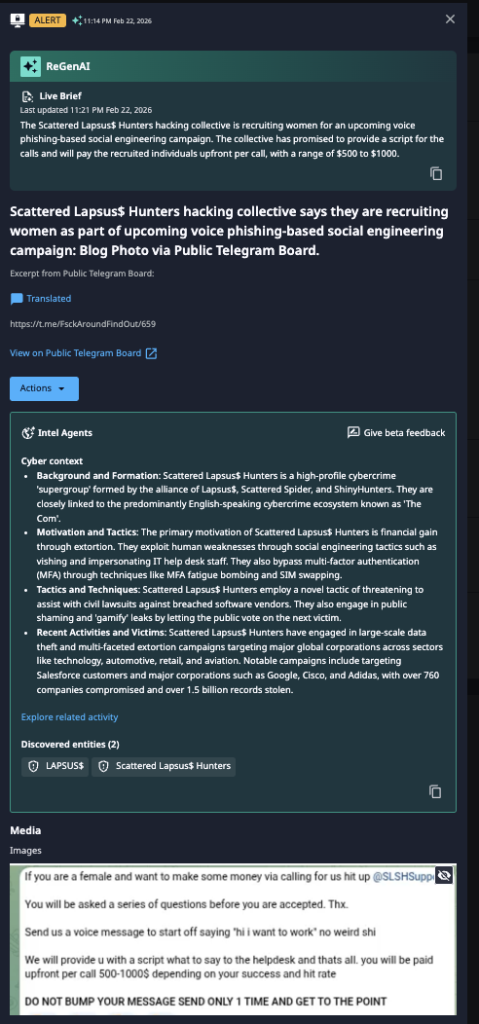
Scattered Lapsus$ Hunters Offers $1,000 to Women Recruited for Vishing Campaigns
- Tactical Shift: The Scattered Lapsus$ Hunters cybercrime group is actively recruiting women on public channels to conduct voice phishing attacks.
- High Incentives: Recruits are offered $500 to $1,000 per call and are provided with pre-written scripts to target IT help desks.
- Threat Actor Profile: SLH is a notorious "supergroup" formed by an alliance of Lapsus$, Scattered Spider, and ShinyHunters, known for high-profile corporate breaches.
The Scattered Lapsus$ Hunters (SLH) cybercrime collective has launched a new recruitment campaign specifically targeting women for upcoming voice phishing (vishing) operations. This tactical evolution signals a calculated effort to diversify the group's social engineering tactics.
By seeking female voices, SLH likely aims to circumvent security training that profiles attackers, thereby increasing the success rate of their impersonation attempts against corporate targets.
Vishing Attacks on IT Help Desks
The SLH vishing campaign is designed to exploit a common vulnerability: the human element in IT support. The group is offering significant financial incentives, paying recruits up to $1,000 upfront for each call made, as Dataminr observed on a public Telegram board on February 22, 2026.
These recruits are armed with detailed scripts, likely to convincingly impersonate employees in need of assistance, typically to reset passwords or bypass multi-factor authentication (MFA).
As seen in previous incidents, the primary targets of these vishing attacks on IT help desks are employees who can grant initial network access, which SLH can then leverage for broader infiltration and data exfiltration.
Escalating Cybersecurity Threats in 2026
The Scattered Lapsus$ Hunters, an alliance of some of the most aggressive threat actors, and its members have a well-documented history of successfully breaching major global corporations. Their known tactics include MFA fatigue bombing and SIM swapping.
Security organizations are urged to:
- Update their help desk training to address this specific threat.
- Enforce stricter out-of-band identity verification for sensitive requests.
- Harden MFA policies to resist social engineering.
- Monitor anomalous access.
Earlier this month, a Mandiant report outlined how the ShinyHunters extortion tactics, vishing, and SSO compromise target cloud environments. In January, security researchers observed an alleged ShinyHunters vishing campaign targeting Okta SSO accounts via custom Phishing-as-a-Service kits.