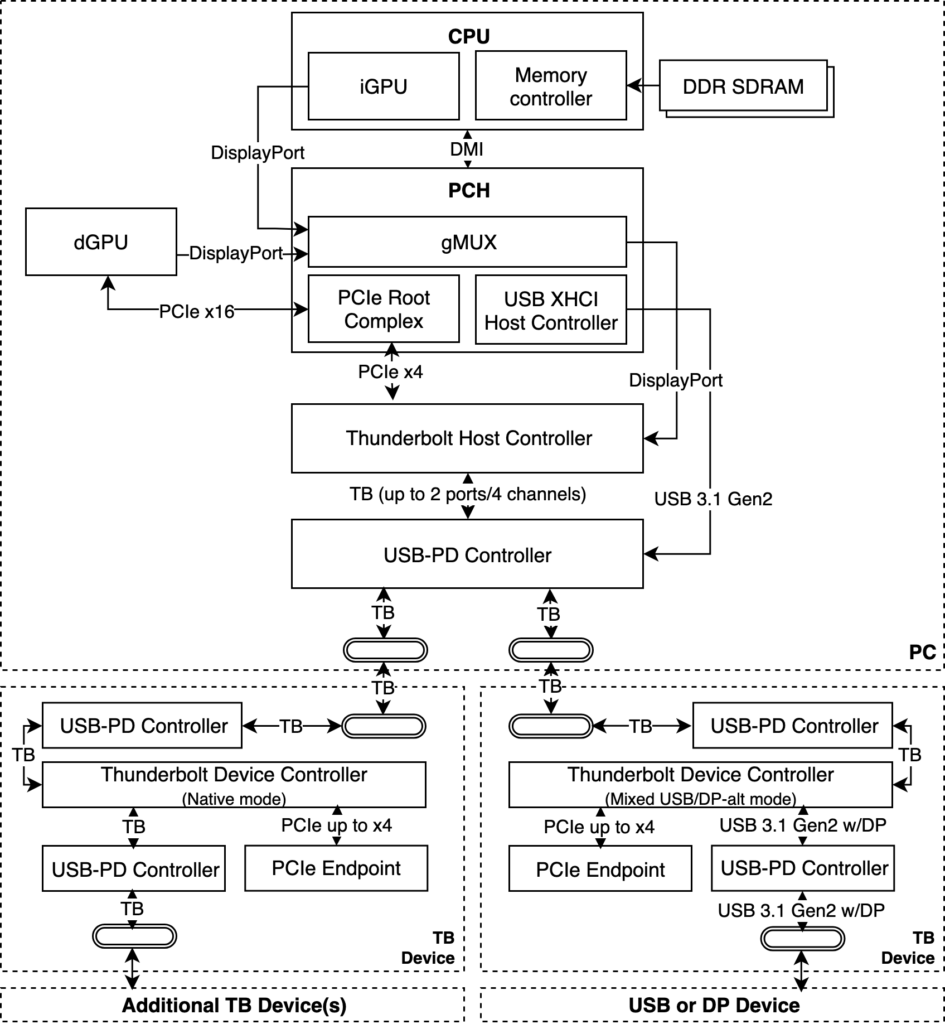
A team of researchers from the Eindhoven University of Technology in the Netherlands has presented a new method of attack against Thunderbolt ports. The attack is called “ThunderSpy” and can potentially enable a hacker who has physical access to the target device to exfiltrate all data from the device, even if the computer is locked, in sleep mode, or the drive is encrypted. After the attack, the victim would have no way to tell that anything critical has happened, as there is no recording of an incident to be reported to the system administrator.
In the following video, the researchers are demonstrating how they were able to bypass the Windows lock screen on a recent model laptop using Thunderbolt 3. To achieve this, the hacker needs to create arbitrary Thunderbolt device identities that are cloning already user-authorized devices. This process is completely ignored by pre-boot protection and Security Levels, so the user can patch the firmware without providing an OS or BIOS password, and eventually disable all Thunderbolt security. In addition to this, the team developed a tool that would configure the SPI flash to “read-only” mode, essentially making the application of any future firmware updates impossible.
The attack is based on the exploitation of a total of seven vulnerabilities, described as follows:
- Inadequate firmware verification schemes
- Weak device authentication scheme
- Use of unauthenticated device metadata
- Downgrade attack using backward compatibility
- Use of unauthenticated controller configurations
- SPI flash interface deficiencies
- No Thunderbolt security on Boot Camp
Source: thunderspy.io
The above information was shared with Intel - who is the creator of the Thunderbolt connectivity standard - on February 10, 2020. Intel confirmed the flaws within a month, while OEMs and ODMs like Apple and the Linux kernel security team were informed of the problem in the weeks that followed.
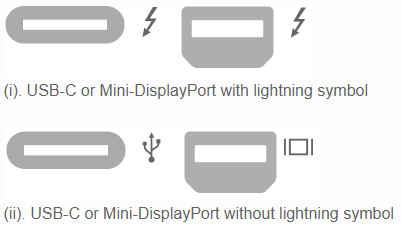
Understandably, there is no fix available yet, so the only way to tell if your device is vulnerable to ThunderSpy is by checking yourself. First, you may use the “Spycheck” tool (Windows, Linux) that was specifically created for this purpose. Secondly, you can visually inspect the ports on your laptop. If the ports look like the (i.) set, you’re vulnerable. If they look like these pictured in (.ii), you are safe against ThunderSpy. USB-C ports that don’t support Thunderbolt aren’t affected by this attack.
Source: thunderspy.io
All Macs released from 2011 onward are vulnerable, and so are all systems that don’t feature Kernel DMA Protection. It is also important to clarify that ThunderSpy affects all three versions of Thunderbolt. Still, systems that began shipping since 2019 have more chances of being safe, due to the presence of Kernel DMA Protection. And this is exactly why Intel is not planning to fix the flaws or provide any mitigations, since the most recent technology ships with the required protection measures anyway.