A Small Set of Android Apps Exposed the Data of Over 100 Million Users
- A few apps have collectively exposed millions of sensitive user data due to cloud service misconfigurations.
- Oftentimes, the embedded keys to access cloud services are poorly encrypted and retrievable.
- The users of these apps would have no way to know about the exposure, so using fake PII is advisable.
App developers love the convenience of cloud services when it comes to storing massive amounts of user data, but what they don’t have an equally strong affinity towards is securing this data properly. As Checkpoint details in a report that came out today, many Android app developers just fail to configure their real-time databases properly, so whatever user data is logged onto them through the apps is left exposed to those who know how to search for it. As the researchers point out, failing to set up an authentication step is actually a lot more common than what we may think.
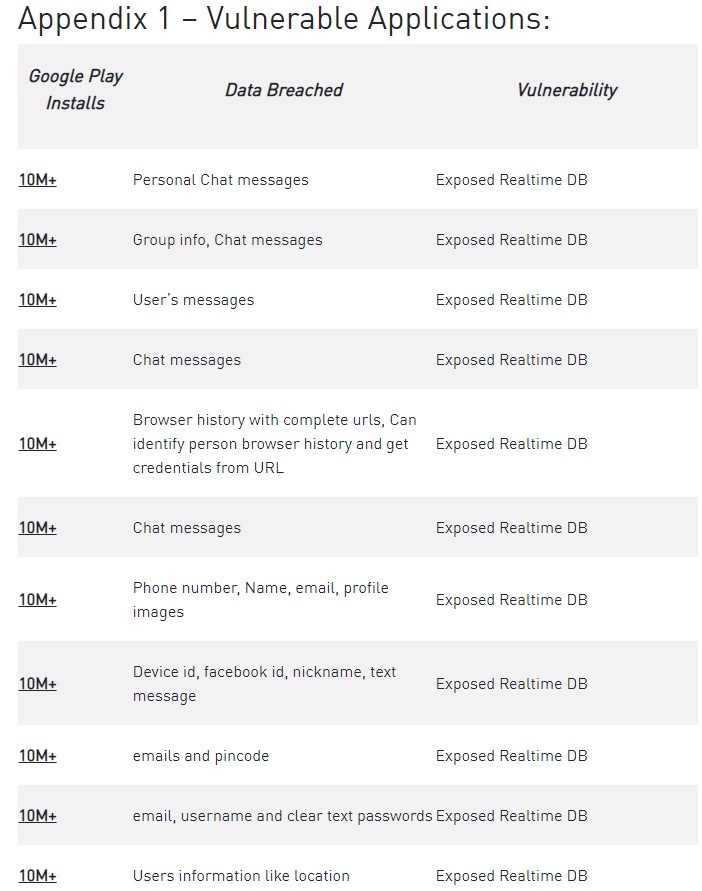
Unfortunately, the list of apps given by Checkpoint includes some top-rated apps that enjoy more than 10 million downloads each. Three examples given include “Logo Maker,” “Astro Guru,” and “T’Leva,” “Screen Recorder,” and “iFax.” As for what type of data was exposed, the list includes the following:
- Names
- Phone numbers
- Email addresses
- Recordings
- Image uploads
- Backups
- User photos
- Logs
- Private chat
- Coarse or fine location
- Device ID
- Facebook ID
- Pincode
- Browser history
Obviously, and depending on the app type, different data types are exposed, but what remains the same is the fact that in most cases, the users themselves are unaware of the exposure. That said, a solid piece of advice to stay safe from this possibility would be to use fake personas when using mobile apps - if possible, of course.
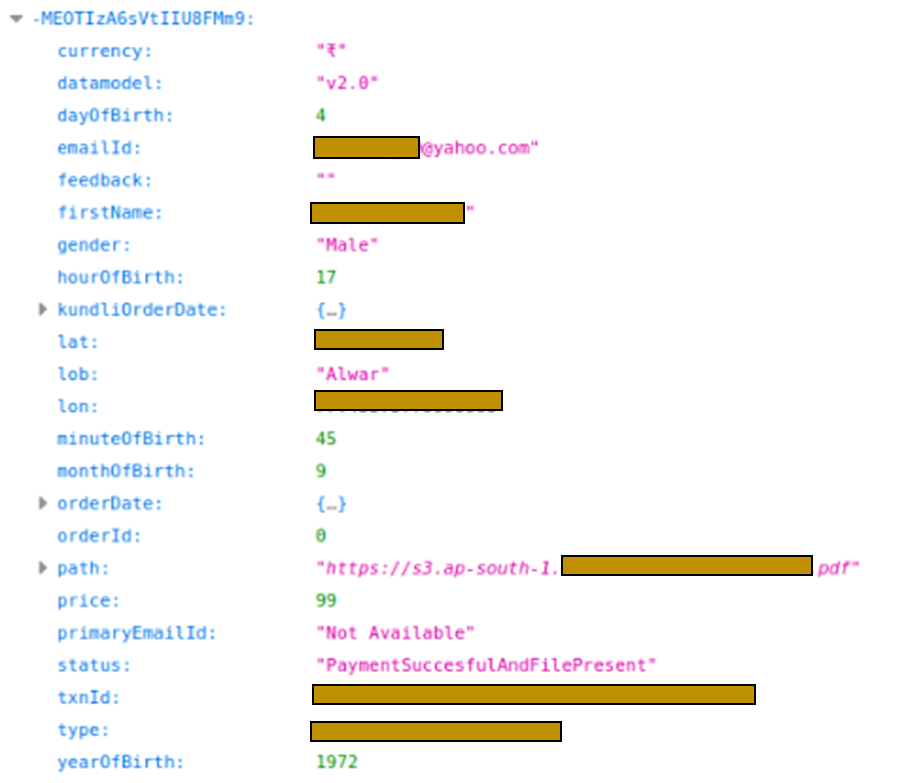
In the Astro Guru example that people use to get regular horoscope predictions for what it’s worth, the exposed set includes names, dates of birth, gender, location, email address, and even payment details. Would a horoscope prediction be worth the trouble of having to deal with the consequences of targeted phishing?
Checkpoint also noticed the problem of poor cloud services key encryption in some applications that have them embedded. Besides the fact that Base64 is reversible, it is oftentimes possible to derive the key value by looking at the code and decode the function. This is again a problem on the developer side, and it is one that users would have no way to realize.
A year ago, we tapped into a similar problem with Android apps that leaked out sensitive user data due to malpractices relevant to the deployment of Google Firebase. The numbers were a lot more dizzying back then, but the conclusion is the same - Android app developers need to step up their game in data privacy and security.