Signal Silently Patched Severe Privacy Flaw Hoping Nobody Would Notice
- Signal wasn’t generating alerts when “safety numbers” on chat rooms are changed in the past couple of months.
- The IM platform rejected the report that came from researchers, saying they’re unable to reproduce the issue.
- Signal pushed the fixing patches silently the next week, even though it never accepted the existence of a flaw.
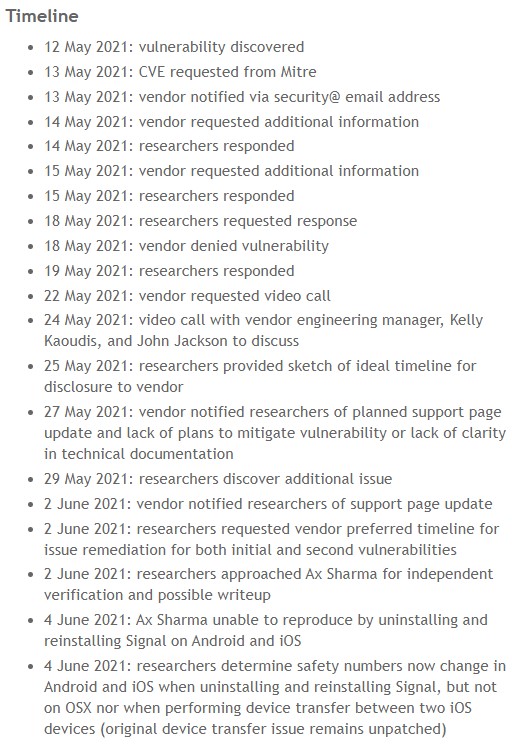
Signal has patched a serious privacy issue on implementing its “safety number” system. Still, it hasn’t made it public even if it was reported to its development team with full technical details by security researchers. More specifically, Kelly Kaoudis, ‘Sick Codes,’ Robert Willis, and John Jackson of the ‘Sakura Samurai’ team have found that when a Signal one-to-one chat participant switches to a new device or reinstalls the app, the relevant notification to the other participant isn’t delivered.
Signal generates a unique “safety number” on each one-to-one chat as a unique identifier that helps verify the other person is indeed the one on your contact list. If that person changes device, reinstalls the Signal app, or switches to another platform, Signal should send a warning to the other party to inform them that the safety number has changed. If that doesn’t happen, someone could impersonate the sender and trick the recipient into thinking they are still communicating with a trusty contact.
This is a serious privacy flaw which the Sakura Samurai team reported to Signal responsibly, offered all of the requested additional information that would help the developers reproduce the problem, and even discussed this over video calls. Unfortunately, the response they got from the IM platform was that they don’t plan to mitigate the vulnerability or to address the lack of clarity on how exactly the “safety number” system works on the project’s documentation. In fact, Signal’s team answered by saying they were unable to reproduce the issue, so for them, there was no flaw to discuss.
Only a week after that, and while the researchers asked for the help of journalist Ax Sharma to verify the existence of the problem, it was discovered that Signal had actually pushed patches to fix the vulnerability, albeit silently. The issue was no longer there on Android or iOS, but it remains on macOS, where a safety number change alert is still not generated. Furthermore, by looking at the version history and the release notes, there’s no mention of fixing such a severe privacy flaw, not even a vague one.
This is overly unethical for a project that likes to promote itself as a privacy-respecting and security-first messenger platform, and there are no excuses for not disclosing the flaw to the public. Even if the Signal team re-evaluated Sakura’s report at a later time, they ought to have acknowledged the researchers for their contribution and act with transparency towards their community of users when they decided to address the problem.
If you are using Signal, note that between mid-April and the most recent update that came earlier this week, you may have been talking to someone who poses as a trusty contact but isn't.