Slack Resets the Passwords of About 1% of Its Userbase
- Slack tries to plug a hole that was opened in the past, resetting passwords of vulnerable users.
- The platform sustained a breach in 2015 and just found out that the user data is roaming out there.
- Only old accounts that are still using the same pass are affected by the forced password reset.
Back in 2015, Slack fell victim of an attack that resulted in the compromise of a database that contained user profile information. The popular communications platform launched two-factor authentication immediately to prevent unauthorized user logins and account takeovers, offered a “password kill switch” for team owners, and urged everyone to reset their passwords anyway. Those who still haven’t will now be forced to do it, as Slack has imposed a password reset for them. This concerns only a small part of the Slack’s userbase (1%), as it affects only accounts that were created before the March 2015 breach, and owners who haven’t changed their password since.
While Slack did not find any evidence that the 2015 breach had resulted in actual risk, a report that they received recently changed that. A bug bounty program contacted Slack and presented them with a set of email addresses and password combinations that the platform confirmed to be valid. Upon a more in-depth inspection, Slack discovered that most of them were taken during the 2015 incident, so the data was out there and for sale after all, and the only way to ensure the safety of the compromised users would be to reset their passwords.
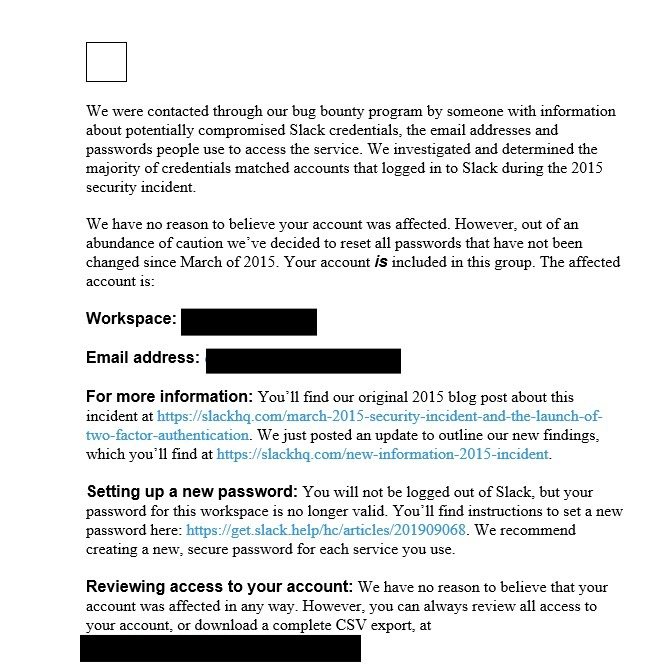
That said, if you belong in the vulnerable category, there’s nothing that you need to do right now as Slack will reset your password automatically. Moreover, you will receive an email that looks like the one below, and that contains instructions on the further steps that you need to take in order to reset your password and secure your account from future threats. Besides setting up a new password and reviewing the account activity, the most essential extra step that you should take from now on is the 2FA, and this applies to all users, no matter if they belong to the vulnerable 1% or the unaffected 99%.
image source: threatpost.com
Remember, in April, Slack announced a rich set of potent dangers to its investors, reminding them that the stock performance of the company could be easily affected by a cyber-attack. As it seems, Slack can’t rule out such a possibility, fearing nation-state hacker groups that deploy advanced password spraying, phishing, credential stuffing, and DDoS attacks. In most cases, it all starts with the user and what measures of protection are taken from the account owner in the first place.
Do you trust Slack for your communications, or do you prefer another tool? Let us know in the comments down below, or on our socials, on Facebook and Twitter.