‘Squid Game’ Lures Used by Actors to Distribute Dridex Malware
- A Squid Game theme is the latest lure used by threat actors' email campaigns to get victims to click.
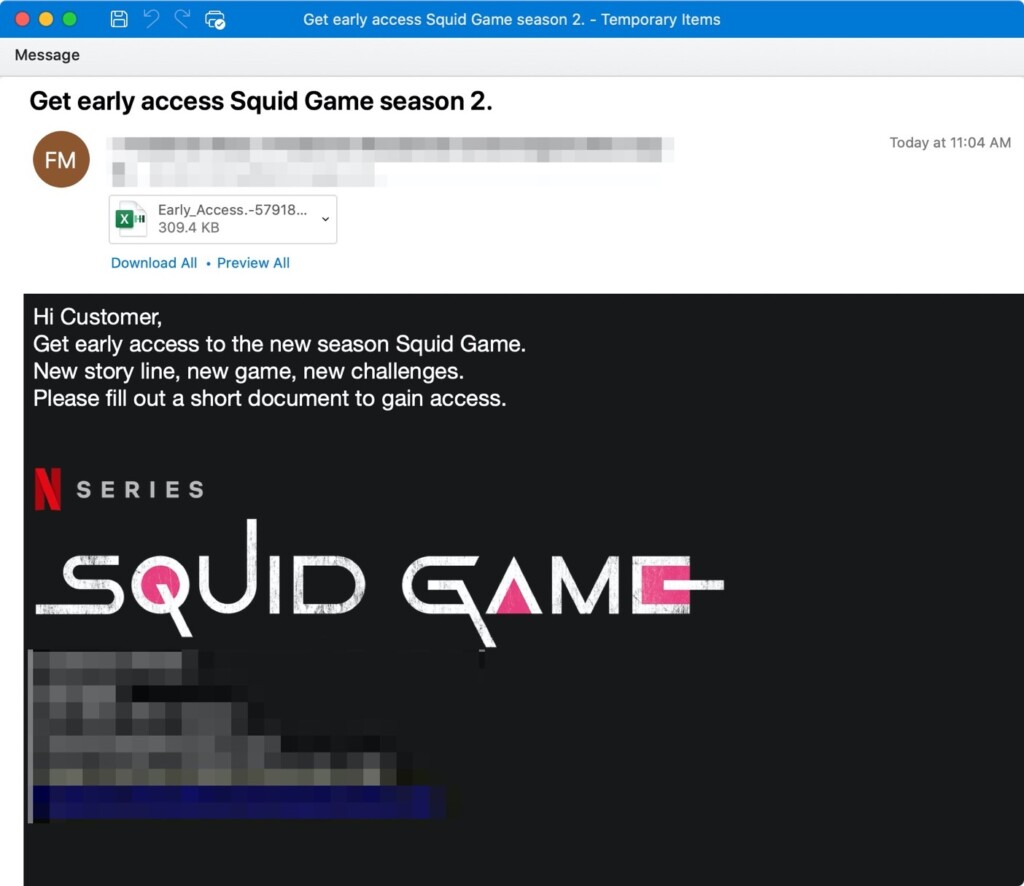
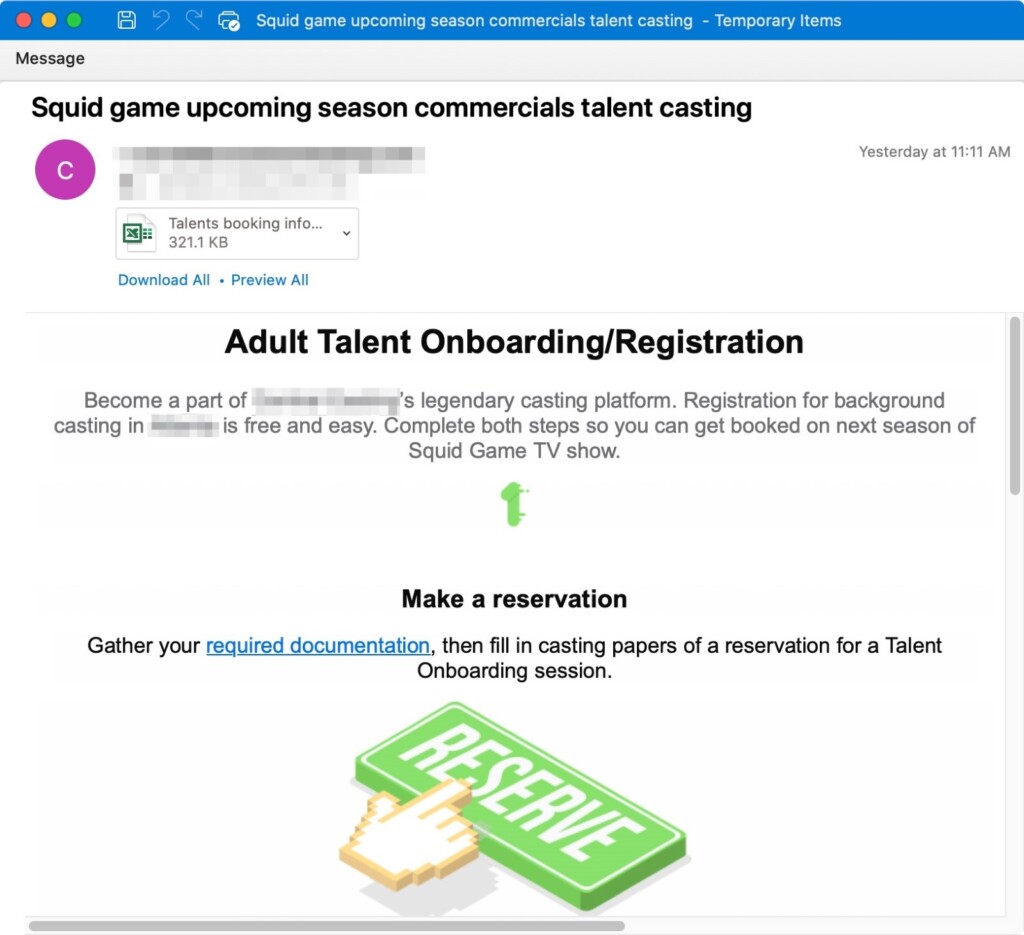
- The TA575 actor sends emails that appear to come from Netflix, urging recipients to open an attached document and fill some information in it.
- It uses the Dridex malware, which combines many malware for multi-level system compromise.
A large-scale threat actor called TA575, which has been on researchers’ radar since late 2020, is moving across major US industries via Squid Game-themed emails containing laced attachments. These emails pose as coming from Netflix and pretend to offer early access to the show's latest season or a role in the show, either one asking the victim to open an attached document to fill in some information.
The attachments are usually in compromised Excel docs format and contain malicious code execution macros. Once they are opened, if the user enables macros, the Dridex banking trojan affiliate id “22203” is downloaded from Discord URLs. The successful Dridex banking trojan is disseminated by several affiliates and can result in data theft and the installation of additional malware such as ransomware.
TA575 is a Dridex affiliate that distributes malware via malicious URLs, Microsoft Office attachments, and password-protected files, sending thousands of emails per campaign. The Discord content delivery network (CDN) is prone to hosting trojans due to a pretty lax system. According to Microsoft’s detection and further research, Discord has 27 unique malware families basically divided into four types, and Dridex is among them.
This group generally uses themes including invoicing and payments, but occasionally includes current news, popular events, and cultural references, and since Squid Game is the latest frenzy, they couldn't miss their chance. Netflix users are advised caution in opening emails that propose unique things that seem unlikely to be true, especially since threat actors love to mimic this particular streaming platform. Of course, not opening any attachments goes without saying.