The Coruna iPhone Exploit Kit Used by Cybercriminals, Possibly a Leaked Government Hacking Tool
- Exploit Proliferation: A sophisticated suite of hacking tools designed to compromise iPhones has been leaked and is now actively used by cybercriminals.
- Broad Impact: The toolkit, known as Coruna, leverages 23 vulnerabilities and can compromise iPhone models running iOS versions up to 17.2.1.
- Threat Actor Usage: The exploits were deployed by a Russian espionage group and a financially motivated hacker in China.
An iPhone exploit kit, dubbed Coruna, is used by multiple, unrelated threat actors, including those based in Russia and China. Coruna contained 5 full iOS exploit chains and a total of 23 exploits, according to security researchers at Google.
Mobile security firm iVerify, which reverse-engineered the tools, noted similarities to hacking frameworks previously attributed to the U.S. government in state-sponsored surveillance operations.
Coruna iPhone Exploit Kit Capabilities
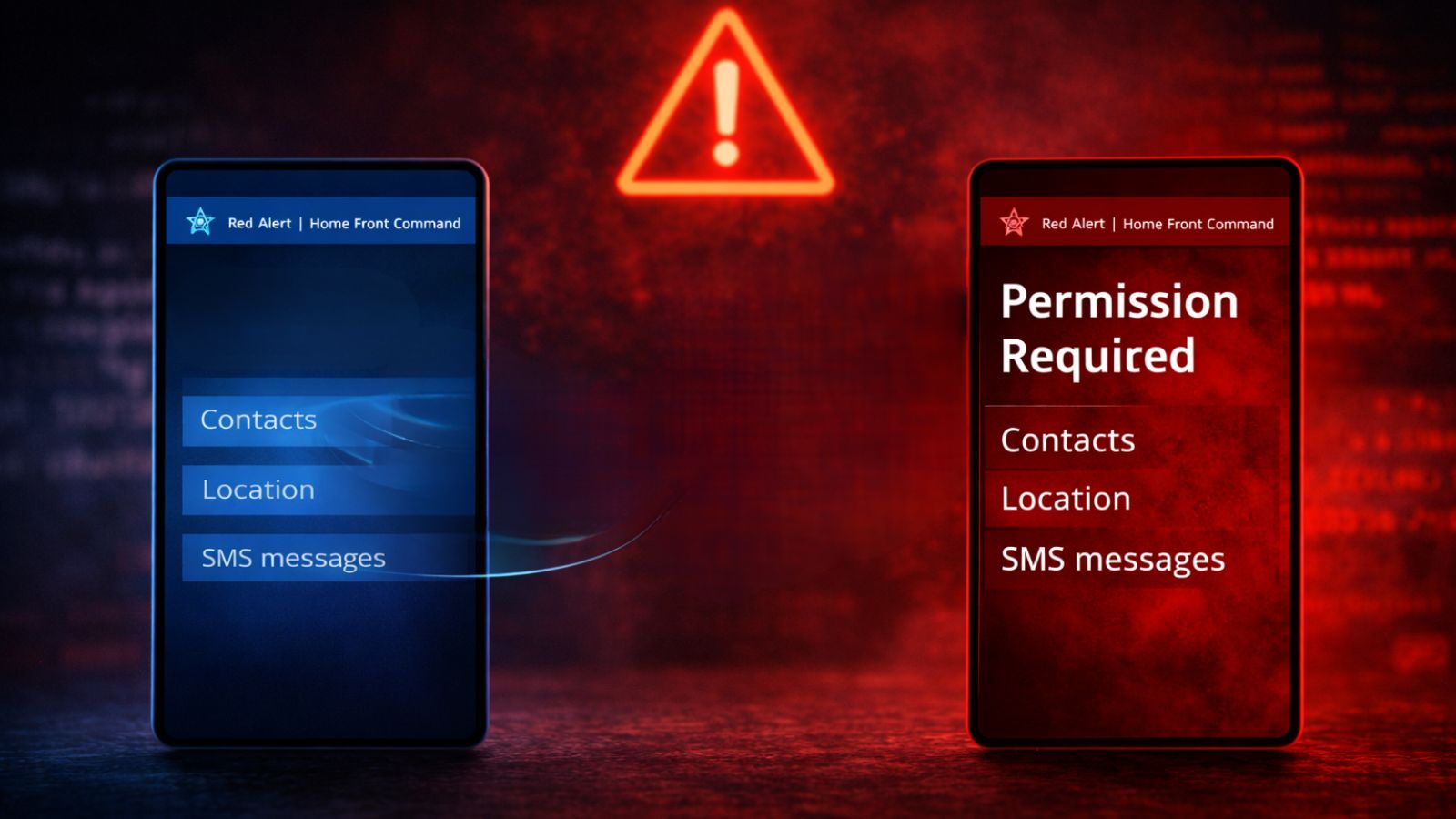
The Coruna hacking toolkit is exceptionally powerful, capable of compromising a target iPhone simply by having the user visit a malicious website, a technique known as a "watering hole" attack. The toolkit's effectiveness spans a wide range of devices, affecting iPhones running iOS 13 through December 2023-released iOS 17.2.1.
The attacks targeted Ukrainian users were orchestrated by UNC6353, a suspected Russian cyberespionage group, according to Google Threat Intelligence Group (GTIG), and the exploit kit was later used in broad-scale campaigns by China-linked UNC6691. Beyond these identified exploits, multiple threat actors have now acquired advanced exploitation techniques that can be reused and modified with newly identified vulnerabilities.
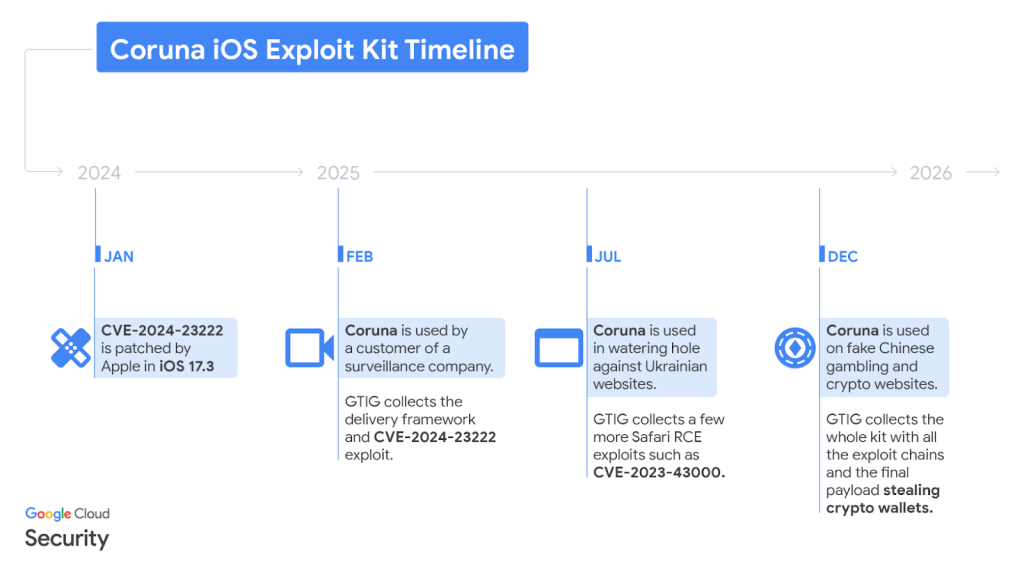
GTIG said this toolkit was first detected in February 2025 as part of an iOS exploit chain used by “a customer of a surveillance company,” with reports adding the discovery occurred during an attempt by a commercial spyware vendor to hack a target on behalf of a government client. Google and iVerify noted that Coruna contains components previously used in a hacking operation targeting Kaspersky in 2023.
The "Secondhand" Exploit Market
While GTIG said the proliferation path is unclear, it suggests an active market for "second-hand" zero-day exploits, where cybercriminals using exploits developed for national intelligence gain access to them, either through leaks or illicit sales.
This creates a new market where powerful cyber weapons are repurposed for financial crime or broader espionage, far beyond their intended use. The proliferation of tools like Coruna underscores the inherent danger of creating and stockpiling digital vulnerabilities.
A February Google report revealed that state-backed hackers leverage Gemini AI for cyberespionage.