Stryker Cyberattack Wipes Employee Devices, Handala Claims Closing Almost 80 Offices Belonging to the US Medical Giant
- Operational disruption: Medical device manufacturer Stryker experienced a significant global network disruption, resulting in wiped corporate devices and locked systems.
- Handala attribution: The pro-Iran Handala hacking group claimed responsibility for the incident, citing retaliation for recent geopolitical conflicts in the Middle East.
- Allegations: Attackers reportedly erased over 200,000 internal systems and exfiltrated 50 terabytes of proprietary data.
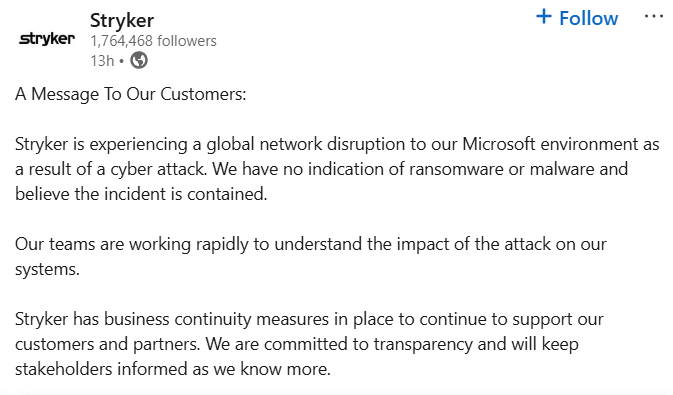
A recent Stryker cyberattack was confirmed by the medical device giant, which said a severe network disruption affected its Microsoft environment, heavily restricting operational capacity and business continuity. The Handala hacking group, a threat actor historically linked to Iranian geopolitical interests, claimed direct responsibility for the network compromise and allegedly exfiltrated 50 TB of data.
Details of the Stryker Breach
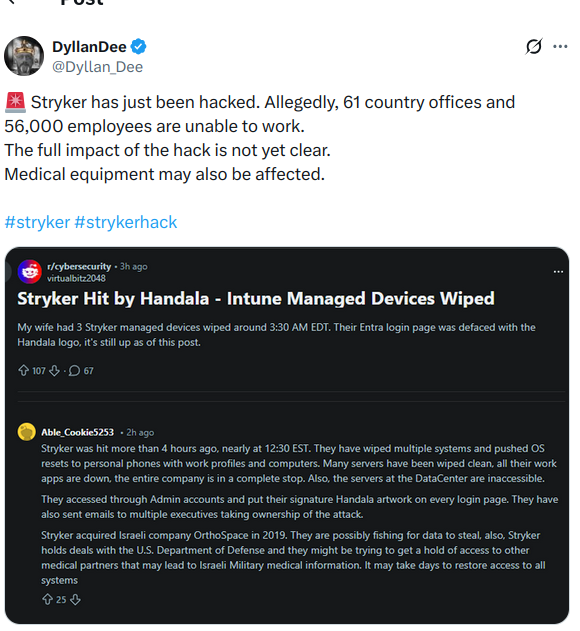
Initial reports indicate this cybersecurity breach systematically dismantled employee access to its corporate Microsoft environments. Workers who discovered their company-issued computers and mobile devices, including iPhones, had been entirely wiped mentioned Intune, a cloud-based unified endpoint management (UEM) solution.
Although Stryker publicly stated they found no immediate evidence of conventional ransomware, the scale of the system disruption paralyzed internal communications and daily operations across multiple international facilities, and automated administrative phone systems declared a building emergency on Wednesday.
Roughly 5,500 employees were locked out simultaneously across Ireland, the U.S., Australia, and India, and manufacturing systems for orthopedic implants went offline, according to David Lindner, CISO of Contrast Security, who called it “a coordinated act of sabotage.”
As some users reported allegedly being instructed to remove Intune, the company portal, Teams, and the VPN from their devices, Stryker continues to investigate the intrusion mechanisms to safely restore full functionality.
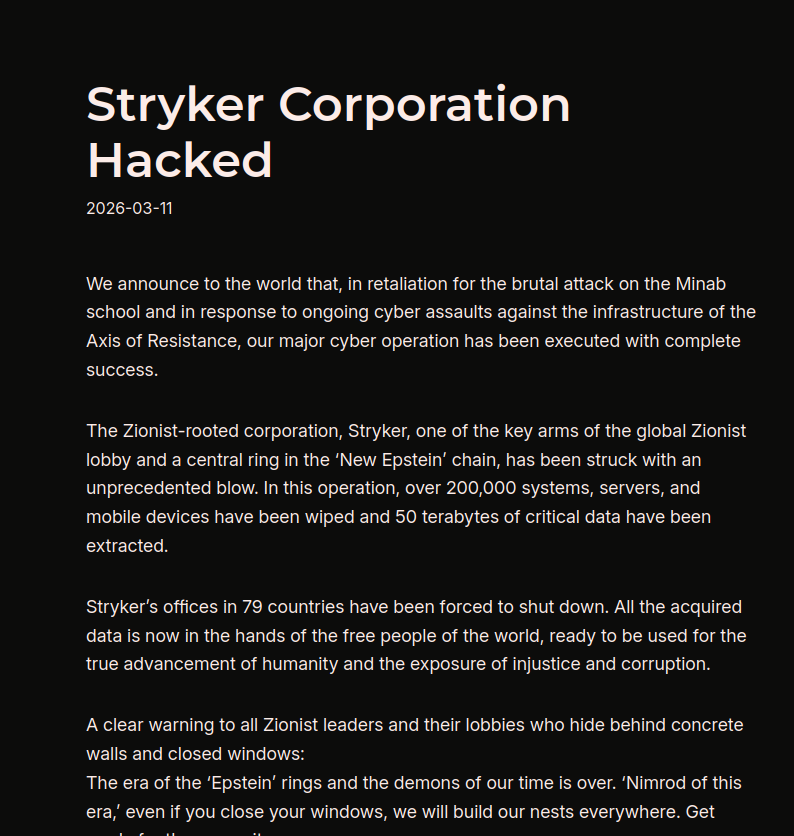
Handala Hacking Group Connection
The Handala hacking group allegedly deployed wiper malware, defacing standard corporate login screens (users reported Entra login pages) with its logo. The group claimed to have erased over 200,000 internal systems and exfiltrated 50 terabytes of proprietary data.
They explicitly framed the digital intrusion as retaliation for recent U.S. and Israeli military actions, illustrating how hostile actors execute destructive digital campaigns to achieve broader political objectives.
Implications for Device Cybersecurity
As a major international supplier holding substantial defense contracts, Stryker's operational downtime risks cascading effects throughout global healthcare supply chains. Hardening corporate networks against highly motivated nation-state adversaries remains a paramount priority for maintaining uninterrupted critical infrastructure operations.
The Stryker attack should be a wake-up call for every CISO in critical manufacturing, said Lindner. He underlines that the hackers didn't encrypt files or ask for Bitcoin but wiped them, a “distinction that matters enormously” since wiper malware is a weapon, not a business model.
The same day, Handala also defaced the Academy of the Hebrew Language's website, and Iran's IRGC formally declared U.S. and Israeli economic interests as targets, naming Google, Microsoft, Palantir, IBM, Nvidia, and Oracle, and Stryker also fits that targeting profile, considering its deep US ties and operations in Israel-adjacent markets, Lindner added.
Last week, MuddyWater targeted the U.S., Canada, and Israeli networks nd critical infrastructure, and 12 hacktivist groups, including Handala, targeted 110 organizations in over 15 countries with 150 DDoS attacks.