A Sprint Contractor Has Exposed 261,300 US Cell Phone Bills via an Unprotected Database
- A marketing company called “Deardorff Communications” has exposed personal data of thousands of cell phone users.
- The data that was left unprotected online includes names, addresses, numbers, and even PINs.
- The involved parties are trying to downplay the incident, saying that the problem has been resolved.
One of the contractors of Sprint has exposed 261,300 cell phone bills after they have left a cloud server unprotected online. The documents contained on the accessible AWS server concern subscribers of AT&T, T-Mobile, and Verizon, while the date of the bills goes as far back as 2015. The discovery of the unprotected server was the work of Fidus Information Security, a British penetration testing expert who had to do some digging in order to find out the owner. At first, they reported the discovery to Amazon, who shut down the bucket and then went on to find who is behind it.
After looking into the files, they have located the name of an executive working at Deardorff Communications, a collaborator of Sprint. Upon contacting the marketing firm, they confirmed that the bucket was theirs, but they didn't clarify the period of time for which it remained accessible by anyone. They were limited to saying that they launched an internal investigation to determine the root cause of this incident, and took the appropriate measures to prevent a similar occurrence in the future. The response of the telecom providers whose customers were exposed was silence, except for Verizon who stated that they are still looking into the matter. As for Sprint itself, they assured the public that the error has been corrected. However, this means nothing for the people who have already had their data leaked.
Source: TechCrunch
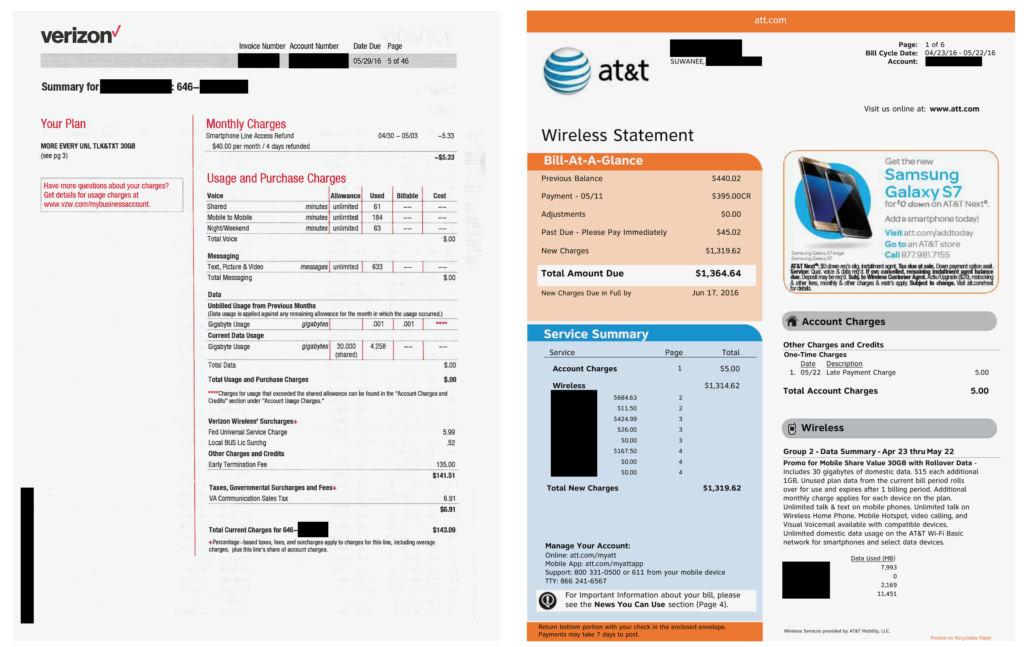
As for what information has been exposed, we all know what cell phone bills contain. Subscriber names, physical addresses, phone numbers, call histories, etc. These are very useful for phishing actors and scammers, but unfortunately, it’s not the whole story. The researchers have also located additional documents such as bank statements, usernames of the subscribers on the companies’ online portals, their passwords, and even their account PINs.
Right now, nobody has received a notification about the exposure from Deardorff Communications, so the cell phone subscribers who have been compromised do not know anything about it. Hopefully, someone in the chain, even the telecom providers who weren’t responsible for this leak, will send warnings to their clients. This is another example that shows the dangers of data mishandling by collaborators and contractors, and it is also noteworthy that the responsible entity was only marginally exposed after the researchers looked deeper into the details of the contents. This could very easily be another case of the responsible entity remaining unknown.
Will you be calling your telecom provider to ask about whether you were exposed by this incident? Let us know in the comments below, or on our socials, on Facebook and Twitter.