Signal Received Grand Jury Subpoena to Hand Over User Data
- A Californian grand jury wants Signal to hand over the details of a user involved in a criminal investigation.
- The IM platform responded by saying they have nothing to share except for account connection timestamps.
- The submitted subpoena requests third-party and data-routing details for reasons unclear.
Signal has received a subpoena coming from the United States Attorney’s Office in the Central District of California, asking the end-to-end encrypted IM platform to hand over user data that was determined to be relevant to an ongoing criminal investigation conducted by Homeland Security Investigations.
The subpoena requires that a custodian of records from Signal appears before the grand jury and produces the following:
- User name, address, and date and time of the account creation.
- Date and time of Signal app download as well as all app access records.
- Identification of all possible third parties that are involved in the activation of Signal accounts.
- All user correspondence associated with the given phone number.
In addition to the above, the subpoena requests the Signal team to clarify what information travels outside the State of California when a user based there creates an account or when two users based there communicate. This sounds like a weird question to ask, but it’s probably relevant to jurisdiction - and possibly also requested as a way to point the legal pressure elsewhere.
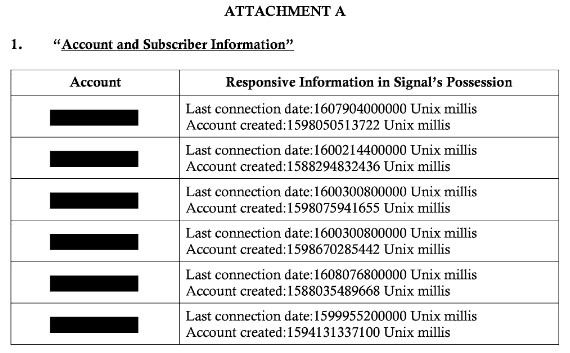
Signal's response to this was that the platform simply doesn’t maintain anything other than UNIX timestamps for when an account was created and when the last connection happened. The platform denied having any access to user messages, lists, groups, contacts, profile names, or avatars, so they were unable to share anything like that with the law enforcement authorities.
Additionally, the service responded to the technical aspect of the subpoena’s questions, saying that its cloud servers are located in Virginia, so some data indeed flies away from California if two Signal users based there communicate. For the most part, though, the data is transmitted peer-to-peer or relayed through a third-party server located closest to the user’s location, so the call data won’t travel through a server that is outside the state.
All in all, Signal has taken this opportunity to remind everyone of the fact that the service is not logging any user data and isn’t spying on people’s communications. However, the fact that the authorities insist on asking for user information is a worrying sign, and some experts in the field maintain that Signal cannot continue denying cooperation for long.
If we were to comment on something, it would be that this is another example of why asking for a phone number is a bad idea and a bad choice from Signal’s side. A person’s phone number is often linked with their identity, so in this case, a person was identified as a Signal user. You can never have true privacy this way, and while we understand the need for a way to verify people, this approach is just plainly de-anonymizing them.